Staff Think Conti Group Is a Legit Employer – Podcast
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C
Thanks to gray-hat Ukrainian hacker ContiLeaks, the Conti ransomware gang spilled its guts in late February. Since then, researchers have been poring over the group’s secrets, including a massive trove of chat logs and other doxxed data, including source code for Conti ransomware, TrickBot malware, a decryptor and the gang’s administrative panels.
ContiLeaks published these internal documents after the ransomware group’s leaders posted an aggressively pro-Russian message on their official site in the aftermath of Russia’s invasion of Ukraine.
Last week, BreachQuest published the findings of its week-long deep dive into the data. In essence, BreachQuest found that Conti Group operates like a legitimate, above-board high-tech company that hires and even fires contractors and salaried employees alike.
The dump enabled researchers to sketch out a chart showing key figureheads and the roles they play to grow Conti’s enterprise, plus details on:
- Earnings and costs;
- How they recruit;
- Who are the leaders;
- Who they target: small as well as big targets;
- How they target and escalate attacks and how they receive payments;
- How they find their victims;
- Project Blockchain – Conti group’s effort to create its own altcoin; and
- A more thorough understanding of the tools used to spy on and compromise victims.
Marco Figueroa, head of product at BreachQuest, dropped in on the Threatpost podcast to give us some of the intelligence gleaned from the leaked chat logs. Those logs show that over the course of 13 months, Conti spent about $6M on salary, monthly bonuses, tooling and services.

(Brought to you by SpecOps. Underwriters of Threatpost podcasts do not assert any editorial control over content.)
Its HR team is indicative of how professionally Conti group conducts business: They offer “employee of the month” and performance review programs, for example.
In short, Conti group considers itself a legitimate company. Many of its employees don’t even know they’re working for a cybercriminal outfit. Some probably choose to look the other way, but the turnover is still high: When they figure it out, they tend to vamoose.
That’s probably one reason why Conti’s training materials are the best Marco’s ever seen: The group needs to document procedures because they constantly have to train new contractors.
In fact, security teams themselves should take the training, Marco says, to find out how the ransomware outfit successfully trains its regrettably top-notch cyberattackers.
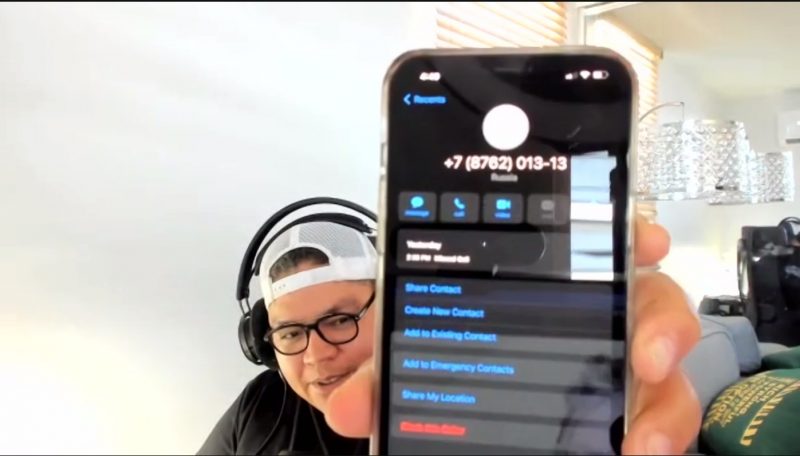
By the way, after BreachQuest’s report was published, Marco got a phone call from Russia: a first for him, he said. Either Conti’s a fan of BreachQuest’s research, it was a wrong number, or hey, who knows? Maybe its HR team is expanding its outreach.
Marco got a call from Russia. He didn’t answer. Source: Threatpost screen capture.
You can download the podcast below or listen here. For more podcasts, check out Threatpost’s podcast site.
_Moving to the cloud? Discover emerging cloud-security threats along with solid advice for how to defend your assets with our _FREE downloadable eBook, “Cloud Security: The Forecast for 2022.”****We explore organizations’ top risks and challenges, best practices for defense, and advice for security success in such a dynamic computing environment, including handy checklists.
References
traffic.libsyn.com/digitalunderground/031122_Marco_Figueroa_BreachQuest_mixdown.mp3
bit.ly/3Jy6Bfs
media.threatpost.com/wp-content/uploads/sites/103/2022/03/14174903/Russia_calling_Marco-e1647294557940.jpg
threatpost.com/conti-ransomware-decryptor-trickbot-source-code-leaked/178727/
threatpost.com/microsite/threatpost-podcasts-going-beyond-the-headlines/
threatpost.com/trickbot-break-researchers-scratching-heads/178678/
threatpost.com/ukraine-russia-cyber-warzone-splits-cyber-underground/178693/
www.breachquest.com/conti-leaks-insight-into-a-ransomware-unicorn/
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C