Attackers Can Remotely Disable Fortress Wi-Fi Home Security Alarms
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
6.8 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:M/Au:N/C:P/I:P/A:P
New vulnerabilities have been discovered in Fortress S03 Wi-Fi Home Security System that could be potentially abused by a malicious party to gain unauthorized access with an aim to alter system behavior, including disarming the devices without the victim’s knowledge.
The two unpatched issues, tracked under the identifiers CVE-2021-39276 (CVSS score: 5.3) and CVE-2021-39277 (CVSS score: 5.7), were discovered and reported by cybersecurity firm Rapid7 in May 2021 with a 60-day deadline to fix the weaknesses.
The Fortress S03 Wi-Fi Home Security System is a do-it-yourself (DIY) alarm system that enables users to secure their homes and small businesses from burglars, fires, gas leaks, and water leaks by leveraging Wi-Fi and RFID technology for keyless entry. The company’s security and surveillance systems are used by “thousands of clients and continued customers,” according to its website.
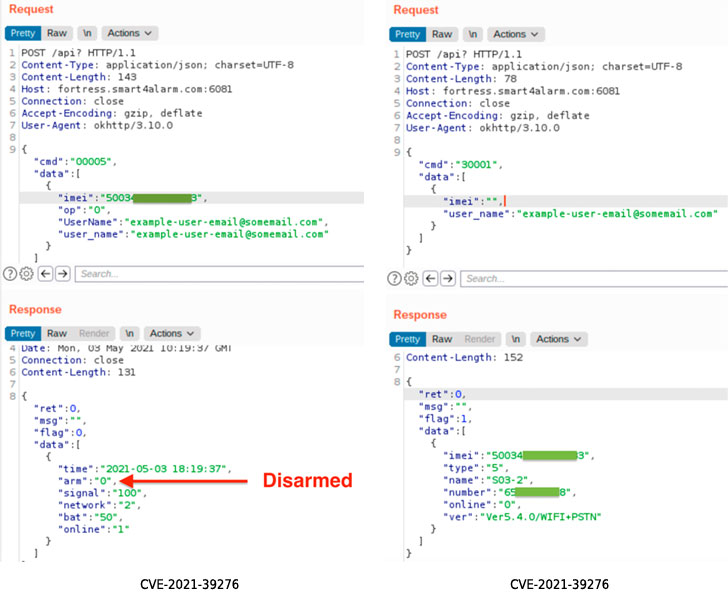
Calling the vulnerabilities “trivially easy to exploit,” Rapid7 researchers noted CVE-2021-39276 concerns an unauthenticated API Access that enables an attacker in possession of a victim’s email address to query the API to leak the device’s International Mobile Equipment Identity (IMEI) number, which also doubles up as the serial number. Armed with the device’s IMEI number and the email address, the adversary can proceed to make a number of unauthorized changes, such as disabling the alarm system via an unauthenticated POST request.
CVE-2021-39277, on the other hand, relates to an RF Signal replay attack, wherein a lack of adequate encryption grants the bad actor the ability to capture the radio frequency command and control communications over the air using a software-defined radio (SDR), and playback the transmission to perform specific functions, such as “arm” and “disarm” operations, on the target device.
“For CVE-2021-39276, an attacker with the knowledge of a Fortress S03 user’s email address can easily disarm the installed home alarm without that user’s knowledge,” the researchers said in a report shared with The Hacker News.
“CVE-2021-39277 presents similar problems, but requires less prior knowledge of the victim, as the attacker can simply stake out the property and wait for the victim to use the RF-controlled devices within radio range. The attacker can then replay the ‘disarm’ command later, without the victim’s knowledge.”
Rapid7 said it notified Fortress Security of the bugs on May 13, 2021, only for the company to close the report 11 days later on May 24. We have reached out to Fortress Security for comment, and we will update the story if we hear back.
In light of the fact that the issues continue to persist, it’s recommended that users configure their alarm systems with a unique, one-time email address to work around the IMEI number exposure.
“For CVE-2021-39277, there seems to be very little a user can do to mitigate the effects of the RF replay issues absent a firmware update to enforce cryptographic controls on RF signals. Users concerned about this exposure should avoid using the key fobs and other RF devices linked to their home security systems,” the researchers said.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
6.8 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:M/Au:N/C:P/I:P/A:P