
What's New in InsightVM: Q3 2021 in Review
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C

In today’s post, we’re giving a rundown of new features and functionality launched in Q3 2021 for InsightVM and the Insight Platform. We hope you can begin to leverage these changes to drive success across your organization.
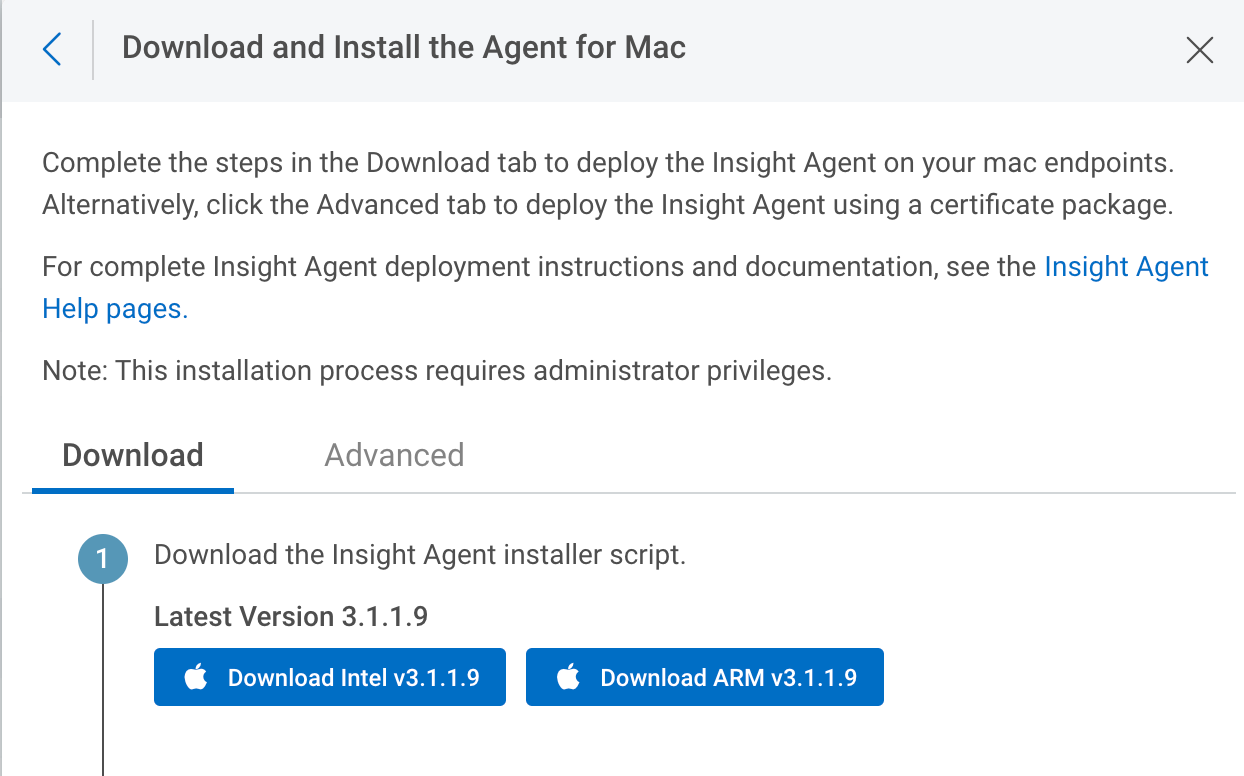
Apple Silicon support on the Insight Agent
We’re excited to announce that the Insight Agent now natively supports Apple Silicon chips!
Apple announced the first generation Apple Silicon chip — the M1 processor — in November 2020. This chip is the new standard on all MacBooks starting with the 2020 releases, and Apple plans to transition completely to Apple Silicon chips over the next two years.
The new Mac installer specifically designed for the Apple Silicon can be accessed right from Agent Management in the platform, in the download section. Learn more in our Apple Silicon Agent Support blog post.
Asset and Vulnerability Details reports
This new feature allows you to easily communicate details of your assets and vulnerabilities with stakeholders in a PDF format. Simply click the Export to PDFbutton on the Vulnerability Details page, and you’ll have a PDF ready to share!
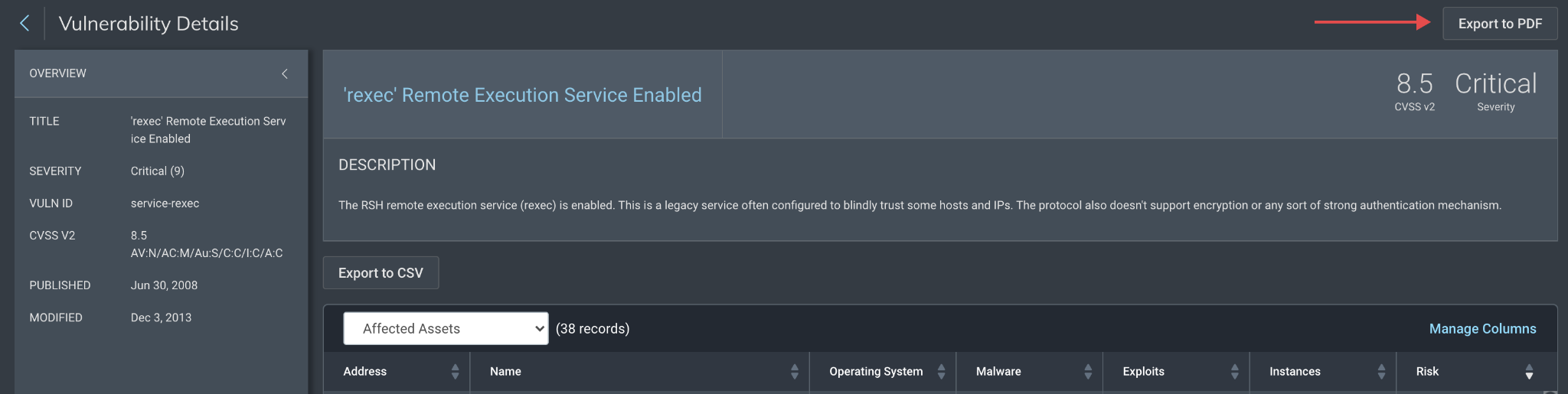
This is particularly useful if you’re attempting to collaborate while remediating a specific vulnerability. We’ll use a hypothetical security engineer named Jane to illustrate this.
Jane recently read about a new ransomware strain that leverages a specific vulnerability as part of an attack chain that seems to be targeting the industry of her organization. She opens the query builder in InsightVM, constructs a search query to identify the vulnerability by CVE, and discovers several instances. She wants to mention this during her morning all-hands sync so she can recruit other team members to her effort. She exports the vulnerability details page to a PDF, which allows her to share this out and provide more details to interested team members, who then can help her remediate this vulnerability much more quickly.
Moreover, while undertaking this effort, another team member — Bill — finds an asset that seems to be a complete tragedy in terms of patching and vulnerability prevalence. He creates the Asset Details report and shares this in an e-mail to his team, stating that this asset seems to be missing their organization’s patch cycle. He also suggests that they look for more of these types of assets because he knows that when there is one offender, there are often many.
Snyk integration for reporting vulnerabilities
Container Security assessments will now report Ruby vulnerabilities through an integration with the Snyk vulnerability database. This adds RubyGems packages to our Snyk-based coverage, which currently includes vulnerability detections for Java, JavaScript, and Python libraries. This integration is particularly helpful for organizations that perform scanning of Container Images at rest, in both public and private registries.
Emergent threat coverage recap
Q3 2021 was another busy quarter for high-priority cybersecurity threats. As part of our emergent threat response process, Rapid7’s VRM research and engineering teams released vulnerability checks and in-depth technical analysis to help InsightVM customers understand the risk of exploitation and assess their exposure to critical security threats. In July, CVE-2021-34527, dubbed “PrintNightmare" presented remediation challenges for many organizations amid active exploitation of the Windows Print Spooler service. In August, the ProxyShell exploit chain put on-premises instances of Microsoft Exchange Server at risk for remote code execution. More recently, widespread attacks took advantage of CVE-2021-26084, a critical flaw in Confluence Server & Confluence Data Center, to deploy cryptominers, exfiltrate data, and obtain initial access for ransomware operations.
Other notable emergent threats included:
- ForgeRock Access Manager/OpenAM Pre-Auth Remote Code Execution Vulnerability (CVE-2021-35464)
- SolarWinds Serv-U FTP and Managed File Transfer (CVE-2021-35211)
- Microsoft SAM File Readability (CVE-2021-36934)
- PetitPotam: Novel Attack Chain
- Zoho ManageEngine ADSelfService Plus (CVE-2021-40539)
- Critical vCenter Server File Upload Vulnerability (CVE-2021-22005)
Stay tuned!
As always, we’re continuing to work on exciting product enhancements and releases throughout the year. Keep an eye on our blog and release notes as we continue to highlight the latest in vulnerability management at Rapid7.
NEVER MISS A BLOG
Get the latest stories, expertise, and news about security today.
Subscribe
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C