
Threat Actors are actively exploiting a SolarWinds Zero-Day Vulnerability
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
THREAT LEVEL: Amber.
For a detailed advisory, download the pdf file here.
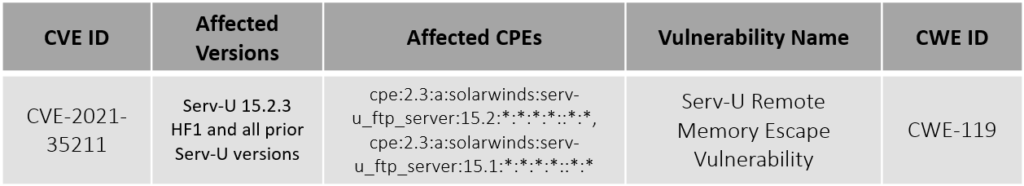
A zero-day vulnerability (CVE-2021-35211) that impacts the Serv-U Managed File Transfer and Serv-U Secure FTP, is been exploited by multiple threat actors. The PoC of this exploited vulnerability was given to SolarWinds by Microsoft. SolarWinds has released a patch for the same.
Vulnerability Details
Indicator of Compromise
| Type | Value |
|---|---|
| IP Address | 98.176.196.89 |
| 68.235.178.32 | |
| 208.113.35.58 |
Patch Link
<https://www.solarwinds.com/trust-center/security-advisories/cve-2021-35211>
References
<https://thehackernews.com/2021/07/a-new-critical-solarwinds-zero-day.html>
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C