
What is NIS2, and how can you best prepare for the new cybersecurity requirements in the EU?
7.1 High
AI Score
Confidence
Low

NIS2 is a European directive that includes new measures to ensure that organizations operating in the European Union (EU) have a high common level of network and infrastructure security.
The "directive" outlines the goals all EU member states must achieve. However, each country will implement it in their own law with room for some national specifics to reach these goals. Directives are binding in terms of minimal requirements for what should be implemented.
For example, if the directive imposes fines for organizations who are not in compliance, states can decide to go beyond the minimum fine and impose higher penalties for entities in their jurisdiction.
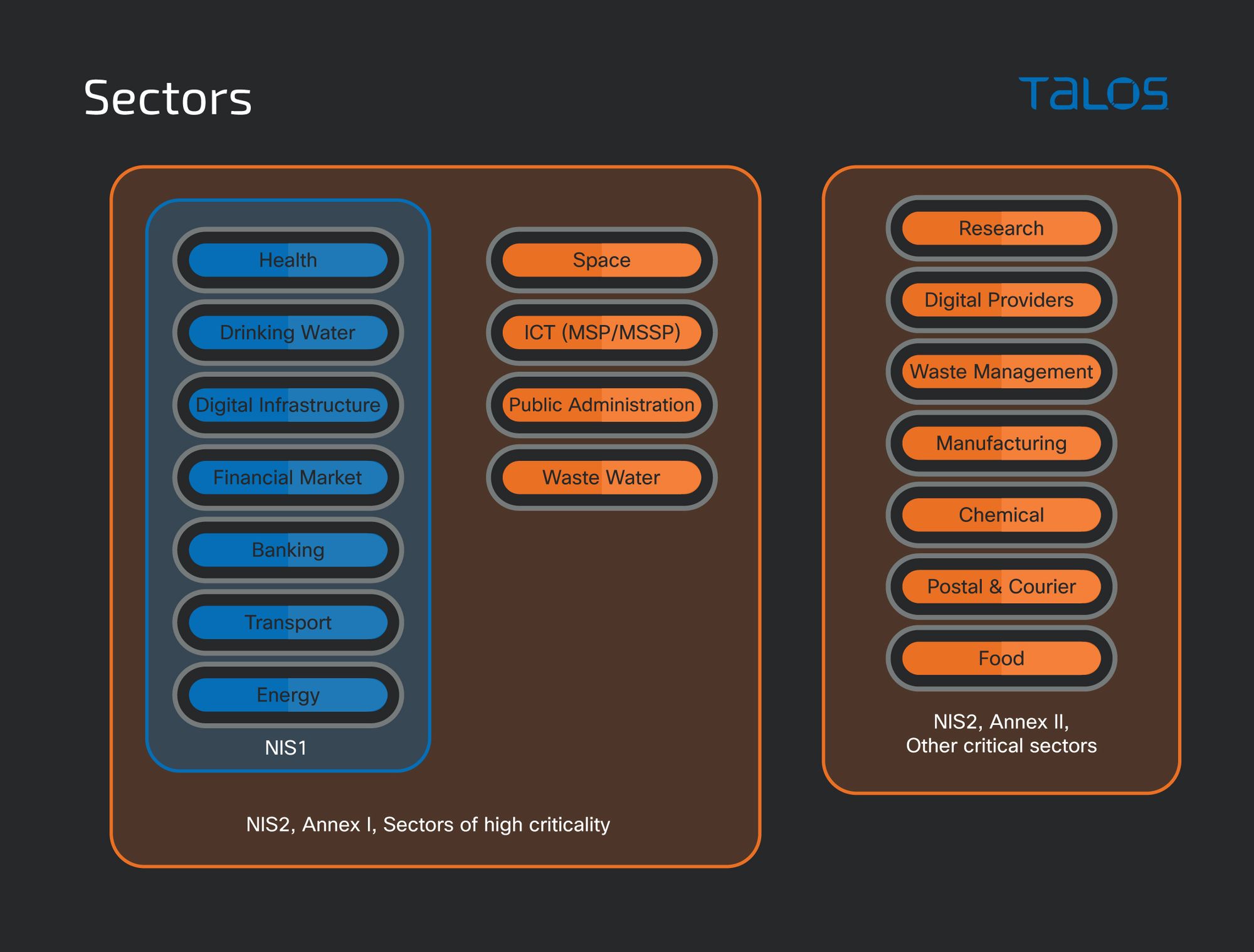
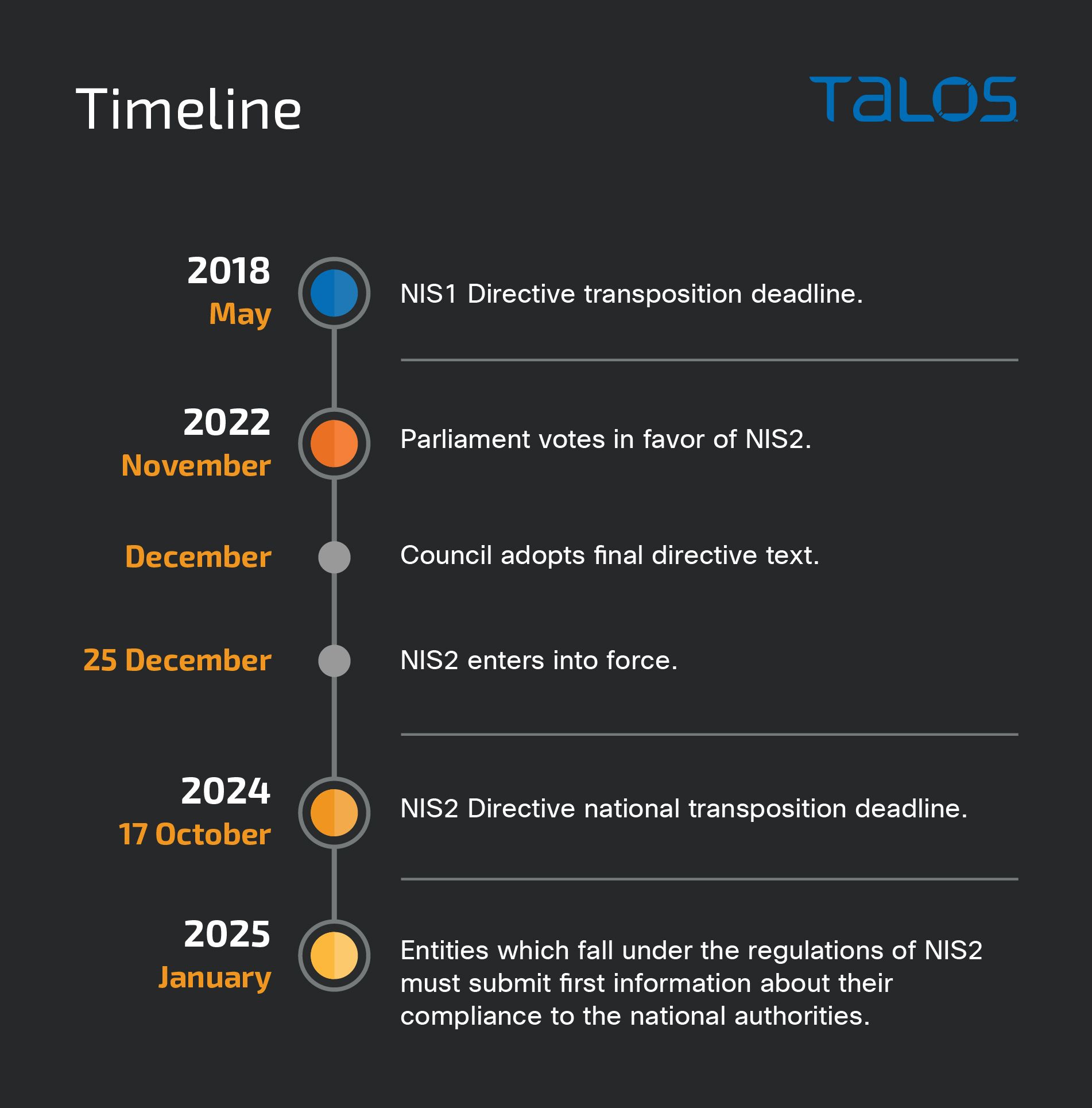
NIS2 is a successor of the NIS1 Directive, which is considered the first EU cybersecurity law. Since its implementation in 2018, NIS1 has proven to be essential for the implementation of the EU Cybersecurity Strategy but not sufficient in addressing the challenges posed by the current cybersecurity threat landscape. NIS2 broadens the scope of the legislation by including new sectors and types of organizations which need to comply and introducing higher requirements for their cybersecurity.
Given the increased geopolitical importance of cybersecurity, NIS2 is a logical step in creating more harmonized and stronger defense capabilities across the European Union.
What is new in NIS2 as compared to NIS1?
- Stricter cybersecurity requirements.
- Broader scope – wider range of sectors and entities affected.
- Change of identification mechanism - from active identification to self-identification.
- Added requirements for supply chain cybersecurity.
- Stronger compliance supervision from the national authorities.
- Clearly defined administrative fines in case of non-compliance.
- Establishment of cybersecurity information-sharing arrangements between interested entities, e.g., a platform for the exchange, automatic tools and content.
Who needs to conform with NIS2?
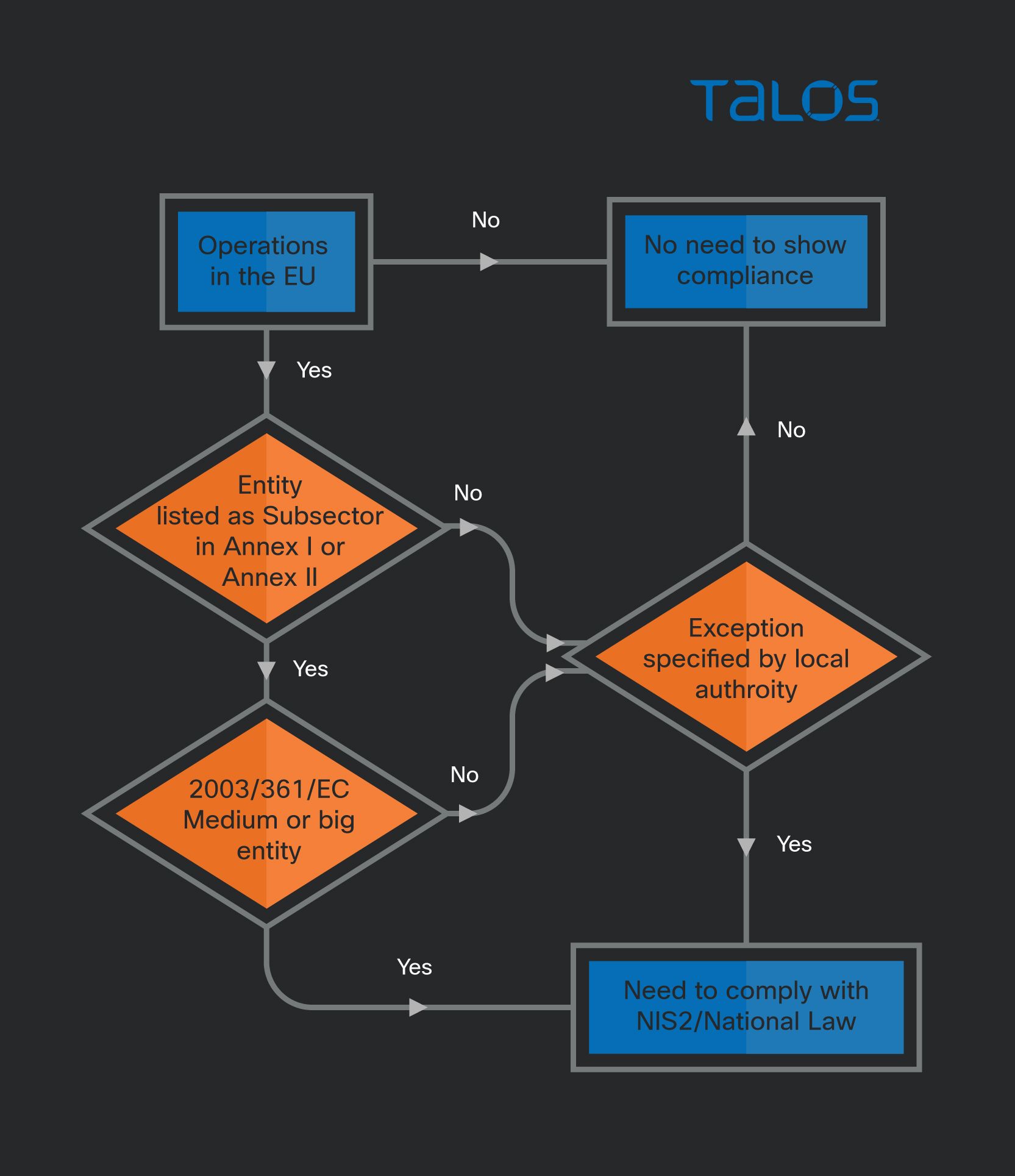
If you operate in the European Union in one of the subsectors listed in the Annex of the Directive and your organization is of a certain size or falls under one of the exceptions under Articles 2 & 3, you must conform to NIS2.
Entities in scope
NIS2 applies to public or private entities which qualify as or exceed the ceilings for medium-sized enterprise as outlined in Recommendation 2003/361/EC: a "medium" entity is "an enterprise which employs 50 or more persons and whose annual turnover and/or annual balance sheet total does exceed EUR 10 million."
Regardless of their size, this directive also applies to several exceptions listed under Article 2 of the directive. Member states may also apply this directive to specific entities/institutions. It is therefore important to double-check with national authorities.
Essential vs. important entities
NIS2 divides entities into two categories – "essential" and "important" – depending on the expected impact of an incident. Both types must comply with the same security measures, but "essential" organizations will always be proactively supervised by the government, and "important" entities will only be checked after a cybersecurity incident. In other words, the control of essential entities is stricter due to the possible more dire consequences if that organization is found to be non-compliant.
What measures need to be implemented as per NIS2?
NIS2 includes a list of 10 key elements that all companies must address in terms of cybersecurity. The exact implementation of these measures should consider state-of-the-art technology and, where applicable, relevant European and international standards at an appropriate and proportionate technical level, and the cost of implementation.
The measures in NIS2 are as follows:
- Policies on risk analysis and information system security.
- Incident handling.
- Business continuity, such as backup management and disaster recovery, and crisis management.
- Supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers.
- Security in network and information systems acquisition, development and maintenance, including vulnerability handling and disclosure.
- Policies and procedures to assess the effectiveness of cybersecurity risk-management measures.
- Basic cyber hygiene practices and cybersecurity training.
- Policies and procedures regarding the use of cryptography and, where appropriate, encryption.
- Human resources security, access control policies and asset management.
- The use of multi-factor authentication or continuous authentication solutions, secured voice, video and text communications and secured emergency communication systems within the entity, where appropriate.
Incident reporting obligations
NIS2 introduces strict incident reporting requirements, which are applicable to essential and important entities:
- Within 24 hours of becoming aware of the incident, the entity must inform the national authority.
- Within 72 hours of a more formal incident, and following an initial incident assessment, a second notification must be provided. It should include incident severity, impact and known indicators of compromise (IOCs).
- Within a month of the formal incident notification, a final report must be submitted.
Fines
Essential and important entities face different administrative fines if they were to fail to meet the incident reporting obligations or general security requirements.
For "essential" entities, national laws must implement a certain level of administrative fines, notably a maximum of at least EUR 10,000,000, or 2% of the total worldwide annual turnover of the preceding fiscal year, whichever is higher.
For "important" entities, the maximum fine is of at least EUR 7,000,000 or at least 1.4% of the total worldwide annual turnover of the preceding financial year, whichever is higher.
When will NIS2 take effect?
The NIS2 Directive was published on Dec. 27, 2022, and each EU member state has until Oct. 17, 2024, to transpose the NIS2 Directive into its national legislation. Once the national laws are effective, organizations that are in scope need to comply.
NIS2 requires that entities have documentation and processes to handle incidents. One of the foundational documents for coordinating the response efforts is an Incident Response Plan.
A Cisco Talos Incident Response Retainer offers several services, such as the incident response plan and IR playbook development, which can help customers create the documentation required by NIS2. Moreover, the training and simulation services in the Talos retainer can support customers in putting new and existing processes to the test and improving the team's overall knowledge in the cyber domain.
Next week, we'll have more information on creating an incident response plan for your organization that complies with NIS2. We have summarized seven of the most common mistakes when starting to write a brand-new plan or reviewing an existing document, and we will share practical advice on how to avoid them.
7.1 High
AI Score
Confidence
Low