New Malware Campaign Targeting Job Seekers with Cobalt Strike Beacons
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C
A social engineering campaign leveraging job-themed lures is weaponizing a years-old remote code execution flaw in Microsoft Office to deploy Cobalt Strike beacons on compromised hosts.
“The payload discovered is a leaked version of a Cobalt Strike beacon,” Cisco Talos researchers Chetan Raghuprasad and Vanja Svajcer said in a new analysis published Wednesday.
“The beacon configuration contains commands to perform targeted process injection of arbitrary binaries and has a high reputation domain configured, exhibiting the redirection technique to masquerade the beacon’s traffic.”
The malicious activity, discovered in August 2022, attempts to exploit the vulnerability CVE-2017-0199, a remote code execution issue in Microsoft Office, that allows an attacker to take control of an affected system.
The entry vector for the attack is a phishing email containing a Microsoft Word attachment that employs job-themed lures for roles in the U.S. government and Public Service Association, a trade union based in New Zealand.
Cobalt Strike beacons are far from the only malware samples deployed, for Cisco Talos said it has also observed the usage of the Redline Stealer and Amadey botnet executables as payloads at the other end of the attack chain.
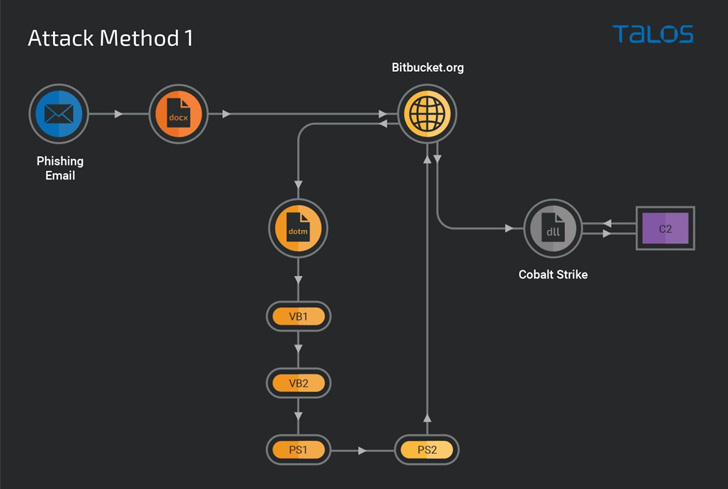
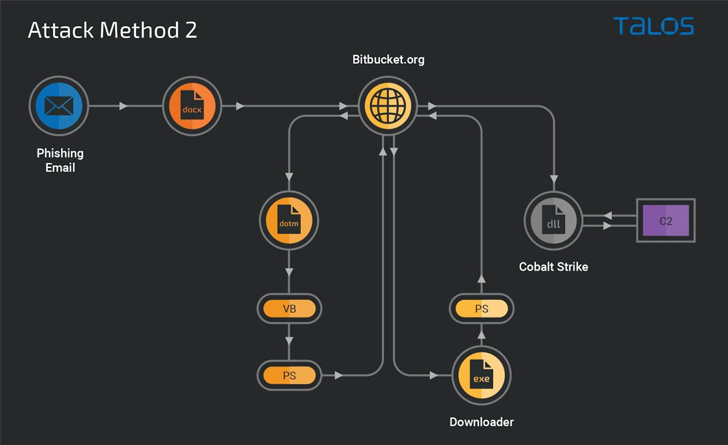
Calling the attack methodology “highly modularized,” the cybersecurity company said the activity also stands out for its use of Bitbucket repositories to host malicious content that serves as a starting point for downloading a Windows executable responsible for deploying the Cobalt Strike DLL beacon.
In an alternative attack sequence, the Bitbucket repository functions as a conduit to deliver obfuscated VB and PowerShell downloader scripts to install the beacon hosted on a different Bitbucket account.
“This campaign is a typical example of a threat actor using the technique of generating and executing malicious scripts in the victim’s system memory,” the researchers said.
“Organizations should be constantly vigilant on the Cobalt Strike beacons and implement layered defense capabilities to thwart the attacker’s attempts in the earlier stage of the attack’s infection chain.”
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C