Popular NPM Package Updated to Wipe Russia, Belarus Systems to Protest Ukraine Invasion
0.008 Low
EPSS
Percentile
81.1%
In what’s an act of deliberate sabotage, the developer behind the popular “node-ipc” NPM package shipped a new tampered version to condemn Russia’s invasion of Ukraine, raising concerns about security in the open-source and the software supply chain.
Affecting versions 10.1.1 and 10.1.2 of the library, the alterations introduced by its maintainer RIAEvangelist brought about undesirable behavior by targeting users with IP addresses located either in Russia or Belarus, and wiping arbitrary file contents and replacing them with a heart emoji.
Node-ipc is a prominent node module used for local and remote inter-process communication (IPC) with support for Linux, macOS, and Windows. It has over 1.1 million weekly downloads.
“A very clear abuse and a critical supply chain security incident will occur for any system on which this NPM package will be called upon, if that matches a geo-location of either Russia or Belarus,” Synk researcher Liran Tal said in an analysis.
The issue has been assigned the identifier CVE-2022-23812 and is rated 9.8 out of 10 on the CVSS vulnerability scoring system. The malicious code changes were published on March 7 (version 10.1.1), with a second update occurring 10 hours later the same day (version 10.1.1).
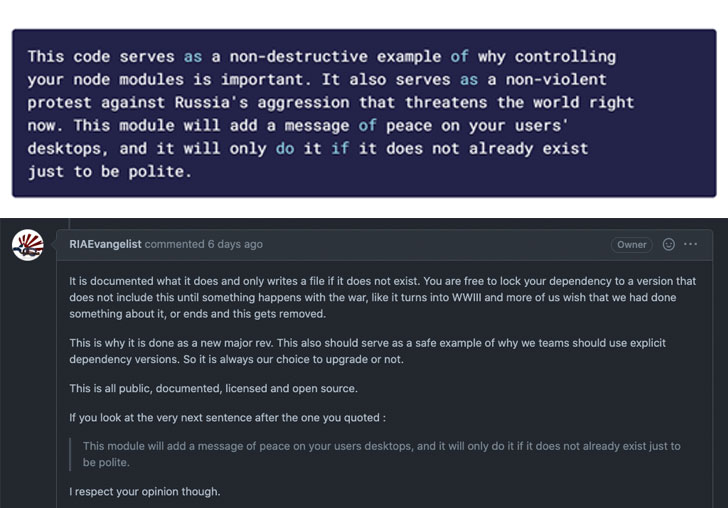
Interestingly, although the destructive modifications were removed from the library with version 10.1., a major update was pushed after less than four hours (version 11.0.0), which imported another dependency called “peacenotwar,” also released by RIAEvangelist as a form of “non-violent protest against Russia’s aggression.”
“Any time the node-ipc module functionality gets called, it prints to STDOUT a message taken out of the peacenotwar module, as well as places a file on the user’s Desktop directory with contents relating to the current war-time situation of Russia and Ukraine,” Tal explained.
As of March 15, 2022, the latest version of node-ipc – 11.1.0 – bumps the “peacenotwar” package version from 9.1.3 to 9.1.5 and bundles the “colors” NPM library, while also removing the STDOUT console messages.
It’s worth noting that “colors,” along with another package called “faker,” were both intentionally sabotaged earlier this January by its developer Marak Squires by introducing infinite loops to the source code, effectively breaking other applications that depended on the libraries.
According to Bleeping Computer, which first reported the corruption, the changes are said to have been retaliatory, with the developer noting that “Respectfully, I am no longer going to support Fortune 500s (and other smaller sized companies) with my free work.”
If anything, the idea of using popular modules as “protestware” to deploy destructive payloads and stage a supply chain compromise runs the risk of undermining trust in open-source software.
“This security incident involves destructive acts of corrupting files on disk by one maintainer and their attempts to hide and restate that deliberate sabotage in different forms,” Tal said. “While this is an attack with protest-driven motivations, it highlights a larger issue facing the software supply chain: the transitive dependencies in your code can have a huge impact on your security.”
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.