U.S. Imposes New Sanctions on Iran Over Cyberattack on Albania
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P
The U.S. Treasury Department on Friday announced sanctions against Iran’s Ministry of Intelligence and Security (MOIS) and its Minister of Intelligence, Esmaeil Khatib, for engaging in cyber-enabled activities against the nation and its allies.
“Since at least 2007, the MOIS and its cyber actor proxies have conducted malicious cyber operations targeting a range of government and private-sector organizations around the world and across various critical infrastructure sectors,” the Treasury said.
The agency also accused Iranian state-sponsored actors of staging disruptive attacks aimed at Albanian government computer systems in mid-July 2022, an incident that forced the latter to temporarily suspend its online services.
The development comes months nearly nine months after the U.S. Cyber Command characterized the advanced persistent threat (APT) known as MuddyWater as a subordinate element within MOIS. It also comes almost two years following the Treasury’s sanctions against another Iranian APT group dubbed APT39 (aka Chafer or Radio Serpens).
Friday’s sanctions effectively prohibit U.S. businesses and citizens from engaging in transactions with MOIS and Khatib, and non-U.S. citizens that engage in transactions with the designated entities may themselves be exposed to sanctions.
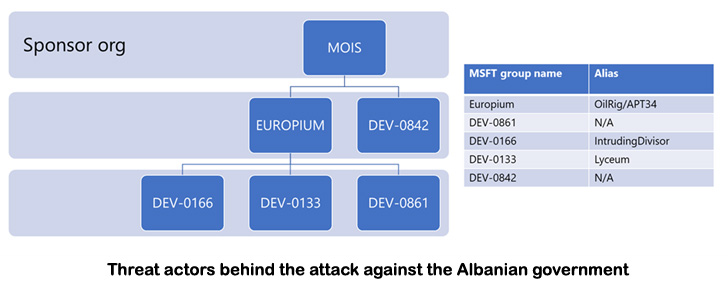
Coinciding with the economic blockade, the Albanian government said the cyberattack on the digital infrastructure was “orchestrated and sponsored by the Islamic Republic of Iran through the engagement of four groups that enacted the aggression.”
Microsoft, which investigated the attacks, said the adversaries worked in tandem to carry out distinct phases of the attacks, with each cluster responsible for a different aspect of the operation -
- DEV-0842 deployed the ransomware and wiper malware
- DEV-0861 gained initial access and exfiltrated data
- DEV-0166 (aka IntrudingDivisor) exfiltrated data, and
- DEV-0133 (aka Lyceum or Siamese Kitten) probed victim infrastructure
The tech giant’s threat intelligence teams also attributed the groups involved in gaining initial access and exfiltrating data to the Iranian MOIS-linked hacking collective codenamed Europium, which is also known as APT34, Cobalt Gypsy, Helix Kitten, or OilRig.
“The attackers responsible for the intrusion and exfiltration of data used tools previously used by other known Iranian attackers,” it said in a technical deepdive. “The attackers responsible for the intrusion and exfiltration of data targeted other sectors and countries that are consistent with Iranian interests.”
“The Iranian sponsored attempt at destruction had less than a 10% total impact on the customer environment,” the company noted, adding the post-exploitation actions involved the use of web shells for persistence, unknown executables for reconnaissance, credential harvesting techniques, and defense evasion methods to turn off security products.
Microsoft’s findings dovetail with previous analysis from Google’s Mandiant, which called the politically motivated activity a “geographic expansion of Iranian disruptive cyber operations.”
Initial access to the network of an Albanian government victim is said to have occurred as early as May 2021 via successful exploitation of a SharePoint remote code execution flaw (CVE-2019-0604), followed by exfiltration of email from the compromised network between October 2021 and January 2022.
A second, parallel wave of email harvesting was observed between November 2021 and May 2022, likely through a tool called Jason. On top of that, the intrusions entailed the deployment of a ransomware strain called ROADSWEEP and the distribution of a wiper malware referred to as ZeroCleare.
Microsoft characterized the destructive campaign as a “form of direct and proportional retaliation” for a string of cyberattacks on Iran, including one staged by an Iranian hacktivist group that’s affiliated to Mujahedin-e-Khalq (MEK) in the first week of July 2022.
The MEK, also known as the People’s Mujahedin Organization of Iran (PMOI), is an Iranian dissident group largely based in Albania that seeks to overthrow the government of the Islamic Republic of Iran and install its own government.
“Some of the Albanian organizations targeted in the destructive attack were the equivalent organizations and government agencies in Iran that experienced prior cyberattacks with MEK-related messaging,” the Windows maker said.
Iran’s Foreign Ministry, however, has rejected accusations that the country was behind the digital offensive on Albania, calling them “baseless” and that it’s “part of responsible international efforts to deal with the threat of cyberattacks.”
It further condemned the sanctions and called the act based on “false and unproven” accusations, stating it “will use all its capabilities within the framework of international law to uphold the Iranians’ rights and defend itself against these sinister conspiracies.” The Ministry also accused the U.S. of “giving full support to a terrorist sect”, referring to MEK.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P