
Quantum Security Goes Live with Samsung Galaxy
Samsung and South Korean telecom giant SK Telecom have debuted the Galaxy A Quantum 5G smartphone, sporting a quantum random number generation (RNG) chipset. It’s the first commercialization of quantum technology for mobile phones, and it will serve as a significant bellwether for full quantum encryption’s chances of going mainstream.
Quantum encryption in general has been touted as being “unhackable” because it generates random numbers and secure keys that cannot be predicted, via particles that can’t be intercepted, eavesdropped upon or spoofed. The very laws of physics themselves prevent successful cracking, the theory goes. However, researchers have proven more than once that this isn’t the case—though hacks so far have required sustained physical access to a device.
In any event, the Samsung phone will provide an interesting test case for the technology — though details are scant in terms of how the chipset actually works. The companies did however offer a few comments that point to the use of quantum mechanics and photons to inform its security efforts.
Samsung’s Implementation
The chipset, which measures 2.5 mm by 2.5 mm, was developed by SK Telecom’s Switzerland-based subsidiary ID Quantique.
“The quantum RNG chipset helps smartphone users safely use specific services by generating unpredictable and patternless pure random numbers,” according to the carrier.
The quantum RNG chip has an on-board LED light source that emits photons; it also has a CMOS image sensor to detect the photons being emitted. The image sensor is responsible for receiving the photons, and then generating the random numbers ultimately used to create encryption keys.
These random numbers are provided to compatible services, and are used to generate one-time encryption keys used in each app, the companies said.
In Samsung’s case, the Galaxy will use quantum RNG in a few different scenarios, according to an SK press release (translated with Google Translate). These include logging into carrier accounts on the device; securely storing personal documents via a blockchain-enabled “Quantum Wallet;” and for biometric-based mobile payments at retail stores. Online payment protection is also on the roadmap.
SK Telecom also plans to roll out open APIs for developers to begin incorporating the technology on an OEM and application basis.
The Power of Photons
As for what quantum encryption actually is, the Optical Society explained in an academic article, that it uses photons (light particles) to encode information: Data essentially moves over the air in the form of light, rather than across circuitry as electrical charges.
“In its simplest form, known as 2D encryption, each photon encodes one bit: either a one or a zero. Scientists have shown that a single photon can encode even more information — a concept known as high-dimensional quantum encryption,” the Society explained. “With eight bits necessary to encode just one letter, for example, packing more information into each photon would significantly speed up data transmission.”
Thanks to the principles of quantum mechanics, quantum cryptography has significant advantages from a security standpoint. As QuantumXchange detailed in an online primer, photons can simultaneously exist in more than one place or more than one state of being; they’re generated randomly in one of two quantum states.
While scientists can clone some quantum properties of a particle, cloning an entire particle as proven so far impossible. That’s because one can’t measure or examine a quantum property without changing or disturbing it, meaning that any tampering will render the original photon essentially non-existent (thus thwarting hacking).
“If the photon is read or copied in any way by an eavesdropper, the photon’s state will change,” according to QuantumXchange. “The change will be detected by the endpoints. In other words, this means you cannot read the photon and forward it on or make a copy of it without being detected.”
The Quantum Process
Quantum encryption typically takes place over a fiber-optic cable. The sending apparatus transmits photons through a filter (known as a “polarizer”) which sends the particles out with one of four random, possible polarizations. When the photons reach the receiver, two light-beam splitters “read” the polarization of each photon. However, the receiver does not know which beam splitter to use for each photon and has to guess which one to use.
“Once the stream of photons has been sent, the receiver tells the sender which beam splitter was used for each of the photons in the sequence they were sent, and the sender compares that information with the sequence of polarizers used to send the key,” according to QuantumXchange. “The photons that were read using the wrong beam splitter are discarded, and the resulting sequence of bits becomes the key.”
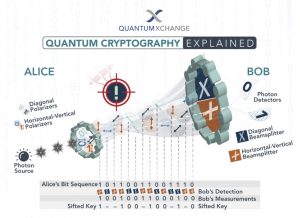
How quantum encryption works. Source: QuantumXchange.
Putting this into practice in the real world has proven elusive, because quantum computing takes a lot of processing power to carry out effectively.
It remains to be seen how “quantum” the Samsung handset’s security chip actually is, but it’s worth noting that quantum encryption is seen as an important advance in keeping up with adversary capabilities, particularly if quantum computing – which can break traditional asymmetric encryption algorithms like RSA, SSL, TLS and HTTPS in an instant – comes on board.
Some are skeptical on that front. At the Cryptographer’s Panel at the RSA Conference in February, Ron Rivest (the R in RSA), said that he believes that quantum computing as it stands will never get to the point of efficiently being deployed, because of the sheer amount of horsepower and expense it requires to function.
“I give fusion power a higher chance of succeeding than quantum computing,” Rivest said. “There is a lot of scaling that has to be done before you can break cryptography, I am not sure it can be done.”
That said, never say never, he noted: “I hope people building quantum computers fail,” Rivest noted. “It would mean the demise of a lovely algorithm we all know and love.”
Concerned about the IoT security challenges businesses face as more connected devices run our enterprises, drive our manufacturing lines, track and deliver healthcare to patients, and more? On June 3 at 2 p.m. ET, join renowned security technologist Bruce Schneier, Armis CISO Curtis Simpson and Threatpost for a FREE webinar, Taming the Unmanaged and IoT Device Tsunami. Get exclusive insights on how to manage this new and growing attack surface. Please register here for this sponsored webinar.
References
attendee.gotowebinar.com/register/1837650474090338831?source=ART
attendee.gotowebinar.com/register/1837650474090338831?source=ART
attendee.gotowebinar.com/register/1837650474090338831?source=ART
futurism.com/high-dimensional-quantum-encryption-performed-in-real-world-city-conditions-for-first-time
quantumxc.com/quantum-cryptography-explained/
threatpost.com/newsletter-sign/
www.csoonline.com/article/3293938/how-quantum-computers-will-destroy-and-maybe-save-cryptography.html
www.fanaticalfuturist.com/2019/03/chinese-researchers-crack-unhackable-quantum-encryption-and-reveal-method/
www.sktelecom.com/advertise/press_detail.do?page.page=1&idx=5229&page.type=all&page.keyword
www.tel.com/museum/exhibition/principle/cmos.html
