Use This One-Click Mitigation Tool from Microsoft to Prevent Exchange Attacks
EPSS
Percentile
100.0%
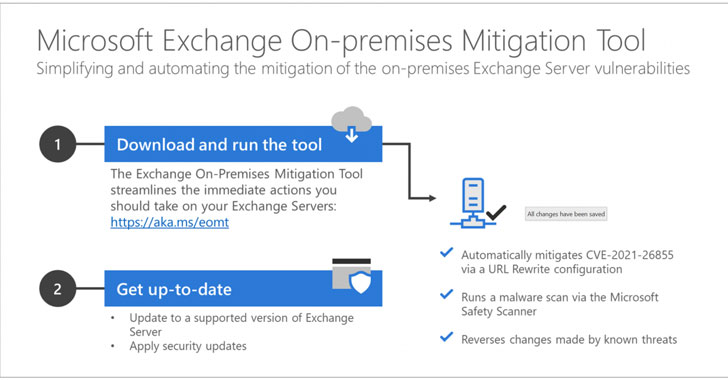
Microsoft on Monday released a one-click mitigation software that applies all the necessary countermeasures to secure vulnerable environments against the ongoing widespread ProxyLogon Exchange Server cyberattacks.
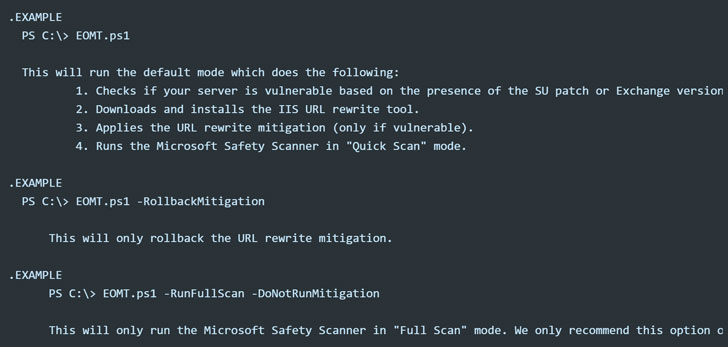
Called Exchange On-premises Mitigation Tool (EOMT), the PowerShell-based script serves to mitigate against current known attacks using CVE-2021-26855, scan the Exchange Server using the Microsoft Safety Scanner for any deployed web shells, and attempt to remediate the detected compromises.
“This new tool is designed as an interim mitigation for customers who are unfamiliar with the patch/update process or who have not yet applied the on-premises Exchange security update,” Microsoft said.
The development comes in the wake of indiscriminate attacks against unpatched Exchange Servers across the world by more than ten advanced persistent threat actors — most of the government-backed cyberespionage groups — to plant backdoors, coin miners, and ransomware, with the release of proof-of-concept (PoC) fueling the hacking spree even further.
Based on telemetry from RiskIQ, 317,269 out of 400,000 on-premises Exchange Servers globally have been patched as of March 12, with the U.S., Germany, Great Britain, France, and Italy leading the countries with vulnerable servers.
Additionally, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated its guidance to detail as many as seven variants of the China Chopper web shell that are being leveraged by malicious actors.
Taking up just four kilobytes, the web shell has been a popular post-exploitation tool of choice for cyber attackers for nearly a decade.
While the breadth of the intrusions is being assessed, Microsoft is also reportedly investigating how the “limited and targeted” attacks it detected in early January picked up steam to quickly morph into a widespread mass exploitation campaign, forcing it to release the security fixes a week before it was due.
The Wall Street Journal on Friday reported that investigators are focused on whether a Microsoft partner, with whom the company shared information about the vulnerabilities through its Microsoft Active Protections Program (MAPP), either accidentally or purposefully leaked it to other groups.
It is also being claimed that some tools used in the “second wave” of attacks towards the end of February are similar to proof-of-concept attack code that Microsoft shared with antivirus companies and other security partners on February 23, raising the possibility that threat actors may have gotten their hands on private disclosure that Microsoft shared with its security partners.
The other theory is that the threat actors independently discovered the same set of vulnerabilities, which were then exploited to stealthily conduct reconnaissance of target networks and steal mailboxes, before ramping up the attacks once the hackers figured out Microsoft was readying a patch.
“This is the second time in the last four months that nation-state actors have engaged in cyberattacks with the potential to affect businesses and organizations of all sizes,” Microsoft said. “While this began as a nation-state attack, the vulnerabilities are being exploited by other criminal organizations, including new ransomware attacks, with the potential for other malicious activities.”
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.