
What's New in InsightVM and Nexpose: Q1 2022 in Review
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C

The world of cybersecurity never has a dull moment. While we are still recovering from the aftermath of Log4Shell, the recent ContiLeaks exposed multiple vulnerabilities that have been exploited by the Conti ransomware group. It’s critical for your team to identify the risk posed by such vulnerabilities and implement necessary remediation measures. As you will see, the product updates our vulnerability management (VM) team has made to InsightVM and Nexpose in the last quarter will empower you to stay in charge — not the vulnerabilities.
But that’s not all we’ve improved on. We’ve increased the scope of vulnerabilities tracked by incorporating CISA’s known exploited vulnerabilities (KEV) in the Threat Feed, usability enhancements, targeted reporting and scanning, and Log4Shell mitigation checks. And we’ve released our annual Vulnerability Intelligence Report to help you make sense of the vulns that impacted us last year and understand the trends that we will all be facing this year. Our team also offers practical guidance to help the security teams better protect themselves.
Let’s dive into the key feature releases and updates on the vulnerability management front for Q1 2022.
[InsightVM] ContiLeaks Helpful Query to easily detect ContiLeaks vulns and ensure compliance
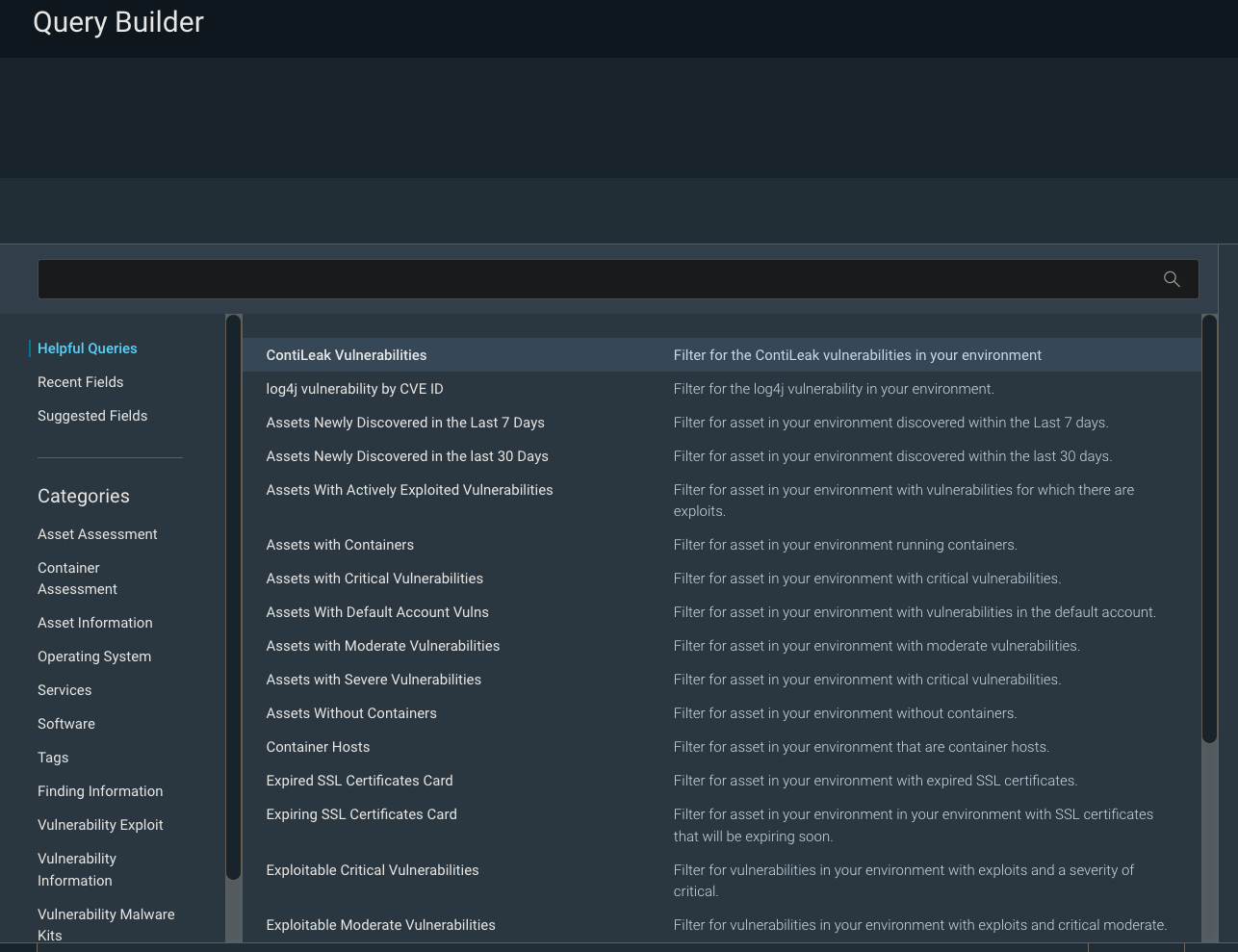
CISA’s KEV catalog is part of the agency’s binding operative directive that has reporting requirements for federal agencies and civilian contractors. The recent ContiLeaks revealed over 30 vulns that are now a part of CISA’s KEV. While users could always build a query in IVM to identify these vulns, doing so is time-consuming and can be prone to error. The ContiLeaks Helpful Query takes out the manual effort and lets customers easily locate 30+ ContiLeaks vulnerabilities in their environments. When the query is loaded into our Specific Vulnerability Dashboard template, it can give an at-a-glance view of the company’s risk posture as it relates to the Conti threat. In addition to helping customers identify the exploited vulnerabilities in their environment, the update will also help them stay within the bounds of CISA’s operative directive.
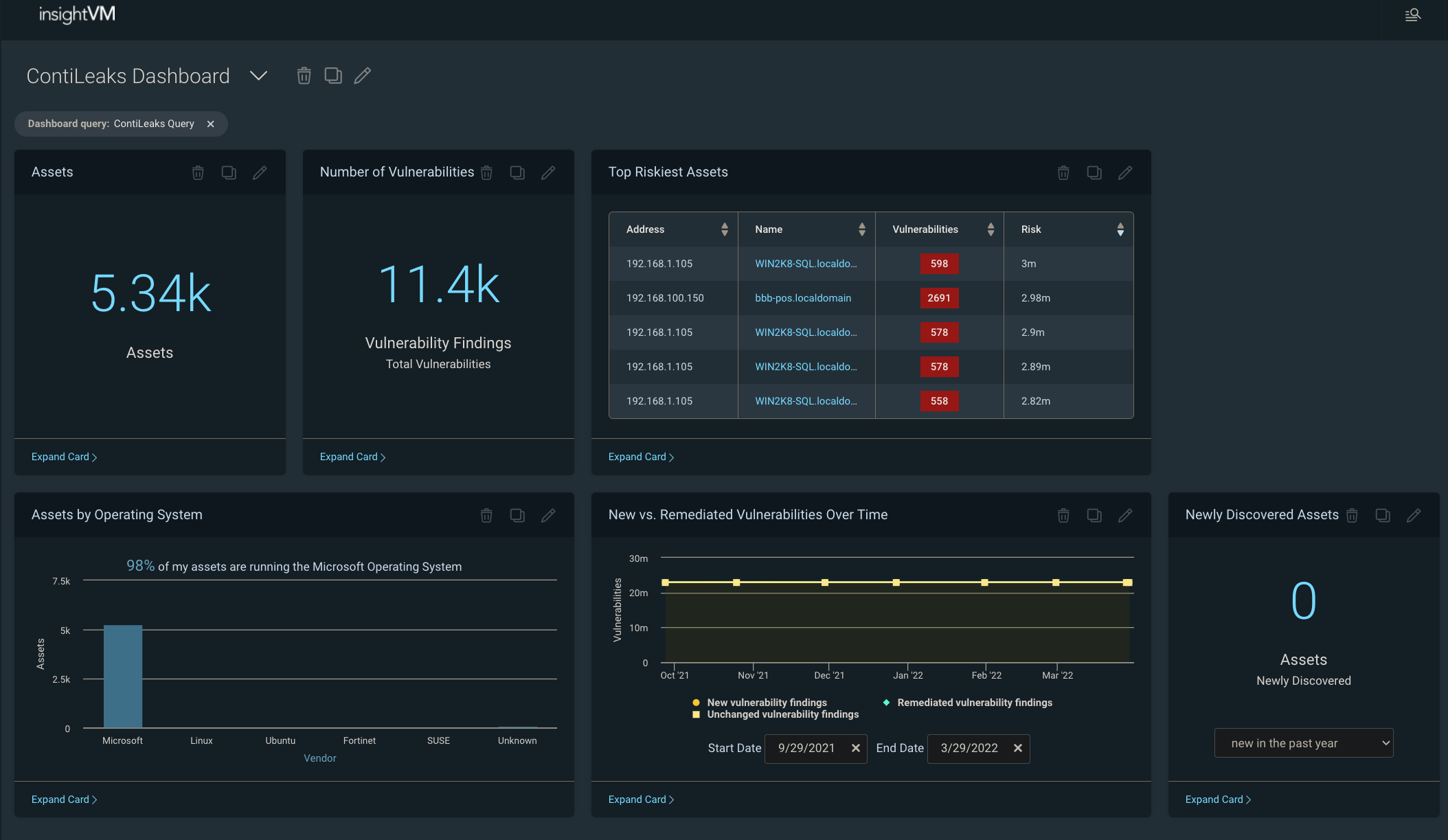
[InsightVM] Threat feed dashboard now includes CISA’s KEV catalog
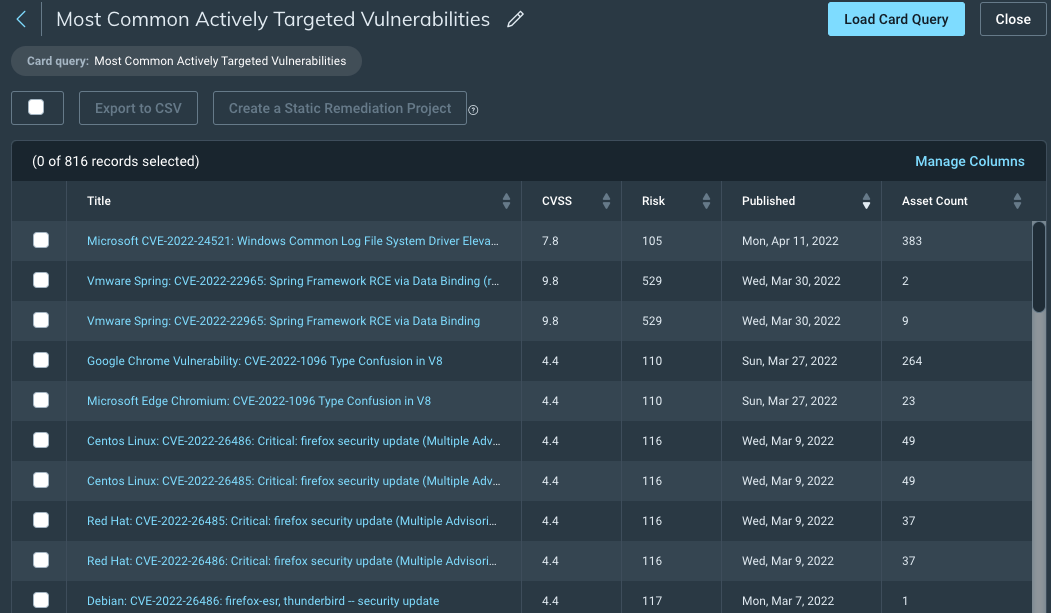
While we are on the topic of CISA, you will be excited to learn that we have expanded the scope of vulnerabilities tracked to incorporate CISA’s KEV catalog in the InsightVM Threat Feed Dashboard, including the Assets With Actively Targeted Vulnerabilities card and theMost Common Actively Targeted Vulnerabilities card. The CISA inclusion makes it easy to see how exposed your organization is to active threats and inform prioritization decisions around remediation efforts.
We have also added a new “CISA KEV (known exploited vulnerability)” vulnerability category to allow for more targeted scanning (i.e. scanning the environment for CISA KEV entries only). You can also use the CISA KEV category to filter scan reports.
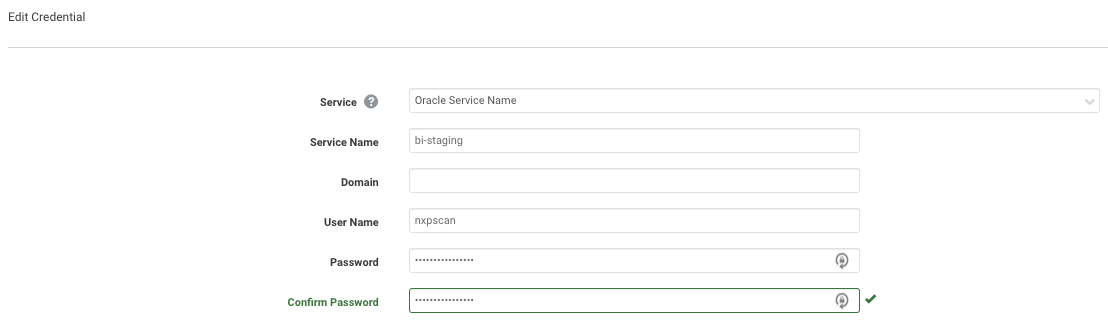
[Insight VM and Nexpose] A new credential type to support scanning Oracle Databases by Service Name
InsightVM and Nexpose customers have always been able to scan Oracle databases using SIDs (system identifiers) but were previously unable to provide a Service Name in the credential. This meant a gap in visibility for Oracle databases that could only be accessed via their Service Name. We were not happy with this limitation. Now, you now configure Oracle Database scans to specify a Service Name instead of an SID (you can still use the SID, if you want!) when authenticating. You now have the visibility into a wider range of deployment configurations of Oracle Database and the ability to configure scan using Service Name or SID.
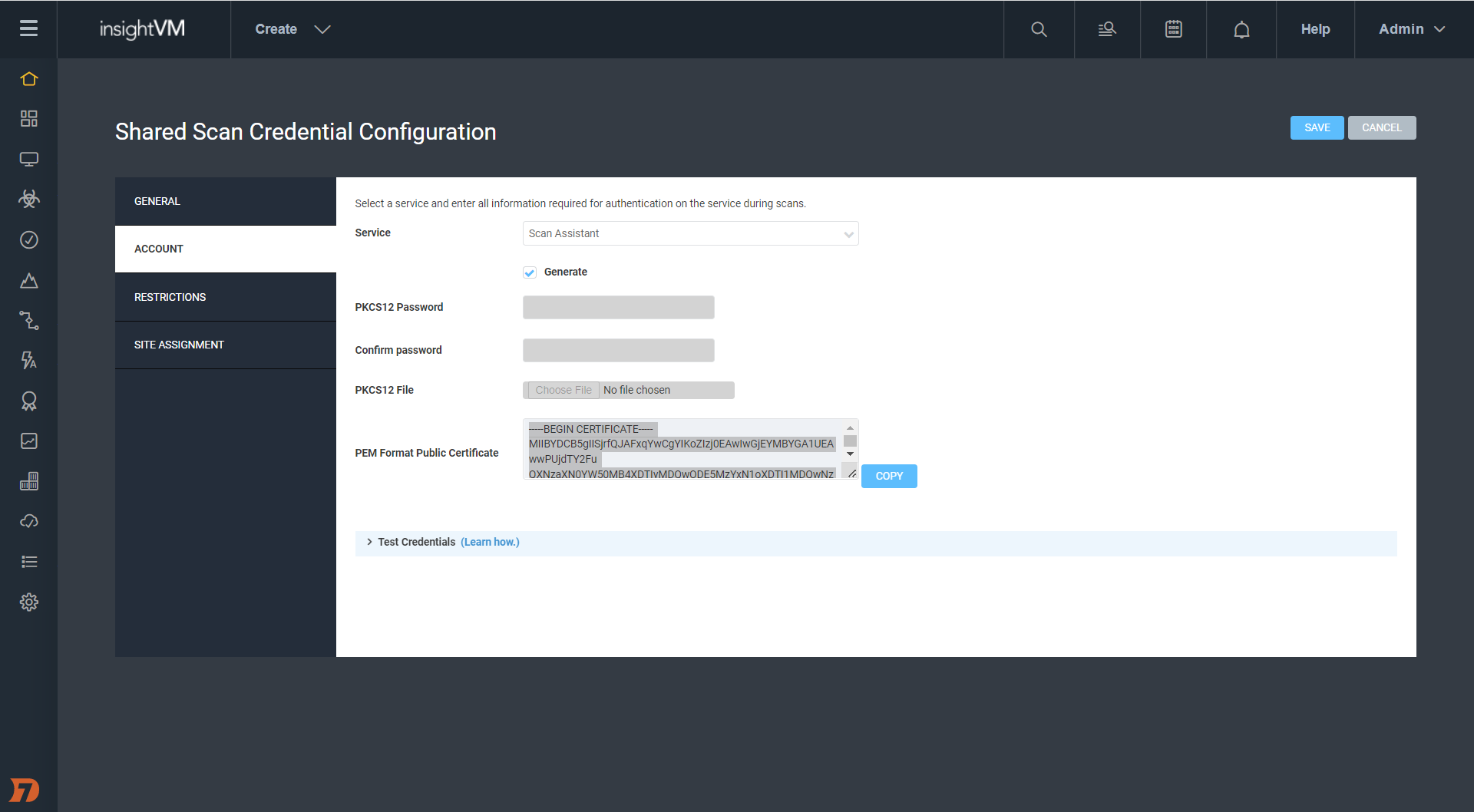
[Insight VM and Nexpose] Automatic Scan Assistant credentials generation
Last year, we introduced Scan Assistant, which alleviates the credential management (for Scan Engine) burden on vulnerability management teams. For the Scan Assistant to communicate with the Scan Engine, it requires digital certificates to be manually created and deployed on both the target assets and the Nexpose / IVM Security Console. Manually creating the public / private key pair is a complex and error-prone process.
With this update, we are taking some more burden off the vulnerability management teams. You can now use the Shared Credentials management UI to automatically generate Scan Assistant credentials. This not only reduces the technical expertise and time required to manage Scan Assistant credentials but also makes for a user-friendly experience for you.
Learn more in our recent blog post on passwordless scanning.
[Insight VM and Nexpose] Log4Shell mitigation checks
The product improvements list would be incomplete without an update on Log4Shell.
If you are vulnerable to Log4Shell, you can edit the JAR files on a system to take out the vulnerable code and thus not get exploited. However, it is difficult to keep a check on this manually. This update adds that extra capability to not only look at the version of Log4j that was present in your environment but also check if it has been mitigated — i.e., if the vulnerable code is removed.
Authenticated scans and Agent-based assessments can now determine whether the JNDILookup class removal mitigation for Log4Shell has been applied to Log4j JAR files on Windows systems. This will reduce the number of reports of the vulnerability on systems that are not exploitable. We also added an Obsolete Software vulnerability check for Log4j 1.x, which will let you find obsolete versions of Log4j in your environment.
Stay in charge
As always, we hope these updates will make it easier for you to stay ahead of vulnerabilities.
It almost felt like the quarter might end on a calm note, but then the world of cybersecurity never has a dull moment. The end of the quarter saw Spring4Shell, another zero-day vulnerability in the Spring Core module of Spring Framework. Learn more about Rapid7 response to this vulnerability and how we are working around the clock to help our customers protect their own environments from Spring4Shell.
Additional reading:
- InsightVM Release Notes
- Widespread Exploitation of Critical Remote Code Execution in Apache Log4j
- The Rapid7 Annual Vulnerability Intelligence Report Webcast
NEVER MISS A BLOG
Get the latest stories, expertise, and news about security today.
Subscribe
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C