7-Year-Old Polkit Flaw Lets Unprivileged Linux Users Gain Root Access
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
LOW
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
7.2 High
CVSS2
Access Vector
LOCAL
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:L/AC:L/Au:N/C:C/I:C/A:C
A seven-year-old privilege escalation vulnerability discovered in the polkit system service could be exploited by a malicious unprivileged local attacker to bypass authorization and escalate permissions to the root user.
Tracked as CVE-2021-3560 (CVSS score: 7.8), the flaw affects polkit versions between 0.113 and 0.118 and was discovered by GitHub security researcher Kevin Backhouse, who said the issue was introduced in a code commit made on Nov. 9, 2013. Red Hat’s Cedric Buissart noted that Debian-based distributions, based on polkit 0.105, are also vulnerable.
Polkit (née PolicyKit) is a toolkit for defining and handling authorizations in Linux distributions, and is used for allowing unprivileged processes to communicate with privileged processes.
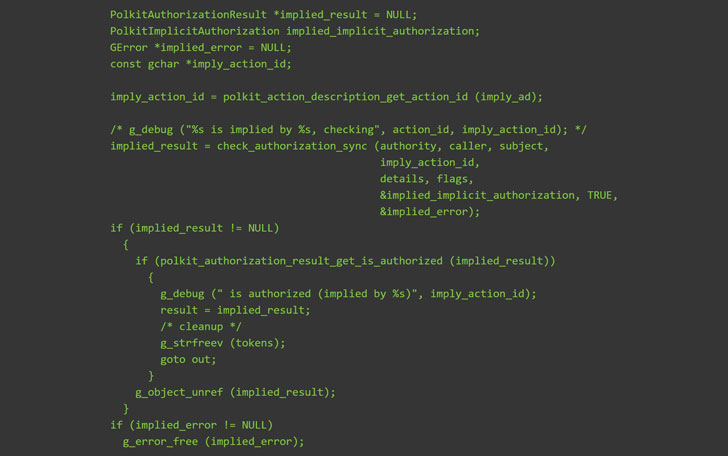
“When a requesting process disconnects from dbus-daemon just before the call to polkit_system_bus_name_get_creds_sync starts, the process cannot get a unique uid and pid of the process and it cannot verify the privileges of the requesting process,” Red Hat said in an advisory. “The highest threat from this vulnerability is to data confidentiality and integrity as well as system availability.”
RHEL 8, Fedora 21 (or later), Debian “Bullseye,” and Ubuntu 20.04 are some of the popular Linux distributions impacted by the polkit vulnerability. The issue has been mitigated in version 0.119, which was released on June 3.
“The vulnerability is surprisingly easy to exploit. All it takes is a few commands in the terminal using only standard tools like bash, kill, and dbus-send,” said Backhouse in a write-up published yesterday, adding the flaw is triggered by sending a dbus-send command (say, to create a new user) but terminating the process while polkit is still in the middle of processing the request.
“dbus-send” is a Linux inter-process communication (IPC) mechanism that’s used to send a message to D-Bus message bus, allowing communication between multiple processes running concurrently on the same machine. Polkit’s policy authority daemon is implemented as a service connected to the system bus to authenticate credentials securely.
In killing the command, it causes an authentication bypass because polkit mishandles the terminated message and treats the request as though it came from a process with root privileges (UID 0), thereby immediately authorizing the request.
“To trigger the vulnerable codepath, you have to disconnect at just the right moment,” Backhouse said. “And because there are multiple processes involved, the timing of that ‘right moment’ varies from one run to the next. That’s why it usually takes a few tries for the exploit to succeed. I’d guess it’s also the reason why the bug wasn’t previously discovered.”
Users are encouraged to update their Linux installations as soon as possible to remediate any potential risk arising out of the flaw.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
LOW
Privileges Required
LOW
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
7.2 High
CVSS2
Access Vector
LOCAL
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:L/AC:L/Au:N/C:C/I:C/A:C