Instagram Bug Allowed Anyone to View Private Accounts Without Following Them
Instagram has patched a new flaw that allowed anyone to view archived posts and stories posted by private accounts without having to follow them.
“This bug could have allowed a malicious user to view targeted media on Instagram,” security researcher Mayur Fartade said in a Medium post today. “An attacker could have been able to see details of private/archived posts, stories, reels, IGTV without following the user using Media ID.”
Fartade disclosed the issue to Facebook’s security team on April 16, 2021, following which the shortcoming was patched on June 15. He was also awarded $30,000 as part of the company’s bug bounty program.
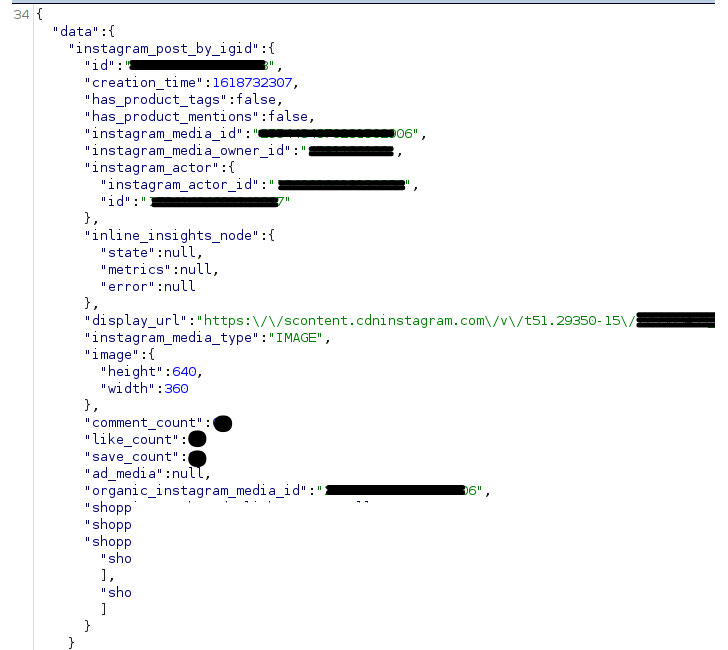
Although the attack requires knowing the media ID associated with an image, video, or album, by brute-forcing the identifiers, Fartade demonstrated that it was possible to craft a POST request to a GraphQL endpoint and retrieve sensitive data.
As a consequence of the flaw, details such as like/comment/save count, display_url, and image.uri corresponding to the media ID could be extracted even without following the targeted user, alongside exposing the Facebook Page linked to an Instagram account.
Fartade said he also discovered a second endpoint on April 23 that revealed the same set of information. Facebook has since addressed both the leaky endpoints.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.