
Metasploit Wrap-Up
Commemorating the 2020 December Metasploit community CTF

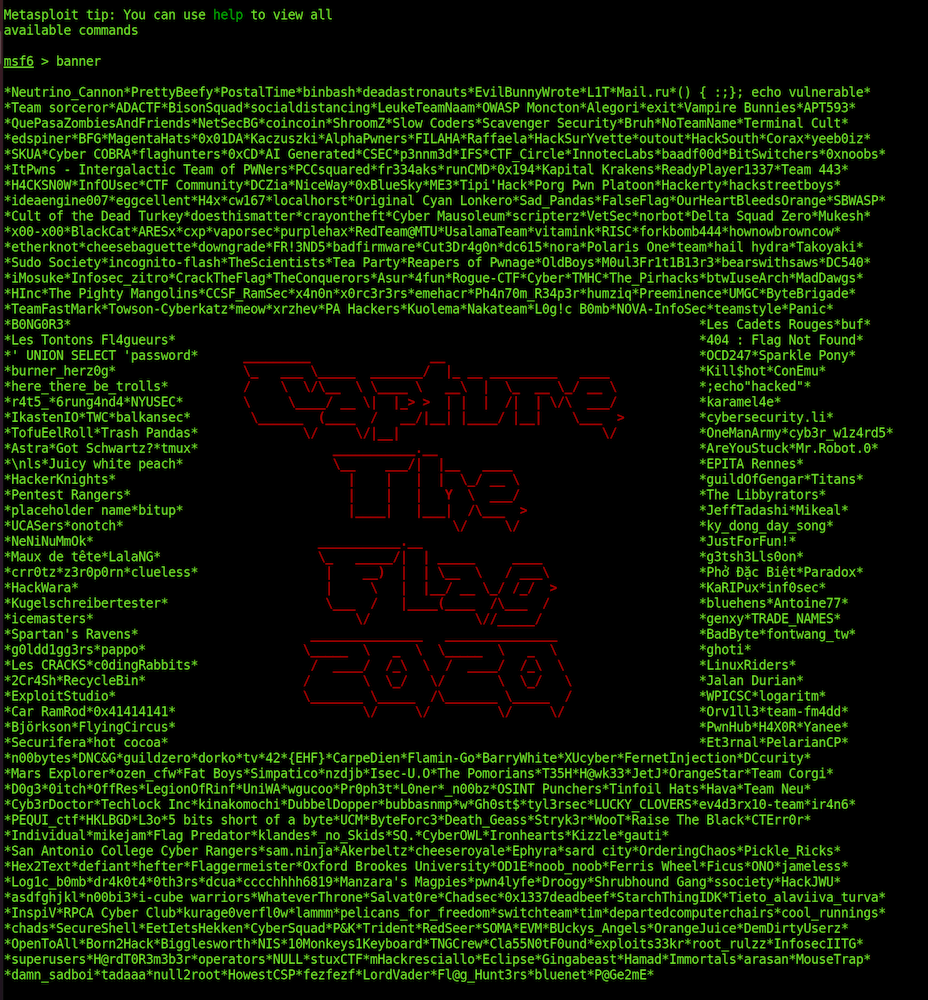
A new commemorative banner has been added to the Metasploit console to celebrate the teams that participated in the 2020 December Metasploit community CTF and achieved 100 or more points:
If you missed out on participating in this most recent event, be sure to follow the Metasploit Twitter and Metasploit blog posts. If there are any future Metasploit CTF events, all details will be announced there!
If the banners aren’t quite your style, you can always disable them with the quiet flag:
msfconsole -q
Windows privilege escalation via Cloud Filter driver
Our very own gwillcox-r7 has created a new module for CVE-2020-1170 Cloud Filter Arbitrary File Creation EOP, with credit to James Foreshaw for the initial vulnerability discovery and proof of concept. The Cloud Filter driver, cldflt.sys, on Windows 10 v1803 and later, prior to December 2020, did not set the IO_FORCE_ACCESS_CHECK or OBJ_FORCE_ACCESS_CHECK flags when calling FltCreateFileEx() and FltCreateFileEx2() within its HsmpOpCreatePlaceholders() function with attacker-controlled input. This meant that files were created with KernelMode permissions, thereby bypassing any security checks that would otherwise prevent a normal user from being able to create files in directories they don’t have permissions to create files in.
This module abuses this vulnerability to perform a DLL hijacking attack against the Microsoft Storage Spaces SMP service, which grants the attacker code execution as the NETWORK SERVICE user. Users are strongly encouraged to set the PAYLOAD option to one of the Meterpreter payloads, as doing so will allow them to subsequently escalate their new session from NETWORK SERVICE to SYSTEM by using Meterpreter’s getsystem command to perform RPCSS Named Pipe Impersonation and impersonate the SYSTEM user.
New Modules (3)
- WordPress AIT CSV Import Export Unauthenticated Remote Code Execution by h00die This adds an exploit module for various versions of the
AIT CSV Import / Exportplugin for Wordpress. This module exploits an unauthenticated file upload vulnerability in plugin versions belowv3.0.4to gain code execution against Wordpress installations. - CVE-2020-1170 Cloud Filter Arbitrary File Creation EOP by Grant Willcox and James Foreshaw, which exploits CVE-2020-17136, an arbitrary file write vulnerability within cldflt.sys. The result yields local code execution as the Network Service account which is suitable for escalating to SYSTEM via documented techniques.
- Windows Manage Volume Shadow Copies by zeroSteiner This adds the possibility to run post module actions as commands. This also consolidates and improves existing VSS modules into one new single module with multiple actions.
Enhancements and Features
- #14562 from zeroSteiner Improves the readability of Meterpreter error messages by replacing the command ID with the command name
- #14582 from zeroSteiner This adds the possibility to run post module actions as commands. This also consolidates and improves existing VSS modules into one new single module with multiple actions.
- #14600 from zeroSteiner The FileSystem mixin has been reorganized and a number of function aliases have been added to assist developers in using the module. Additionally new YARD documentation has been added to better explain the functionality of several of the FileSystem mixin’s functions to assist developers in determining when to use these functions.
- #14606 from bwatters-r7 This adds a banner commemorating all of the teams that participated in the Q4 2020 CTF.
Bugs Fixed
- #14515 from timwr This fixes an issue with both cmd/unix/reverse_awk and cmd/unix/bind_awk payloads that were not correctly terminating when after a session was closed. This was causing endless session creations and high CPU consumption on the target.
- #14605 from zeroSteiner This PR fixes an issue where the
VHOSToption was not being correctly populated when theRHOSToption was a domain name - #14613 from adfoster-r7 Fixes a regression error with modules depending on NTLM such as cve_2019_0708_bluekeep
- #14614 from zeroSteiner A bug within the module for CVE-2020-17136 occurred where a relative path was used instead of an absolute path when attempting to load the C# exploit exe. The code has been replaced with a call to
File.expand_path()to allow the module to dynamically determine the full path to this file, allowing users to use the module regardless of which directory they are in when runningmsfconsole.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
If you are a git user, you can clone the Metasploit Framework repo (master branch) for the latest. To install fresh without using git, you can use the open-source-only Nightly Installers or the binary installers (which also include the commercial edition).