Cuba Ransomware Extorted Over $60 Million in Ransom Fees from More than 100 Entities
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C
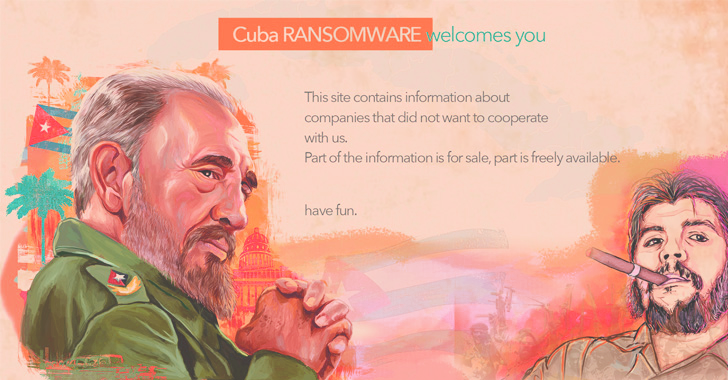
The threat actors behind Cuba (aka COLDDRAW) ransomware have received more than $60 million in ransom payments and compromised over 100 entities across the world as of August 2022.
In a new advisory shared by the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI), the agencies highlighted a “sharp increase in both the number of compromised U.S. entities and the ransom amounts.”
The ransomware crew, also known as Tropical Scorpius, has been observed targeting financial services, government facilities, healthcare, critical manufacturing, and IT sectors, while simultaneously expanding its tactics to gain initial access and interact with breached networks.
It’s worth noting that despite the name “Cuba,” there is no evidence to suggest that the actors have any connection or affiliation with the island country.
The entry point for the attacks involves the exploitation of known security flaws, phishing, compromised credentials, and legitimate remote desktop protocol (RDP) tools, followed by distributing the ransomware via Hancitor (aka Chanitor).
Some of the flaws incorporated by Cuba into its toolset are as follows -
- CVE-2022-24521 (CVSS score: 7.8) - An elevation of privilege vulnerability in Windows Common Log File System (CLFS) Driver
- CVE-2020-1472 (CVSS score: 10.0) - An elevation of privilege vulnerability in Netlogon remote protocol (aka ZeroLogon)
“In addition to deploying ransomware, the actors have used ‘double extortion’ techniques, in which they exfiltrate victim data, and (1) demand a ransom payment to decrypt it and, (2) threaten to publicly release it if a ransom payment is not made,” CISA noted.
Cuba is also said to share links with the operators of RomCom RAT and another ransomware family called Industrial Spy, according to recent findings from BlackBerry and Palo Alto Networks Unit 42.
The RomCom RAT is distributed through trojanized versions of legitimate software such as SolarWinds Network Performance Monitor, KeePass, PDF Reader Pro, Advanced IP Scanner, pdfFiller, and Veeam Backup & Replication that are hosted on counterfeit lookalike websites.
The advisory from CISA and FBI is the latest in a series of alerts the agencies have issued about different ransomware strains such as MedusaLocker, Zeppelin, Vice Society, Daixin Team, and Hive.
Found this article interesting? Follow us on Twitter and LinkedIn to read more exclusive content we post.
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C