New Microsoft Exchange 'ProxyToken' Flaw Lets Attackers Reconfigure Mailboxes
7.5 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
NONE
Availability Impact
NONE
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
5 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
NONE
Availability Impact
NONE
AV:N/AC:L/Au:N/C:P/I:N/A:N
Details have emerged about a now-patched security vulnerability impacting Microsoft Exchange Server that could be weaponized by an unauthenticated attacker to modify server configurations, thus leading to the disclosure of Personally Identifiable Information (PII).
The issue, tracked as CVE-2021-33766 (CVSS score: 7.3) and coined “ProxyToken,” was discovered by Le Xuan Tuyen, a researcher at the Information Security Center of Vietnam Posts and Telecommunications Group (VNPT-ISC), and reported through the Zero-Day Initiative (ZDI) program in March 2021.
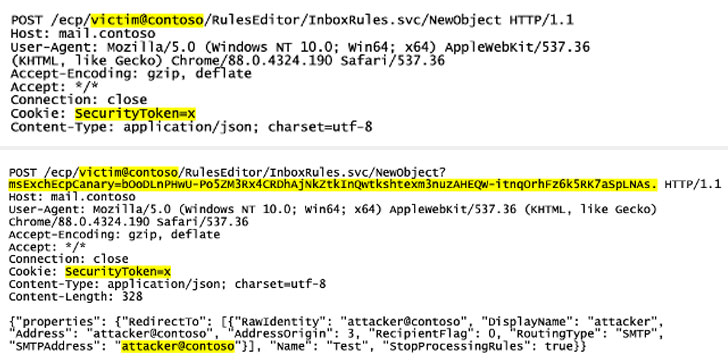
“With this vulnerability, an unauthenticated attacker can perform configuration actions on mailboxes belonging to arbitrary users,” the ZDI said Monday. “As an illustration of the impact, this can be used to copy all emails addressed to a target and account and forward them to an account controlled by the attacker.”
Microsoft addressed the issue as part of its Patch Tuesday updates for July 2021.
The security shortcoming resides in a feature called Delegated Authentication, which refers to a mechanism whereby the front-end website — the Outlook web access (OWA) client — passes authentication requests directly to the back-end when it detects the presence of a SecurityToken cookie.
However, since Exchange has to be specifically configured to use the feature and have the back-end carry out the checks, it leads to a scenario in which the module handling this delegation (“DelegatedAuthModule”) isn’t loaded under default configuration, culminating in a bypass as the back-end fails to authenticate incoming requests based on the SecurityToken cookie.
“The net result is that requests can sail through, without being subjected to authentication on either the front or back end,” ZDI’s Simon Zuckerbraun explained.
The disclosure adds to a growing list of Exchange Server vulnerabilities that have come to light this year, including ProxyLogon, ProxyOracle, and ProxyShell, which have been actively exploited by threat actors to take over unpatched servers, deploy malicious web shells and file-encrypting ransomware such as LockFile.
Troublingly, in-the-wild exploit attempts abusing ProxyToken have already been recorded as early as August 10, according to NCC Group security researcher Rich Warren, making it imperative that customers move quickly to apply the security updates from Microsoft.
Found this article interesting? Follow THN on Facebook, Twitter and LinkedIn to read more exclusive content we post.
7.5 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
NONE
Availability Impact
NONE
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
5 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
NONE
Availability Impact
NONE
AV:N/AC:L/Au:N/C:P/I:N/A:N