
Patch Tuesday - October 2022
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H

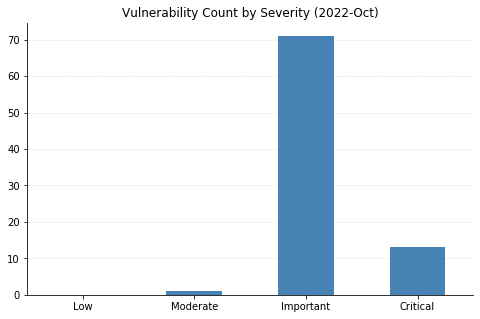
The October batch of CVEs published by Microsoft includes 96 vulnerabilities, including 12 fixed earlier this month that affect the Chromium project used by their Edge browser.
Top of mind for many this month is whether Microsoft would patch the two Exchange Server zero-day vulnerabilities (CVE-2022-41040 and CVE-2022-41082) disclosed at the end of September. While Microsoft was relatively quick to acknowledge the vulnerabilities and provide mitigation steps, their guidance has continually changed as the recommended rules to block attack traffic get bypassed. This whack-a-mole approach seems likely to continue until a proper patch addressing the root causes is available; unfortunately, it doesn’t look like that will be happening today. Thankfully, the impact should be more limited than 2021’s ProxyShell and ProxyLogon vulnerabilities due to attackers needing to be authenticated to the server for successful exploitation. Reports are also surfacing about an additional zero-day distinct from these being used in ransomware attacks; however, these have not yet been substantiated.
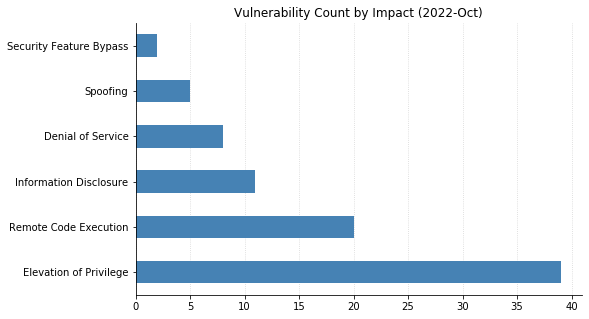
Microsoft did address two other zero-day vulnerabilities with today’s patches. CVE-2022-41033, an Elevation of Privilege vulnerability affecting the COM+ Event System Service in all supported versions of Windows, has been seen exploited in the wild. CVE-2022-41043 is an Information Disclosure vulnerability affecting Office for Mac that was publicly disclosed but not (yet) seen exploited in the wild.
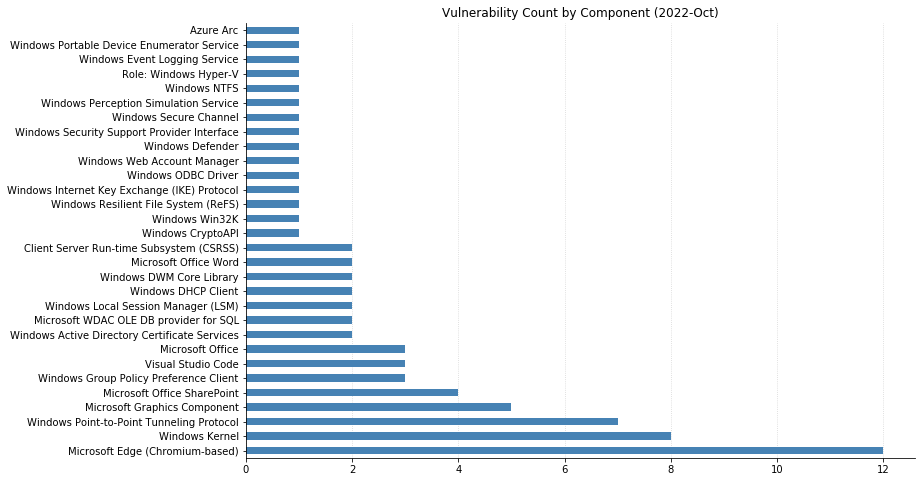
Nine CVEs categorized as Remote Code Execution (RCE) with Critical severity were also patched today – seven of them affect the Point-to-Point Tunneling Protocol, and like those fixed last month, require an attacker to win a race condition to exploit them. CVE-2022-38048 affects all supported versions of Office, and CVE-2022-41038 could allow an attacker authenticated to SharePoint to execute arbitrary code on the server, provided the account has “Manage List” permissions.
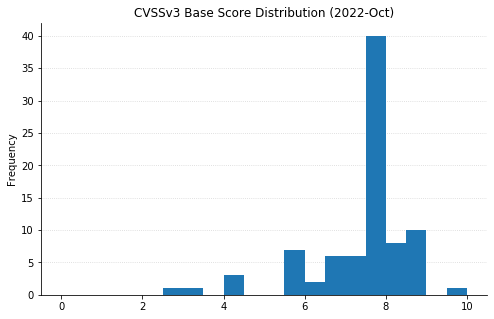
Maxing out the CVSS base score with a 10.0 this month is CVE-2022-37968, an Elevation of Privilege vulnerability in the Azure Arc-enabled Kubernetes cluster Connect component. It’s unclear why Microsoft has assigned such a high score, given that an attacker would need to know the randomly generated external DNS endpoint for an Azure Arc-enabled Kubernetes cluster (arguably making the Attack Complexity “High”). That said, if this condition is met then an unauthenticated user could become a cluster admin and potentially gain control over the Kubernetes cluster. Users of Azure Arc and Azure Stack Edge should check whether auto-updates are turned on, and if not, upgrade manually as soon as possible.
Summary charts
Summary tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-37968 | Azure Arc-enabled Kubernetes cluster Connect Elevation of Privilege Vulnerability | No | No | 10 | Yes |
| CVE-2022-38017 | StorSimple 8000 Series Elevation of Privilege Vulnerability | No | No | 6.8 | Yes |
| CVE-2022-35829 | Service Fabric Explorer Spoofing Vulnerability | No | No | 6.2 | Yes |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-41035 | Microsoft Edge (Chromium-based) Spoofing Vulnerability | No | No | 8.3 | Yes |
| CVE-2022-3373 | Chromium: CVE-2022-3373 Out of bounds write in V8 | No | No | N/A | Yes |
| CVE-2022-3370 | Chromium: CVE-2022-3370 Use after free in Custom Elements | No | No | N/A | Yes |
| CVE-2022-3317 | Chromium: CVE-2022-3317 Insufficient validation of untrusted input in Intents | No | No | N/A | Yes |
| CVE-2022-3316 | Chromium: CVE-2022-3316 Insufficient validation of untrusted input in Safe Browsing | No | No | N/A | Yes |
| CVE-2022-3315 | Chromium: CVE-2022-3315 Type confusion in Blink | No | No | N/A | Yes |
| CVE-2022-3313 | Chromium: CVE-2022-3313 Incorrect security UI in Full Screen | No | No | N/A | Yes |
| CVE-2022-3311 | Chromium: CVE-2022-3311 Use after free in Import | No | No | N/A | Yes |
| CVE-2022-3310 | Chromium: CVE-2022-3310 Insufficient policy enforcement in Custom Tabs | No | No | N/A | Yes |
| CVE-2022-3308 | Chromium: CVE-2022-3308 Insufficient policy enforcement in Developer Tools | No | No | N/A | Yes |
| CVE-2022-3307 | Chromium: CVE-2022-3307 Use after free in Media | No | No | N/A | Yes |
| CVE-2022-3304 | Chromium: CVE-2022-3304 Use after free in CSS | No | No | N/A | Yes |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-41034 | Visual Studio Code Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-41083 | Visual Studio Code Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-41032 | NuGet Client Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-41042 | Visual Studio Code Information Disclosure Vulnerability | No | No | 7.4 | Yes |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-41038 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-41036 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-41037 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-38053 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-41031 | Microsoft Word Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38048 | Microsoft Office Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38049 | Microsoft Office Graphics Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38001 | Microsoft Office Spoofing Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-41043 | Microsoft Office Information Disclosure Vulnerability | No | Yes | 3.3 | Yes |
System Center vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-37971 | Microsoft Windows Defender Elevation of Privilege Vulnerability | No | No | 7.1 | Yes |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-38016 | Windows Local Security Authority (LSA) Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-38045 | Server Service Remote Protocol Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-37984 | Windows WLAN Service Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38003 | Windows Resilient File System Elevation of Privilege | No | No | 7.8 | Yes |
| CVE-2022-38028 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38039 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37995 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37979 | Windows Hyper-V Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37970 | Windows DWM Core Library Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37980 | Windows DHCP Client Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38050 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37983 | Microsoft DWM Core Library Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37998 | Windows Local Session Manager (LSM) Denial of Service Vulnerability | No | No | 7.7 | Yes |
| CVE-2022-37973 | Windows Local Session Manager (LSM) Denial of Service Vulnerability | No | No | 7.7 | Yes |
| CVE-2022-38036 | Internet Key Exchange (IKE) Protocol Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-38027 | Windows Storage Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-38021 | Connected User Experiences and Telemetry Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-37974 | Windows Mixed Reality Developer Tools Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-38046 | Web Account Manager Information Disclosure Vulnerability | No | No | 6.2 | Yes |
| CVE-2022-37965 | Windows Point-to-Point Tunneling Protocol Denial of Service Vulnerability | No | No | 5.9 | Yes |
| CVE-2022-37996 | Windows Kernel Memory Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-38025 | Windows Distributed File System (DFS) Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-38030 | Windows USB Serial Driver Information Disclosure Vulnerability | No | No | 4.3 | Yes |
Windows ESU vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-37982 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-38031 | Microsoft WDAC OLE DB provider for SQL Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-38040 | Microsoft ODBC Driver Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-37976 | Active Directory Certificate Services Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-30198 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-22035 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-24504 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-33634 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-38047 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-38000 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-41081 | Windows Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-37986 | Windows Win32k Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37988 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38037 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38038 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37990 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37991 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37999 | Windows Group Policy Preference Client Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37993 | Windows Group Policy Preference Client Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37994 | Windows Group Policy Preference Client Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37975 | Windows Group Policy Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-38051 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37997 | Windows Graphics Component Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-33635 | Windows GDI+ Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37987 | Windows Client Server Run-time Subsystem (CSRSS) Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-37989 | Windows Client Server Run-time Subsystem (CSRSS) Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-41033 | Windows COM+ Event System Service Elevation of Privilege Vulnerability | Yes | No | 7.8 | Yes |
| CVE-2022-38044 | Windows CD-ROM File System Driver Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-33645 | Windows TCP/IP Driver Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-38041 | Windows Secure Channel Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-34689 | Windows CryptoAPI Spoofing Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-37978 | Windows Active Directory Certificate Services Security Feature Bypass | No | No | 7.5 | Yes |
| CVE-2022-38042 | Active Directory Domain Services Elevation of Privilege Vulnerability | No | No | 7.1 | Yes |
| CVE-2022-38029 | Windows ALPC Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-38033 | Windows Server Remotely Accessible Registry Keys Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35770 | Windows NTLM Spoofing Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-37977 | Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability | No | No | 6.5 | No |
| CVE-2022-38032 | Windows Portable Device Enumerator Service Security Feature Bypass Vulnerability | No | No | 5.9 | Yes |
| CVE-2022-38043 | Windows Security Support Provider Interface Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-37985 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-38026 | Windows DHCP Client Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-38034 | Windows Workstation Service Elevation of Privilege Vulnerability | No | No | 4.3 | Yes |
| CVE-2022-37981 | Windows Event Logging Service Denial of Service Vulnerability | No | No | 4.3 | Yes |
| CVE-2022-38022 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 2.5 | Yes |
10 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H