New Lenovo UEFI Firmware Vulnerabilities Affect Millions of Laptops
EPSS
Percentile
12.6%
Three high-impact Unified Extensible Firmware Interface (UEFI) security vulnerabilities have been discovered impacting various Lenovo consumer laptop models, enabling malicious actors to deploy and execute firmware implants on the affected devices.
Tracked as CVE-2021-3970, CVE-2021-3971, and CVE-2021-3972, the latter two “affect firmware drivers originally meant to be used only during the manufacturing process of Lenovo consumer notebooks,” ESET researcher Martin Smolár said in a report published today.
“Unfortunately, they were mistakenly included also in the production BIOS images without being properly deactivated,” Smolár added.
Successful exploitation of the flaws could permit an attacker to disable SPI flash protections or Secure Boot, effectively granting the adversary the ability to install persistent malware that can survive system reboots.
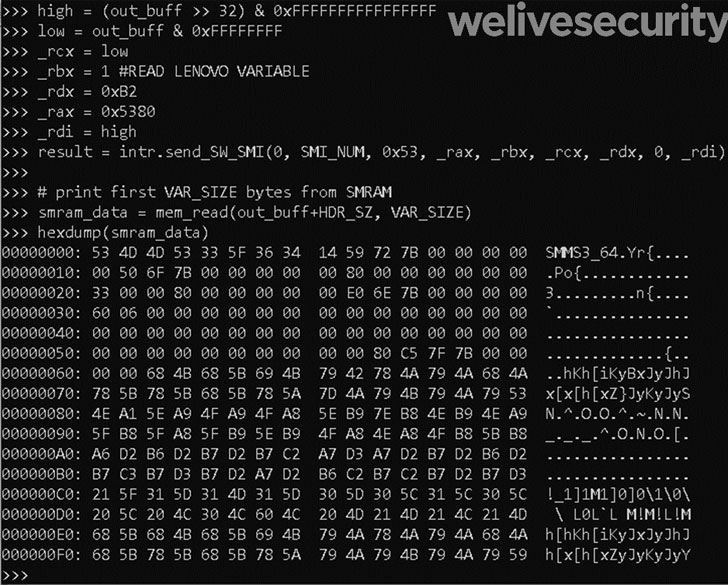
CVE-2021-3970, on the other hand, relates to a case of memory corruption in the System Management Mode (SMM) of the firm, leading to the execution of malicious code with the highest privileges.
The three flaws were reported to the PC maker on October 11, 2021, following which patches were issued on April 12, 2022. A summary of the three flaws as described by Lenovo is below -
- CVE-2021-3970 – A potential vulnerability in LenovoVariable SMI Handler due to insufficient validation in some Lenovo Notebook models may allow an attacker with local access and elevated privileges to execute arbitrary code.
- CVE-2021-3971 – A potential vulnerability by a driver used during older manufacturing processes on some consumer Lenovo Notebook devices that was mistakenly included in the BIOS image could allow an attacker with elevated privileges to modify the firmware protection region by modifying an NVRAM variable.
- CVE-2021-3972 – A potential vulnerability by a driver used during manufacturing process on some consumer Lenovo Notebook devices that was mistakenly not deactivated may allow an attacker with elevated privileges to modify secure boot setting by modifying an NVRAM variable.
The weaknesses, which impact Lenovo Flex; IdeaPads; Legion; V14, V15, and V17 series; and Yoga laptops, add to the disclosure of as many as 50 UEFI firmware vulnerabilities in Insyde Software’s InsydeH2O, HP, and Dell since the start of the year.
Included in the list are six severe flaws in HP’s firmware affecting laptops and desktops that, if successfully exploited, could allow attackers to locally escalate to SMM privileges and trigger a denial-of-service (DoS) condition.
“UEFI threats can be extremely stealthy and dangerous,” Smolár said. “They are executed early in the boot process, before transferring control to the operating system, which means that they can bypass almost all security measures and mitigations higher in the stack that could prevent their OS payloads from being executed.”
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.