Cortana Software Could Help Anyone Unlock Your Windows 10 Computer
6.8 Medium
CVSS3
Attack Vector
PHYSICAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
4.6 Medium
CVSS2
Access Vector
LOCAL
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:L/AC:L/Au:N/C:P/I:P/A:P
0.003 Low
EPSS
Percentile
64.0%
Cortana, an artificial intelligence-based smart assistant that Microsoft has built into every version of Windows 10, could help attackers unlock your system password.
With its latest patch Tuesday release, Microsoft has pushed an important update to address an easily exploitable vulnerability in Cortana that could allow hackers to break into a locked Windows 10 system and execute malicious commands with the user’s privileges.
In worst case scenario, hackers could also compromise the system completely if the user has elevated privileges on the targeted system.
The elevation of privilege vulnerability, tracked as CVE-2018-8140 and reported by McAfee security researchers, resides due to Cortana’s failure to adequately check command inputs, which eventually leads to code execution with elevated permissions.
> “An Elevation of Privilege vulnerability exists when Cortana retrieves data from user input services without consideration for status,” Microsoft explains. “An attacker who successfully exploited the vulnerability could execute commands with elevated permissions.”
Microsoft has classified the flaw as “important” because exploitation of this vulnerability requires an attacker to have physical or console access to the targeted system and the targeted system also needs to have Cortana enabled.
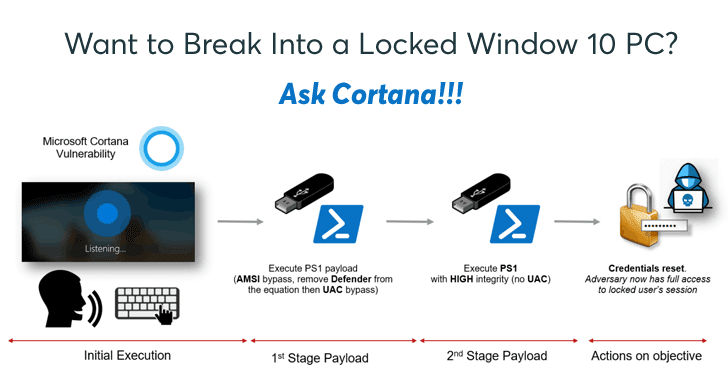
Cedric Cochin of McAfee’s Advanced Threat Research (ATR) team has published technical details of the flaw, and also provided a step-by-step proof-of-concept video tutorial, showing how he hijacked a locked Windows 10 computer by carrying out a full password reset using Cortana.
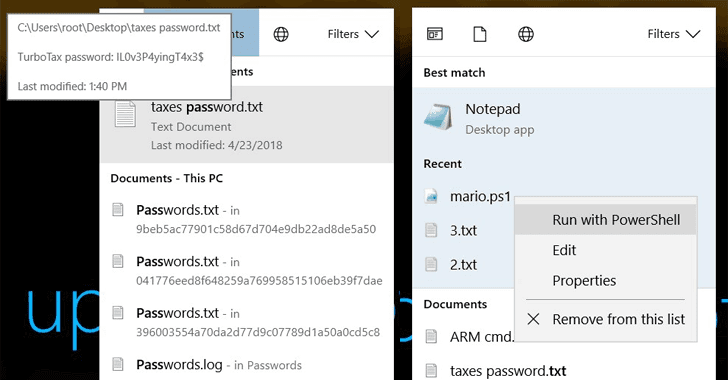
> “Cochin discovered that by simply typing while Cortana starts to listen to a request or question on a locked device, he could bring up a search menu. Cochin didn’t even have to say anything to Cortana, but simply clicked on the “tap and say” button and started typing in words,” a blog post on McAfee explained.
Cochin represents three different attack vectors, demonstrating how the Cortana flaw could be used for various nefarious purposes, such as retrieving confidential information, logging into a locked device and even run malicious code from the locked screen.
McAfee recommends users to turn off Cortana on the lock screen in order to prevent such attacks. Although Microsoft has patched the vulnerability with its latest security updates released yesterday, many PCs will not be running the latest updates just yet.
6.8 Medium
CVSS3
Attack Vector
PHYSICAL
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:P/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
4.6 Medium
CVSS2
Access Vector
LOCAL
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:L/AC:L/Au:N/C:P/I:P/A:P
0.003 Low
EPSS
Percentile
64.0%