Zero-Day Vulnerability Month, new Vulners events and malware

There are many zero-day vulnerabilities this month that were only recently patched. Most helpful tools and news. We also decided to add a section on what's new for Vulners this month.
- Vulners events: Our strongest vulnerability database, which is convenient to work with, is regularly updated and gets better;
- Vulnerabilities: Google is updating its zero-days non-stop, Nvidia is not lagging behind, and the rest is important to know and regularly update;
- Tools: Android tools for attack / defense and others;
- News: Based on the news and the number of botnet-based ransomware in this review, all these groups are gaining ground;
- Research: Regular personal observations of the author with the most useful research.
Really short feedback -> here
Vulners events
Vulners team updated/added the following robots this month:
- [Oracle](https://vulners.com/search?query=order:published AND type:Oracle) (fixed);
- [Broadcom](https://vulners.com/search?query=order:published AND type:Broadcom) (fixed);
- [Symantec](https://vulners.com/search?query=order:published AND type:Symantec) (fixed);
- [nextcloud](https://vulners.com/search?query=order:published AND type:nextcloud) (fixed);
- [slackware](https://vulners.com/search?query=order:published AND type:slackware) (fixed);
- [Nvidia](https://vulners.com/search?query=order:published AND type:Nvidia) (new);
- [attackerkb](https://vulners.com/search?query=order:published AND type:attackerkb) (fixed);
- [Github](https://vulners.com/search?query=order:published AND type:Github) (fixed);
- [Opera](https://vulners.com/search?query=order:published AND type:Opera) (fixed);
- [typo3](https://vulners.com/search?query=order:published AND type:typo3) (fixed);
- [sslabuse](https://vulners.com/search?query=order:published AND type:sslabuse) (fixed).
Some of the vendors only update their bulletins and do not post new ones. Our database is constantly updated with new information. Total robots: 137
Also, we updated to the latest version of ElasticSearch 7.10, check in our post: Vulners updated ElasticSearch 7.10 - what changes for you?
Vulnerabilities

Microsoft released a November security update.
112 vulnerabilities were closed, of which 17 are critical. Exploiting 24 errors leads to Remote Code Execution (RCE), including in Excel, Sharepoint, Exchange Server, and more.
The first critical vulnerability, CVE-2020-17087, which is about buffer overflow in Windows kernel, is 0-day and allows local privileges escalation. Error was found by Google's Project Zero team late last month along with 0-day vulnerability in Chrome leading to RCE. And exploitation of both of these vulnerabilities was found in wilderness.
The second critical vulnerability with almost nothing written in news - CVE-2020-17051. This vulnerability is most dangerous in this update with CVSS 9.8 score. Microsoft describes CVE-2020-17051 as a remote code execution vulnerability affecting Windows network file system. At the time of this description, there is little information about this vulnerability, but Microsoft noted that it has low operational complexity. At the moment, it is unknown how to exploit this vulnerability in the wild.
https://vulners.com/rapid7blog/RAPID7BLOG:5C1C01CE46935D3FDB62B946B79E9801
https://vulners.com/krebs/KREBS:613A537780BD40A6F8E0047CE8D3E6EC

SAD DNS
A group of researchers from the University of Tsinghua and the University of California at Riverside developed a new type of attack CVE-2020-25705, which allows for the substitution of dummy data in the cache of DNS-server, which can be used to spoof the IP address of an arbitrary domain and redirect requests to the domain to the server of the attacker.
The attack allows bypassing the protection added to DNS servers to block the classic method of cache poisoning DNS, proposed in 2008 by Dan Kaminsky.
https://vulners.com/thn/THN:2C912D2A2005BA770BBD4A4975BD3518
Fourth and fifth zero day vulnerability in Chrome, fixed by Google for last month: CVE-2020-16013 and CVE-2020-16017.
One of them is contained in V8 (JavaScript) and the other in the Chrome component responsible for isolating these sites from each other. Google does not provide other technical details yet. Error information, as described, was obtained from anonymous sources.
During half a month Google closed five 0-day vulnerabilities in Chrome, some of which were exploited by hackers in the wild.
https://vulners.com/thn/THN:B62D46980D8C942D94FCDBF0A5899352
Another vulnerability in Chrome detected on Tianfu Cup is being tracked as CVE-2020-16016. Google describes it as incorrect implementation in base component. Company engineers fixed bug update for Chrome 86, which was released earlier this week.

Cisco disclosed details of AnyConnect Secure Mobility Client vulnerability in its secure mobile access client allowing remote code execution. PoC exploit is already available for vulnerability, but Cisco is still working on fixing it. According to Cisco Product Security Incident Response Team, cybercriminals are not yet using the vulnerability in their attacks.

Nvidia is red-flagging a high-severity flaw in its GeForce NOW application software for Windows. An attacker on a local network can exploit the flaw in order to execute code or gain escalated privileges on affected devices.
GeForce NOW is the brand used by Nvidia for its cloud-based gaming service, which enables real-time gameplay on desktops, laptops, Macs and Android devices. With an estimated user base of 4 million, the service is wildly popular in the gaming community.
In a Tuesday security advisory, Nvidia revealed a flaw in the popular service CVE-2020-5992 that has a CVSS score of 7.3.

Details of three vulnerabilities in Acronis products appeared, allowing unprivileged users to run code with SYSTEM rights:
- CVE-2020-10138
- CVE-2020-10139
- CVE-2020-10140
Fixes was released, so it is recommended that everyone update immediately!

Security researcher from GitHub identified a vulnerability CVE-2020-16125 in GDM (GNOME Display Manager) responsible for login screen output. Combined with other vulnerability in account tracking service (accounts-daemon) the problem allows to execute code with root rights. The vulnerability was fixed in GNOME 3.36.2 and 3.38.2. Exploitation of the vulnerability confirmed in Ubuntu and derivatives.
Demonstration: https://www.youtube.com/watch?v=8IjTq7GBupw
Tools
OpenEDR for Windows is a free and open source platform which allows you to analyze what’s happening across your entire environment at base-security-event level. The agent records all telemetry information locally and will send the data to locally hosted or cloud hosted ElasticSeach deployments.
https://github.com/ComodoSecurity/openedr
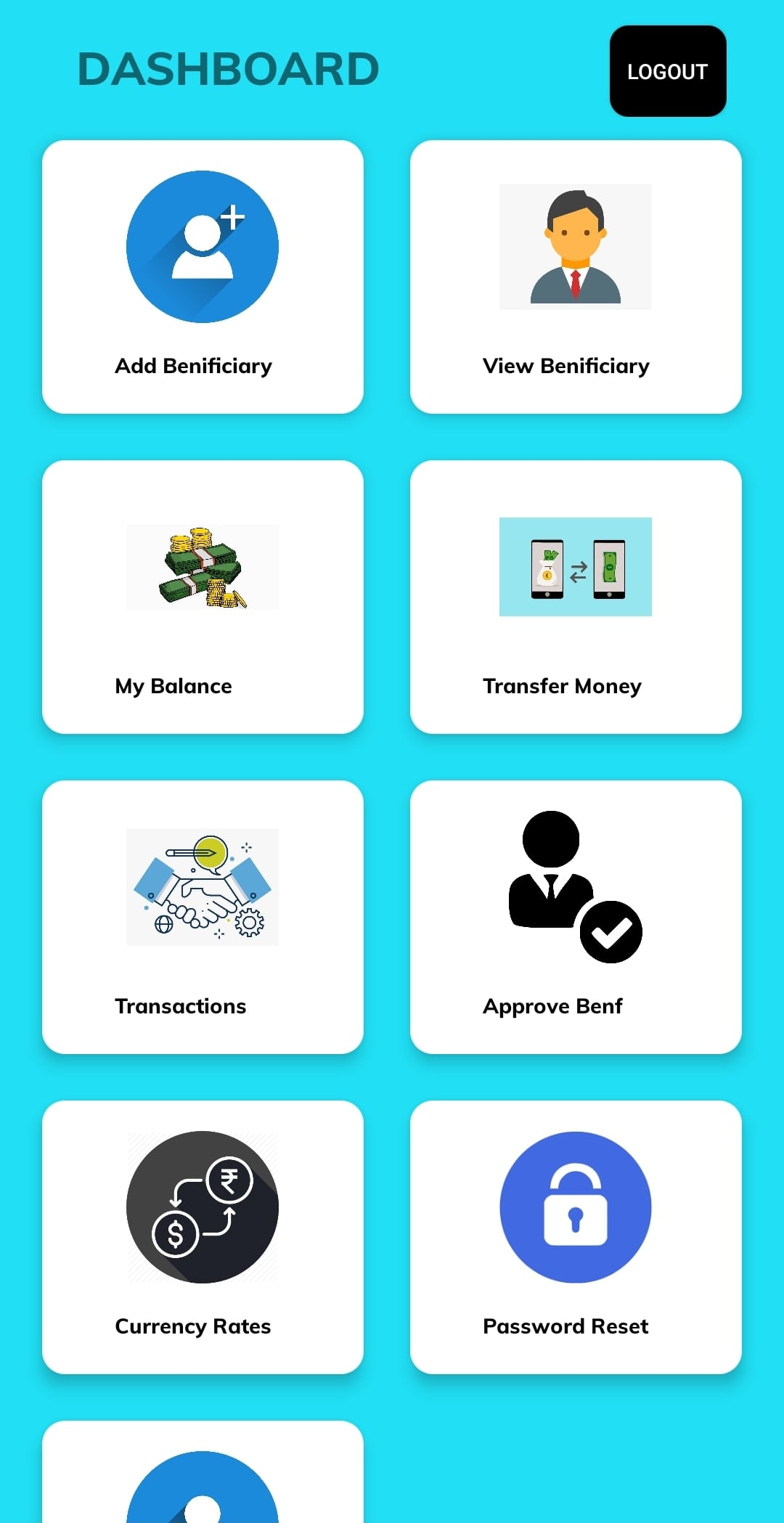
Damn Vulnerable Bank Android Application aims to provide an interface for everyone to get a detailed understanding with internals and security aspects of android application.
https://github.com/rewanth1997/Damn-Vulnerable-Bank
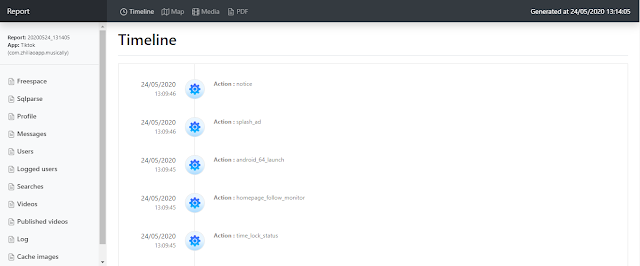
LabCIF
Forensic Analysis for Mobile Apps. Android extraction and analysis framework with an integrated Autopsy Module. Dump easily user data from a device and generate powerful reports for Autopsy or external applications.
https://vulners.com/kitploit/KITPLOIT:2282509672650905891

A curated list of Android Security materials and resources For Pentesters and Bug Hunters.
https://vulners.com/kitploit/KITPLOIT:249292095984323465

**Linux evil toolkit
**It is a framework that aims to centralize, standardize and simplify the use of various security tools for pentest professionals.
https://vulners.com/kitploit/KITPLOIT:1898409887489738477
News

Ransomware operators use malicious ads to distribute fake Microsoft Teams updates, infect systems with backdoors, and then install Cobalt Strike beacons to compromise the network.
In most cases, the original payload was the Predator the Thief infostiller, which sends sensitive information such as credentials, browser data, and financial information to the attacker, Microsoft said. Other programs distributed in this way include the Bladabindi backdoor (NJRat) and the ZLoader info-stealer.
The malware also downloaded Cobalt Strike beacons, allowing an attacker to perform lateral movement across the network. In some attacks, the final stage was the launch of malware to encrypt files on computers on the network.
https://vulners.com/threatpost/THREATPOST:090BB8078666F06CFF081E0E945AC9B9

Continuing the history of Compari company hacked by RagnarLocker encryptor. Recall that this company is a world-renowned manufacturer of various alcoholic beverages. This week, hackers gained access to the Facebook account of DJ Chris Hodson and paid $500 for an advertising campaign in the social network, during which they distributed a statement about the break-in of Campari. They confirmed that they had stolen more than 2 TB of confidential data. In total, more than 7 thousand people watched ransomware advertisements.
https://vulners.com/krebs/KREBS:30CD884948D0098CF8B20012CC34F0BE
Pharmaceutical giant Dr Reddy's was forced to shut down all of its data center servers around the world for an entire day after being attacked. The cyberattack came just days after the company received approval from the Drugs Controller General of India, (DCGI) to conduct clinical trials of the Russian Sputnik V vaccine in the country.
According to a source from ETNow, the attackers used ransomware during the attack, as a result of which the company had to “isolate” all its data centers and halted production at factories in the US, UK, Brazil, India and Russia.
https://vulners.com/threatpost/THREATPOST:7C58B02273B2AC6A34850CCB69E8F050
Children's resource Animal Jam has been hacked. There were 46,000,000 records affected.
The media reported that Animal Jam's online "playground" targeted at children ages 7-11 was cracked. A total of 46,000,000 users have already published information on the darknet.
https://vulners.com/threatpost/THREATPOST:DD290F09D6F45B65685FA49A30BF6199
Juniper Threat Labs security researchers discovered a new botnet called Gitpaste-12. The malware uses the GitHub and Pastebin platforms to host component code and uses 12 different ways to compromise systems.
Experts detected the first Gitpaste-12 attacks on October 15, 2020, but the malware itself was detected on GitHub as early as July 9. The operators of Gitpaste-12 mainly attacked x86 servers based on Linux and IoT devices based on Linux ARM and MIPS processors.
The researchers found a script with comments in Chinese and commands to disable some security tools. In one case, the commands disable cloud security agents, indicating that cyber criminals intended to attack the public cloud infrastructure provided by Alibaba Cloud and Tencent.
https://vulners.com/threatpost/THREATPOST:7B2EAFA107D335014D553D78946C453E
Research
https://twitter.com/\_wald0/status/1327339539782897664?s=20
Password reset privilege cheat sheet for Azure AD
Hunting Emotet with Brim and Zeek: https://medium.com/brim-securitys-knowledge-funnel/hunting-emotet-with-brim-and-zeek-1000c2f5c1ff
New Version of the Microsoft Research Security Update Guide adds CVSS! Didn’t take that long… also, adds Dark-mode (more importantly):
https://msrc-blog.microsoft.com/2020/11/09/vulnerability-descriptions-in-the-new-version-of-the-security-update-guide
This is part one of a four-part series about measuring security at a startup. Some nice ideas that can work anywhere: https://medium.com/@theporkskewer/this-is-part-one-of-a-four-part-series-about-measuring-security-at-a-startup-64964365ae25
Using Active Directory Replication Metadata for hunting purposes: https://security-tzu.com/2020/11/09/active-directory-replication-metadata-for-forensics-purposes
2020 Q4 OSCP writeup: https://medium.com/@nmappn/journey-to-oscp-2020-pwk-693690cdc218
Really short feedback -> here
