Palo Alto Warns of Zero-Day Bug in Firewalls Using GlobalProtect Portal VPN
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
A new zero-day vulnerability has been disclosed in Palo Alto Networks GlobalProtect VPN that could be abused by an unauthenticated network-based attacker to execute arbitrary code on affected devices with root user privileges.
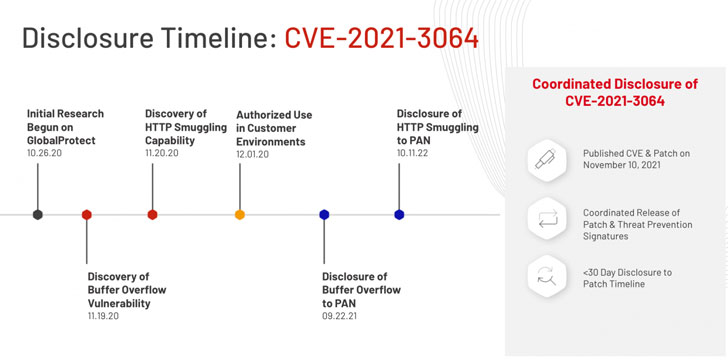
Tracked as CVE-2021-3064 (CVSS score: 9.8), the security weakness impacts PAN-OS 8.1 versions earlier than PAN-OS 8.1.17. Massachusetts-based cybersecurity firm Randori has been credited with discovering and reporting the issue.
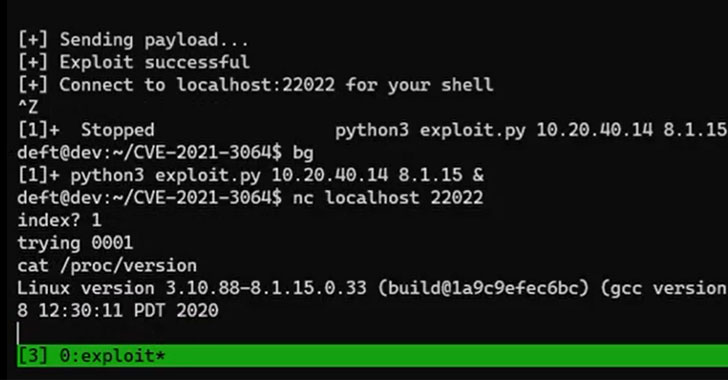
“The vulnerability chain consists of a method for bypassing validations made by an external web server (HTTP smuggling) and a stack-based buffer overflow,” Randori researchers said. “Exploitation of the vulnerability chain has been proven and allows for remote code execution on both physical and virtual firewall products.”
However, in a troubling turn of events, the company said it used this exploit as part of its red team engagements for nearly 10 months before disclosing it to Palo Alto Networks in late September 2021. Technical details related to CVE-2021-3064 have been withheld for 30 days to prevent threat actors from abusing the vulnerability to stage real-world attacks.
The security bug stems from a buffer overflow that occurs while parsing user-supplied input. Successful exploitation of the flaw necessitates that the attacker strings it with a technique known as HTTP smuggling to achieve remote code execution on the VPN installations, not to mention have network access to the device on the GlobalProtect service default port 443.
“A memory corruption vulnerability exists in Palo Alto Networks GlobalProtect portal and gateway interfaces that enables an unauthenticated network-based attacker to disrupt system processes and potentially execute arbitrary code with root privileges,” Palo Alto Networks said in an independent advisory. “The attacker must have network access to the GlobalProtect interface to exploit this issue.”
In light of the fact that VPN devices are lucrative targets for malicious actors, it’s highly recommended that users move quickly to patch the vulnerability. As a workaround, Palo Alto Networks is advising affected organizations to enable threat signatures for identifiers 91820 and 91855 on traffic destined for GlobalProtect portal and gateway interfaces to prevent any potential attacks against CVE-2021-3064.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C