
Microsoft Patches 17-Year-Old Office Bug
0.974 High
EPSS
Percentile
99.9%
Microsoft on Tuesday patched a 17-year-old remote code execution bug found in an Office executable called Microsoft Equation Editor. The vulnerability (CVE-2017-11882) was patched as part of Microsoft’s November Patch Tuesday release of 53 fixes.
While Microsoft rates the vulnerability only as “Important” in severity, researchers at Embedi who found the bug, call it “extremely dangerous.”
In a report released Tuesday (PDF) by Embedi, researchers argue the vulnerability is a threat because all version of Microsoft Office for the past 17 years are vulnerable and that the CVE “works with all the Microsoft Windows versions (including Microsoft Windows 10 Creators Update).”
The Microsoft Equation Editor is installed by default with the Office suite. The application is used to insert and edit complex equations as Object Linking and Embedding (OLE) items in Microsoft Word documents.
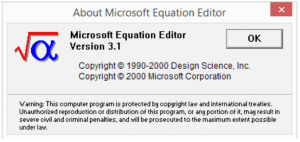
The origins of Equation Editor date back to November 2000 when it was compiled. Since then, it has been part of Office 2000 through Office 2003. Researchers said in 2007 the component was replaced with a newer version. But, the old Equation Editor was left in Office to support files that utilized the old OLE-based (EQNEDT32.EXE) equations.
Further analysis by Embedi revealed that the EQNEDT32.EXE was unsafe because when executed, it ran outside of Office and didn’t benefit from many of the Microsoft Windows 10 and Office security features such as Control Flow Guard.
“The component is an OutProc COM server executed in a separate address space. This means that security mechanisms and policies of the office processes (e.g. WINWORD.EXE, EXCEL.EXE, etc.) do not affect exploitation of the vulnerability in any way, which provides an attacker with a wide array of possibilities,” Embedi wrote in its technical write-up.
 Embedi researchers discovered the error using Microsoft’s own BinScope tool, which identified EQNEDT32.EXE as a vulnerable executable. BinScope works by analyzing files to see if they pass standards set by Microsoft’s Security Development Lifecycle, a core element of Microsoft’s Trustworthy Computing.
Embedi researchers discovered the error using Microsoft’s own BinScope tool, which identified EQNEDT32.EXE as a vulnerable executable. BinScope works by analyzing files to see if they pass standards set by Microsoft’s Security Development Lifecycle, a core element of Microsoft’s Trustworthy Computing.
Embedi exploited this vulnerability using two buffer overflows that relied on several OLEs. “By inserting several OLEs that exploited the described vulnerability, it was possible to execute an arbitrary sequence of commands (e.g. to download an arbitrary file from the Internet and execute it),” researchers said.
Microsoft describes the CVE-2017-11882 as a Microsoft Office memory corruption vulnerability. “Exploitation of the vulnerability requires that a user open a specially crafted file with an affected version of Microsoft Office or Microsoft WordPad software. In an email attack scenario, an attacker could exploit the vulnerability by sending the specially crafted file to the user and convincing the user to open the file,” Microsoft wrote.
As part of its research, Embedi created a proof-of-concept exploit that attacks all versions of Office dating back to 2000, including Office 365, running on Windows 7, Windows 8.1, and the Windows 10 Creators Update. In a video below, Embedi shows three different attacks on Office and Windows versions (Office 2010 on Windows 7, Office 2013 on Windows 8.1, and Office 2016 on Windows 10).
Along with downloading the patch to fix Equation Editor, Embedi is recommending companies disable EQNEDT32.EXE in the Windows registry to prevent further exploitation.
“Because the component has numerous security issues and the vulnerabilities it contains can be easily exploited, the best option for a user to ensure security is to disable registering of the component in Windows registry,” researchers wrote.
References
cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-11882
embedi.com/files/white-papers/skeleton-in-the-closet.pdf
media.threatpost.com/wp-content/uploads/sites/103/2017/11/06222113/Equation-Editor.png
portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2017-11882#ID0EWIAC
portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2017-11884
threatpost.com/microsoft-patches-20-critical-vulnerabilities/128891/