Mazafaka — Elite Hacking and Cybercrime Forum — Got Hacked!
In what’s a case of hackers getting hacked, a prominent underground online criminal forum by the name of Maza has been compromised by unknown attackers, making it the fourth forum to have been breached since the start of the year.
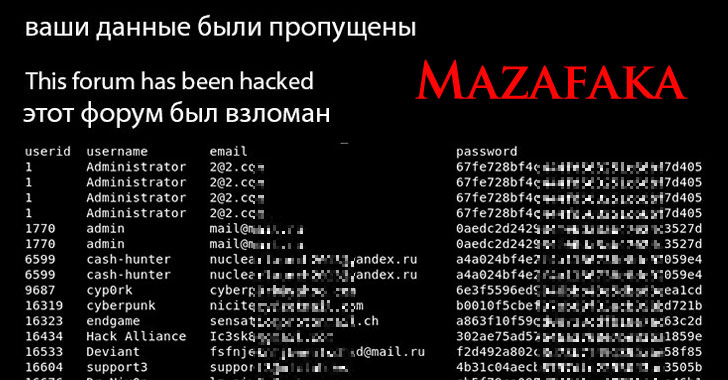
The intrusion is said to have occurred on March 3, with information about the forum members — including usernames, email addresses, and hashed passwords — publicly disclosed on a breach notification page put up by the attackers, stating “Your data has been leaked” and “This forum has been hacked.”
“The announcement was accompanied by a PDF file allegedly containing a portion of forum user data. The file comprised more than 3,000 rows, containing usernames, partially obfuscated password hashes, email addresses and other contact details,” cybersecurity firm Intel 471 said.
Originally called Mazafaka, Maza is an elite, invite-only Russian-language cybercrime forum known to be operational as early as 2003, acting as an exclusive online space for exploit actors to trade ransomware-as-a-service tools and conduct other forms of illicit cyber operations.
The development comes close on the heels of successful breaches of other forums, including that of Verified, Crdclub, and Exploit.
Verified is said to have been breached on January 20, 2021, with the actor behind the attack claiming access to the entire database on another popular forum called Raid Forums, besides transferring $150,000 worth of cryptocurrency from Verified’s bitcoin wallet to their own. The forum, however, staged a return last month on February 18 with a change in ownership, according to Flashpoint.
Then again, in February, a cybercrime forum known as Crdclub disclosed an attack that resulted in the compromise of an administrator account with the goal of defrauding its members. No other personal information appears to have been plundered.
“By doing so, the actor behind the attack was able to lure forum customers to use a money transfer service that was allegedly vouched for by the forum’s admins,” Intel 471 said. “That was a lie, and resulted in an unknown amount of money being diverted from the forum.”
Lastly, earlier this week, the Exploit cybercrime forum sustained an attack that involved an apparent compromise of a proxy server used for safeguarding the forum from distributed denial-of-service (DDoS) attacks.
Details are fuzzy as to the perpetrators of the attacks, with forum members speculating that it could be the work of a government intelligence agency, while also distressing over the possibility that their real-world identities could be exposed in the wake of the leaks.
Flashpoint researchers noted that the Russian sentences on the Maza forum’s notification page were possibly translated using an online translator, but added it’s unclear if this implies the involvement of a non-Russian speaking actor or if it was deliberately used to mislead attribution.
“While Intel 471 isn’t aware of anyone claiming responsibility for the breaches, whomever is behind the actions has indirectly given researchers an advantage,” the company concluded. “Any information unearthed from the breaches aids in the fight against these criminals due to the added visibility it gives security teams who are tracking actors that populate these forums.”
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.