
September 2022 Patch Tuesday | Microsoft Releases 63 Vulnerabilities with 5 Critical, plus 16 Microsoft Edge (Chromium-Based); Adobe Releases 7 Advisories, 63 Vulnerabilities with 35 Critical.
EPSS
Percentile
99.9%
Microsoft Patch Tuesday Summary
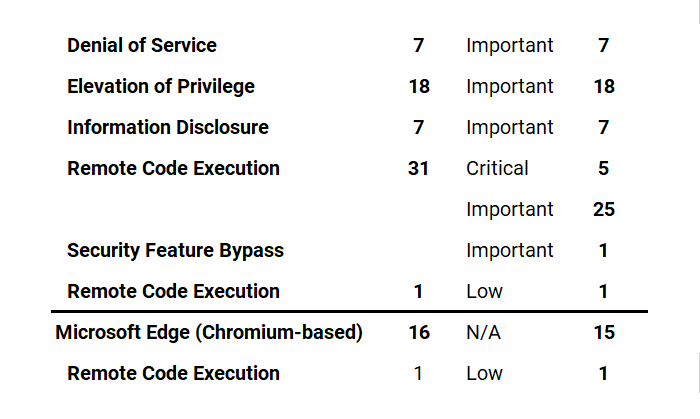
Microsoft has fixed 63 vulnerabilities (aka flaws) in the September 2022 update, including five (5) vulnerabilities classified as Critical as they allow Remote Code Execution (RCE). This month's Patch Tuesday fixes two (2) zero-day vulnerabilities, with one (1) actively exploited***** in attacks (CVE-2022-37969, CVE-2022-23960*). Earlier this month, on September 1-2, 2022, Microsoft also released a total of 16 Microsoft Edge (Chromium-Based) updates, one (1) addressing a Remote Code Execution (RCE) (CVE-2022-38012) ranked Low.
Microsoft has fixed several flaws in its software, including Denial of Service, Elevation of Privilege, Information Disclosure, Microsoft Edge (Chromium-based), Remote Code Execution, and Security Feature Bypass.
The September 2022 Microsoft Vulnerabilities are Classified as follows:
Notable Microsoft Vulnerabilities Patched
CVE-2022-34718 | Windows TCP/IP Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 9.8/10.
An unauthenticated attacker could send a specially crafted IPv6 packet to a Windows node where IPSec is enabled, which could enable a remote code execution exploitation on that machine.
Exploitability Assessment: Exploitation More Likely
CVE-2022-34721, CVE-2022-34722 | Windows Internet Key Exchange (IKE) Protocol Extensions Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 9.8/10.
An unauthenticated attacker could send a specially crafted IP packet to a target machine that is running Windows and has IPSec enabled, which could enable a remote code execution exploitation. NOTE: This vulnerability_ only impacts IKEv1_. IKEv2 is not impacted. However, all Windows Servers are affected because they accept both V1 and V2 packets.
Exploitability Assessment: Exploitation Less Likely
Zero-Day Vulnerabilities Addressed
A vulnerability is classified as a zero-day if it is publicly disclosed or actively exploited with no official fix available.
CVE-2022-37969 | Windows Common Log File System Driver Elevation of Privilege (EoP) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
An attacker must already have access and the ability to run code on the target system. This technique does not allow for remote code execution in cases where the attacker does not already have that ability on the target system.
An attacker who successfully exploited this vulnerability could gain SYSTEM privileges.
Exploitability Assessment: Exploitation More Likely
CVE-2022-23960 | Windows Common Log File System Driver Elevation of Privilege (EoP) Vulnerability
This vulnerability has a CVSSv3.1 score of 5.6/10.
CVE-2022-23960 is regarding a vulnerability known as Spectre-BHB. MITRE created this CVE on behalf of Arm Limited.
Please see Spectre-BHB on arm Developer for more information.
Exploitability Assessment: Exploitation Less Likely
Microsoft Important Vulnerability Highlights
This month’s advisory covers multiple Microsoft product families, including Azure, Browser, Developer Tools, Extended Security Updates (ESU), Microsoft Dynamics, Microsoft Office, System Center, and Windows.
A total of 92 unique Microsoft products/versions are affected, including but not limited to .NET, Azure Arc, Microsoft Dynamics, Microsoft Edge (Chromium-based), Microsoft Office, Microsoft Office SharePoint, SPNEGO Extended Negotiation, Visual Studio Code, Windows Common Log File System Driver, Windows Credential Roaming Service, Windows Defender, Windows Distributed File System (DFS), Windows DPAPI (Data Protection Application Programming Interface), Windows Enterprise App Management, Windows Event Tracing, Windows Group Policy, Windows IKE Extension, Windows Kerberos, Windows Kernel, Windows LDAP - Lightweight Directory Access Protocol, Windows ODBC Driver, Windows OLE, Windows Print Spooler Components, Windows Remote Access Connection Manager, Windows TCP/IP, and Windows Transport Security Layer (TLS).
Downloads include Cumulative Update, Monthly Rollup, Security Hotpatch Update, Security Only, and Security Updates.
CVE-2022-38009 | Microsoft SharePoint Server Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 8.8/10.
In a network-based attack, an authenticated attacker with Manage List permissions could execute code remotely on the SharePoint Server.
The attacker must be authenticated to the target site, with the permission to use Manage Lists within SharePoint.
Exploitability Assessment: Exploitation Less Likely
CVE-2022-26929 | .NET Framework Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally.
For example, when the score indicates that the Attack Vector isLocalandUser InteractionisRequired, this could describe an exploit in which an attacker, through social engineering, convinces a victim to download and open a specially crafted file from a website which leads to a local attack on their computer.
Exploitability Assessment: Exploitation Less Likely
CVE-2022-38007 | Azure Guest Configuration and Azure Arc-enabled Servers Elevation of Privilege (EoP) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
An attacker who successfully exploited the vulnerability could replace Microsoft-shipped code with their own code, which would then be run as root in the context of a Guest Configuration daemon. On an Azure VM with the Guest Configuration Linux Extension installed, this would run in the context of the GC Policy Agent daemon. On an Azure Arc-enabled server, it could run in the context of the GC Arc Service or Extension Service daemons.
Exploitability Assessment: Exploitation Less Likely
Microsoft Edge | Last But Not Least
Earlier in September 2022, Microsoft released Microsoft Edge (Chromium-based) vulnerabilities including CVE-2022-38012. The vulnerability assigned to the CVE is in the Chromium Open Source Software (OSS) which is consumed by Microsoft Edge. It is being documented in the Security Update Guide to announce that the latest version of Microsoft Edge (Chromium-based) is no longer vulnerable. For more information, please see Security Update Guide Supports CVEs Assigned by Industry Partners.
CVE-2022-38012 | Microsoft Edge (Chromium-based) Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.7/10.
The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally.
For example, when the score indicates that the Attack Vector isLocalandUser InteractionisRequired, this could describe an exploit in which an attacker, through social engineering, convinces a victim to download and open a specially crafted file from a website which leads to a local attack on their computer.
This vulnerability could lead to a browser sandbox escape.
Successful exploitation of this vulnerability requires an attacker to take additional actions prior to exploitation to prepare the target environment.
NOTE: Per Microsoft's severity guidelines, the amount of user interaction or preconditions required to allow this sort of exploitation downgraded the severity. The CVSS scoring system doesn't allow for this type of nuance which explains why this CVE is rated as Low, but the CVSSv3.1 score is 7.7
Adobe Security Bulletins and Advisories
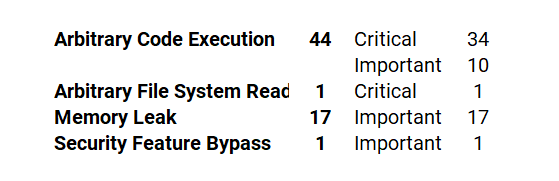
Adobe released seven (7) security bulletins and advisories with updates to fix 63 vulnerabilities affecting Adobe Animate, Bridge, Illustrator, InCopy, InDesign, Photoshop, and Experience Manager applications. Of these 63 vulnerabilities, 35 are rated as Critical and 28 rated as ****Important****; ranging in severity from a CVSS score of 5.3/10 to 7.8/10, as summarized below.
APSB22-40 | Security Update Available for Adobe Experience Manager
This update resolves 11 __****Important**** vulnerabilities.
Adobe has released updates for Adobe Experience Manager (AEM). These updates resolve vulnerabilities rated Important. Successful exploitation of these vulnerabilities could result in arbitrary code execution and security feature bypass.
APSB22-49 | Security Update Available for Adobe Bridge
This update resolves 12 vulnerabilities:
_Adobe Priority: _3
Adobe has released a security update for Adobe Bridge. This update addresses critical and important vulnerabilities that could lead to arbitrary code execution and memory leak.
APSB22-50 | Security Update Available for Adobe InDesign
This update resolves 18 vulnerabilities:
_Adobe Priority: _3
Adobe has released a security update for Adobe InDesign. This update addresses multiple critical and important vulnerabilities. Successful exploitation could lead to arbitrary code execution, arbitrary file system read, and memory leak.
APSB22-52 | Security Update Available for Adobe Photoshop
This update resolves ten (10) vulnerabilities:
Adobe has released an update for Photoshop for Windows and macOS. This update resolves critical and important vulnerabilities. Successful exploitation could lead to arbitrary code execution and memory leak.
APSB22-53 | Security Update Available for Adobe InCopy
This update resolves seven (7) vulnerabilities:
Adobe has released a security update for Adobe InCopy. This update addresses multiple critical and important vulnerabilities. Successful exploitation could lead to arbitrary code execution and memory leak.
APSB22-54 | Security Update Available for Adobe Animate
This update resolves two (2) Critical vulnerabilities.
Adobe has released an update for Adobe Animate. This update resolves critical vulnerabilities. Successful exploitation could lead to arbitrary code execution in the context of the current user.
APSB22-55 | Security Update Available for Adobe Illustrator
This update resolves three (3) vulnerabilities:
Adobe has released an update for Adobe Illustrator 2022. This update resolves critical and important vulnerabilities that could lead to arbitrary code execution and memory leak.
About Qualys Patch Tuesday
Qualys Patch Tuesday QIDs are published as Security Alerts typically late in the evening on the day of Patch Tuesday, followed later by the publication of the monthly queries for the Unified Dashboard: 2022 Patch Tuesday (QID Based) Dashboard by Noon on Wednesday.
Qualys Threat Protection High-Rated Advisories from August to September 2022 Patch Tuesday Advisory
Sorted in Descending Order
- Microsoft Patches Vulnerabilities 79 including 16 Microsoft Edge (Chromium-Based); with 2 Zero-days and 5 Critical in Patch Tuesday September 2022 Edition
- Google Chrome Releases Fix for the Zero-day Vulnerability (CVE-2022-3075)
- Atlassian Bitbucket Server and Data Center Command Injection Vulnerability (CVE-2022-36804)
- GitLab Patches Critical Remote Command Execution Vulnerability (CVE-2022-2884)
- Apple Releases Security Updates to patch two Zero-Day Vulnerabilities (CVE-2022-32893 and CVE-2022-32894)
- Google Chrome Zero-Day Insufficient Input Validation Vulnerability (CVE-2022-2856)
- Palo Alto Networks (PAN-OS) Reflected Amplification Denial-of-Service (DoS) Vulnerability (CVE-2022-0028)
- Microsoft Patches 121 Vulnerabilities with Two Zero-days and 17 Critical; Plus 20 Microsoft Edge (Chromium-Based) in August 2022 Patch Tuesday
- VMware vRealize Operations Multiple Vulnerabilities Patched in the Latest Security update (CVE-2022-31672, CVE-2022-31673, CVE-2022-31674, & CVE-2022-31675)
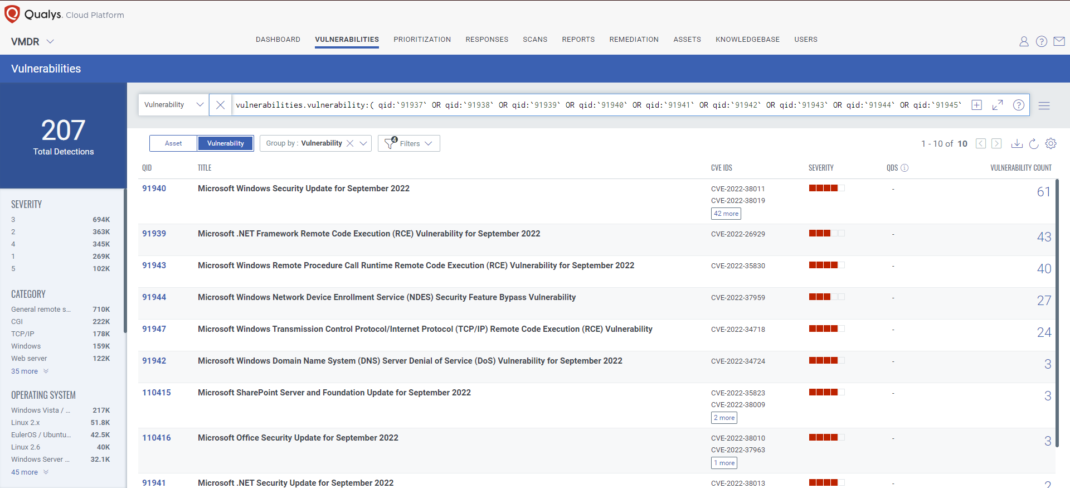
Discover and Prioritize Vulnerabilities in Vulnerability Management Detection Response (VMDR)
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its KnowledgeBase (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability:( qid:`91937` OR qid:`91938` OR qid:`91939` OR qid:`91940` OR qid:`91941` OR qid:`91942` OR qid:`91943` OR qid:`91944` OR qid:`91945` OR qid:`91946` OR qid:`91947` OR qid:`110415` OR qid:`110416` OR qid:`377590` )
 Qualys VMDR Recognized as Best VM Solution by SC Awards 2022 & Leader by GigaOm New
Qualys VMDR Recognized as Best VM Solution by SC Awards 2022 & Leader by GigaOm New
 A Deep Dive into VMDR 2.0 with Qualys TruRisk™
A Deep Dive into VMDR 2.0 with Qualys TruRisk™
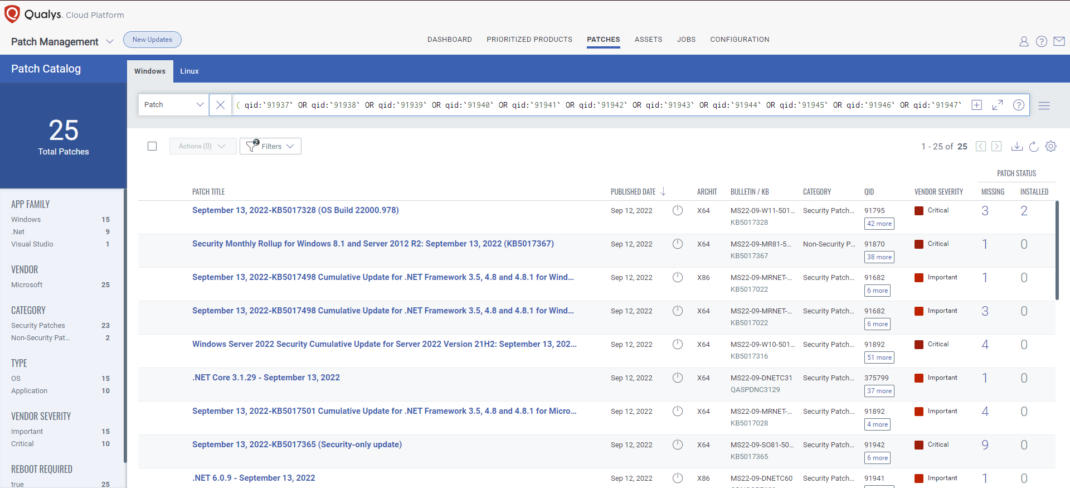
Rapid Response with Patch Management (PM)
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches with one click.
The following QQL will return the missing patches for this Patch Tuesday:
( qid:`91937` OR qid:`91938` OR qid:`91939` OR qid:`91940` OR qid:`91941` OR qid:`91942` OR qid:`91943` OR qid:`91944` OR qid:`91945` OR qid:`91946` OR qid:`91947` OR qid:`110415` OR qid:`110416` OR qid:`377590` )
 Let Smart Automation Reduce the Risk of Zero-Day Attacks on Third-Party Applications New
Let Smart Automation Reduce the Risk of Zero-Day Attacks on Third-Party Applications New
 Risk-based Remediation Powered by Patch Management in Qualys VMDR 2.0
Risk-based Remediation Powered by Patch Management in Qualys VMDR 2.0
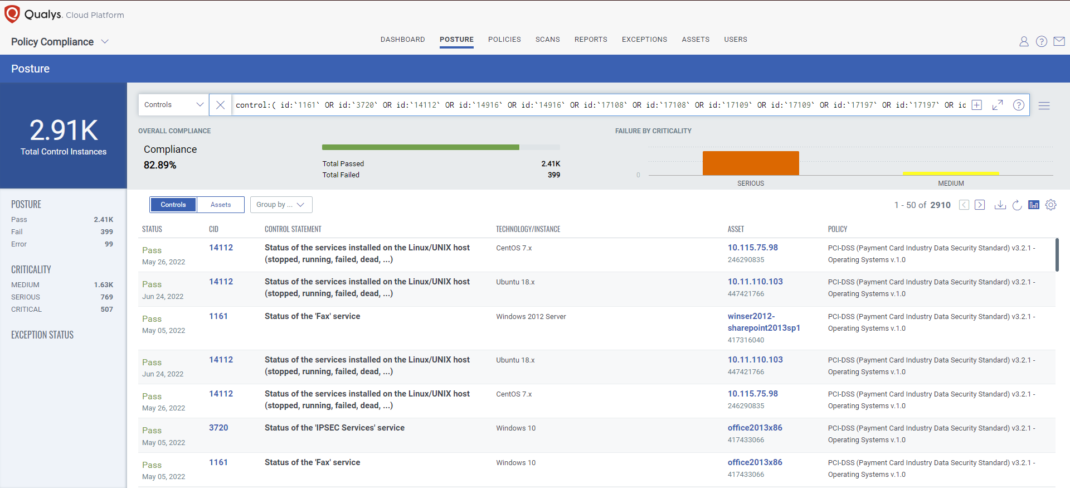
Evaluate Vendor-Suggested Workarounds with Policy Compliance
Qualys’ Policy Compliance Control Library makes it easy to evaluate your technology infrastructure when the current situation requires the implementation of a vendor-suggested workaround. A workaround is a method, sometimes used temporarily, for achieving a task or goal when the usual or planned method isn't working. Information technology often uses a workaround to overcome hardware, programming, or communication problems. Once a problem is fixed, a workaround is usually abandoned. _ Source_
The following Qualys Policy Compliance Control IDs (CIDs), and System Defined Controls (SDC) have been updated to support Microsoft recommended workaround for this Patch Tuesday:
CVE-2022-38007** | Azure Guest Configuration and Azure Arc-enabled Servers Elevation of Privilege (EoP) Vulnerability**
This vulnerability has a CVSSv3.1 score of 7.8/10.
Policy Compliance Control IDs (CIDs) for Checking Azure Arc-Enabled Servers on Linux:
- 14112: Status of the services installed on the Linux/UNIX host (stopped, running, failed, dead, …)
Exploitability Assessment: Exploitation Less Likely
CVE-2022-34718**** |****Windows TCP/IP Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 9.8/10.
Policy Compliance Control IDs (CIDs):
- 3720: Status of the 'IPSEC Services' service
- 14916: Status of Windows Services
Exploitability Assessment: Exploitation More Likely
CVE-2022-35838****** |HTTP V3 Denial of Service (DoS) Vulnerability**
This vulnerability has a CVSSv3.1 score of 7.5/10.
Policy Compliance Control IDs (CIDs):
- 24717: Status of the 'HTTP/3' service
Exploitability Assessment: Exploitation Less Likely
CVE-2022-33679 , CVE-2022-33647**** |Windows Kerberos Elevation of Privilege (EoP) Vulnerability
These vulnerabilities have a CVSSv3.1 score of 8.1/10.
Policy Compliance Control IDs (CIDs):
- 17108: Status of the 'KDC support for claims, compound authentication and Kerberos armoring' setting (Enabled / Disabled)
- 17109: Status of the 'Kerberos client support for claims, compound authentication and Kerberos armoring' setting
- 17197: Status of the 'KDC support for claims, compound authentication, and Kerberos armoring' setting
Exploitability Assessment: Exploitation Less Likely
CVE-2022-38004 | Windows Network File System Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
Policy Compliance Control IDs (CIDs):
- 1161: Status of the 'Fax' service
- 14916: Status of Windows Services
Exploitability Assessment: Exploitation Less Likely
The following QQL will return a posture assessment for the CIDs for this Patch Tuesday:
control:( id:`1161` OR id:`3720` OR id:`14112` OR id:`14916` OR id:`14916` OR id:`17108` OR id:`17108` OR id:`17109` OR id:`17109` OR id:`17197` OR id:`17197` OR id:`24717` )
 Mitigating the Risk of Zero-Day Vulnerabilities by using Compensating Controls New
Mitigating the Risk of Zero-Day Vulnerabilities by using Compensating Controls New
 Policy Compliance (PC) | Policy Library Update Blogs
Policy Compliance (PC) | Policy Library Update Blogs
Patch Tuesday is Complete.
Qualys This Month in Vulnerabilities and Patches Webinar Series

The Qualys Research team hosts a monthly webinar series to help our existing customers leverage the seamless integration between Qualys Vulnerability Management Detection Response (VMDR) and Qualys Patch Management. Combining these two solutions can reduce the median time to remediate critical vulnerabilities.
During the webcast, we will discuss this month’s high-impact vulnerabilities, including those that are part of this month's Patch Tuesday alert. We will walk you through the necessary steps to address the key vulnerabilities using Qualys VMDR and Qualys Patch Management.
Join the webinar
This Month in Vulnerabilities & Patches
NEW & NOTEWORTHY UPCOMING EVENTS
The content within this section will spotlight Vulnerability Management, Patch Management, Threat Protections, and Policy Compliance adjacent events available to our new and existing customers.
Introducing Qualys Threat Thursdays

The Qualys Research Team announces the first in a series of regular monthly webinars covering the latest threat intelligence analysis and insight. Join us each month for Threat Thursdays, where we will zero in on a specific malware or other exploit observed in the wild… and how to defend against it.
Please join us for the first Threat Thursdays monthly webinar where the Qualys Threat Research Team will present the latest threat intelligence… each and every month!
To quickly navigate to Threat Thursday blog posts, please use <https://blog.qualys.com/tag/threat-thursday>
Qualys Annual Security Conference #QSC22
November 7-10, 2022
The Venetian Resort Las Vegas, 3355 Las Vegas Blvd. South, Las Vegas, NV 89109, US
Book your hotel here & take advantage of the discounted QSC rate of $229+ per night
Or find a conference near you.
