
Patch Tuesday - August 2022
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C

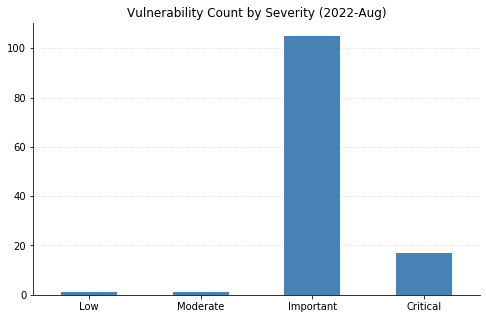
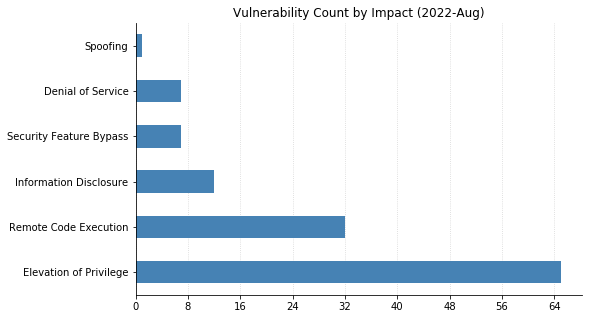
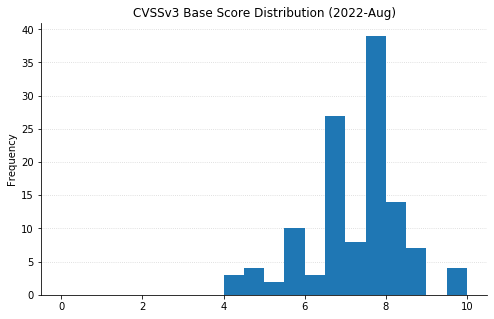
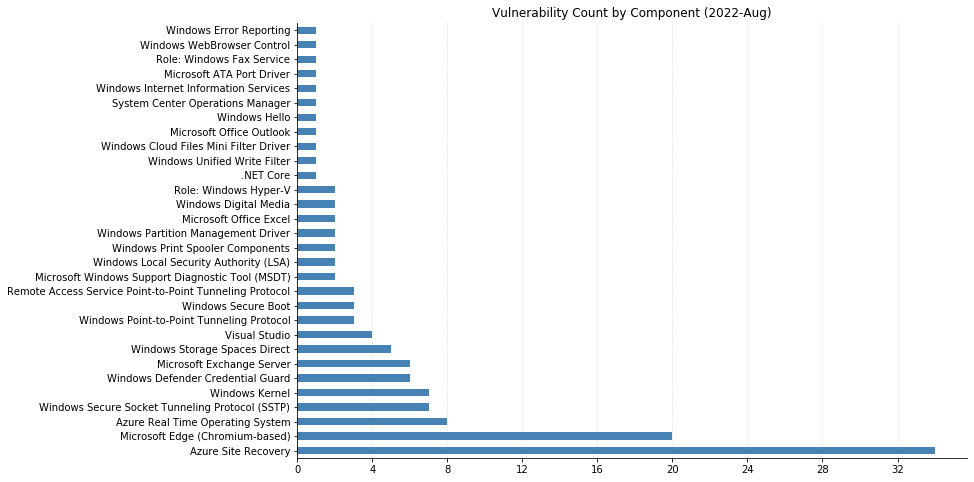
It’s the week of Hacker Summer Camp in Las Vegas, and Microsoft has published fixes for 141 separate vulnerabilities in their swath of August updates. This is a new monthly record by raw CVE count, but from a patching perspective, the numbers are slightly less dire. 20 CVEs affect their Chromium-based Edge browser, and 34 affect Azure Site Recovery (up from 32 CVEs affecting that product last month). As usual, OS-level updates will address a lot of these, but note that some extra configuration is required to fully protect Exchange Server this month.
There is one 0-day being patched this month. CVE-2022-34713 is a remote code execution (RCE) vulnerability affecting the Microsoft Windows Support Diagnostic Tool (MSDT) – it carries a CVSSv3 base score of 7.8, as it requires convincing a potential victim to open a malicious file. The advisory indicates that this CVE is a variant of the “Dogwalk” vulnerability, which made news alongside Follina (CVE-2022-30190) back in May.
Publicly disclosed, but not (yet) exploited is CVE-2022-30134, an Information Disclosure vulnerability affecting Exchange Server. In this case, simply patching is not sufficient to protect against attackers being able to read targeted email messages. Administrators should enable Extended Protection in order to fully remediate this vulnerability, as well as the five other vulnerabilities affecting Exchange this month. Details about how to accomplish this are available via the Exchange Blog.
Microsoft also patched several flaws affecting Remote Access Server (RAS). The most severe of these (CVE-2022-30133 and CVE-2022-35744) are related to Windows Point-to-Point Tunneling Protocol and could allow RCE simply by sending a malicious connection request to a server. Seven CVEs affecting the Windows Secure Socket Tunneling Protocol (SSTP) on RAS were also fixed this month: six RCEs and one Denial of Service. If you have RAS in your environment but are unable to patch immediately, consider blocking traffic on port 1723 from your network.
Vulnerabilities affecting Windows Network File System (NFS) have been trending in recent months, and today sees Microsoft patching CVE-2022-34715 (RCE, CVSS 9.8) affecting NFSv4.1 on Windows Server 2022.
This is the worst of it. One last vulnerability to highlight: CVE-2022-35797 is a Security Feature Bypass in Windows Hello – Microsoft’s biometric authentication mechanism for Windows 10. Successful exploitation requires physical access to a system, but would allow an attacker to bypass a facial recognition check.
Summary charts
Summary tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-35802 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-30175 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-30176 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34687 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35773 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35779 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35806 | Azure RTOS GUIX Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35772 | Azure Site Recovery Remote Code Execution Vulnerability | No | No | 7.2 | Yes |
| CVE-2022-35824 | Azure Site Recovery Remote Code Execution Vulnerability | No | No | 7.2 | Yes |
| CVE-2022-33646 | Azure Batch Node Agent Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-35780 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35781 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35799 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35775 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35801 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35807 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35808 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35782 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35809 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35784 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35810 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35811 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35785 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35786 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35813 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35788 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35814 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35789 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35815 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35790 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35816 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35817 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35791 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35818 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35819 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-35776 | Azure Site Recovery Denial of Service Vulnerability | No | No | 6.2 | Yes |
| CVE-2022-34685 | Azure RTOS GUIX Studio Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34686 | Azure RTOS GUIX Studio Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-35774 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 4.9 | Yes |
| CVE-2022-35800 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 4.9 | Yes |
| CVE-2022-35787 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 4.9 | Yes |
| CVE-2022-35821 | Azure Sphere Information Disclosure Vulnerability | No | No | 4.4 | Yes |
| CVE-2022-35783 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 4.4 | Yes |
| CVE-2022-35812 | Azure Site Recovery Elevation of Privilege Vulnerability | No | No | 4.4 | Yes |
Browser vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-33649 | Microsoft Edge (Chromium-based) Security Feature Bypass Vulnerability | No | No | 9.6 | Yes |
| CVE-2022-33636 | Microsoft Edge (Chromium-based) Remote Code Execution Vulnerability | No | No | 8.3 | Yes |
| CVE-2022-35796 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-2624 | Chromium: CVE-2022-2624 Heap buffer overflow in PDF | No | No | N/A | Yes |
| CVE-2022-2623 | Chromium: CVE-2022-2623 Use after free in Offline | No | No | N/A | Yes |
| CVE-2022-2622 | Chromium: CVE-2022-2622 Insufficient validation of untrusted input in Safe Browsing | No | No | N/A | Yes |
| CVE-2022-2621 | Chromium: CVE-2022-2621 Use after free in Extensions | No | No | N/A | Yes |
| CVE-2022-2619 | Chromium: CVE-2022-2619 Insufficient validation of untrusted input in Settings | No | No | N/A | Yes |
| CVE-2022-2618 | Chromium: CVE-2022-2618 Insufficient validation of untrusted input in Internals | No | No | N/A | Yes |
| CVE-2022-2617 | Chromium: CVE-2022-2617 Use after free in Extensions API | No | No | N/A | Yes |
| CVE-2022-2616 | Chromium: CVE-2022-2616 Inappropriate implementation in Extensions API | No | No | N/A | Yes |
| CVE-2022-2615 | Chromium: CVE-2022-2615 Insufficient policy enforcement in Cookies | No | No | N/A | Yes |
| CVE-2022-2614 | Chromium: CVE-2022-2614 Use after free in Sign-In Flow | No | No | N/A | Yes |
| CVE-2022-2612 | Chromium: CVE-2022-2612 Side-channel information leakage in Keyboard input | No | No | N/A | Yes |
| CVE-2022-2611 | Chromium: CVE-2022-2611 Inappropriate implementation in Fullscreen API | No | No | N/A | Yes |
| CVE-2022-2610 | Chromium: CVE-2022-2610 Insufficient policy enforcement in Background Fetch | No | No | N/A | Yes |
| CVE-2022-2606 | Chromium: CVE-2022-2606 Use after free in Managed devices API | No | No | N/A | Yes |
| CVE-2022-2605 | Chromium: CVE-2022-2605 Out of bounds read in Dawn | No | No | N/A | Yes |
| CVE-2022-2604 | Chromium: CVE-2022-2604 Use after free in Safe Browsing | No | No | N/A | Yes |
| CVE-2022-2603 | Chromium: CVE-2022-2603 Use after free in Omnibox | No | No | N/A | Yes |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-35777 | Visual Studio Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-35825 | Visual Studio Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-35826 | Visual Studio Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-35827 | Visual Studio Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-34716 | .NET Spoofing Vulnerability | No | No | 5.9 | Yes |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-30133 | Windows Point-to-Point Protocol (PPP) Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-35744 | Windows Point-to-Point Protocol (PPP) Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-34691 | Active Directory Domain Services Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-34714 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-35745 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-35752 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-35753 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-34702 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-35767 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-34706 | Windows Local Security Authority (LSA) Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34707 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35768 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35756 | Windows Kerberos Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35751 | Windows Hyper-V Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35795 | Windows Error Reporting Service Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35820 | Windows Bluetooth Driver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35750 | Win32k Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34713 | Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability | Yes | Yes | 7.8 | Yes |
| CVE-2022-35743 | Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35760 | Microsoft ATA Port Driver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-30194 | Windows WebBrowser Control Remote Code Execution Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-35769 | Windows Point-to-Point Protocol (PPP) Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-35793 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.3 | Yes |
| CVE-2022-34690 | Windows Fax Service Elevation of Privilege Vulnerability | No | No | 7.1 | Yes |
| CVE-2022-35759 | Windows Local Security Authority (LSA) Denial of Service Vulnerability | No | No | 6.5 | No |
| CVE-2022-35747 | Windows Point-to-Point Protocol (PPP) Denial of Service Vulnerability | No | No | 5.9 | Yes |
| CVE-2022-35758 | Windows Kernel Memory Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34708 | Windows Kernel Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34701 | Windows Secure Socket Tunneling Protocol (SSTP) Denial of Service Vulnerability | No | No | 5.3 | No |
Exchange Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-21980 | Microsoft Exchange Server Elevation of Privilege Vulnerability | No | No | 8 | Yes |
| CVE-2022-24516 | Microsoft Exchange Server Elevation of Privilege Vulnerability | No | No | 8 | Yes |
| CVE-2022-24477 | Microsoft Exchange Server Elevation of Privilege Vulnerability | No | No | 8 | Yes |
| CVE-2022-30134 | Microsoft Exchange Information Disclosure Vulnerability | No | Yes | 7.6 | Yes |
| CVE-2022-34692 | Microsoft Exchange Information Disclosure Vulnerability | No | No | 5.3 | Yes |
| CVE-2022-21979 | Microsoft Exchange Information Disclosure Vulnerability | No | No | 4.8 | Yes |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-34717 | Microsoft Office Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-33648 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35742 | Microsoft Outlook Denial of Service Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-33631 | Microsoft Excel Security Feature Bypass Vulnerability | No | No | 7.3 | Yes |
System Center Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-33640 | System Center Operations Manager: Open Management Infrastructure (OMI) Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-34715 | Windows Network File System Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-35804 | SMB Client and Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-35761 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 8.4 | Yes |
| CVE-2022-35766 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-35794 | Windows Secure Socket Tunneling Protocol (SSTP) Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-34699 | Windows Win32k Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-33670 | Windows Partition Management Driver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34703 | Windows Partition Management Driver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34696 | Windows Hyper-V Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35746 | Windows Digital Media Receiver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35749 | Windows Digital Media Receiver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-34705 | Windows Defender Credential Guard Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35771 | Windows Defender Credential Guard Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35762 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35763 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35764 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35765 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-35792 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-30144 | Windows Bluetooth Service Remote Code Execution Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-35748 | HTTP.sys Denial of Service Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-35755 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.3 | Yes |
| CVE-2022-35757 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | No | No | 7.3 | Yes |
| CVE-2022-35754 | Unified Write Filter Elevation of Privilege Vulnerability | No | No | 6.7 | Yes |
| CVE-2022-35797 | Windows Hello Security Feature Bypass Vulnerability | No | No | 6.1 | Yes |
| CVE-2022-34709 | Windows Defender Credential Guard Security Feature Bypass Vulnerability | No | No | 6 | Yes |
| CVE-2022-30197 | Windows Kernel Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34710 | Windows Defender Credential Guard Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34712 | Windows Defender Credential Guard Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34704 | Windows Defender Credential Guard Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-34303 | CERT/CC: CVE-20220-34303 Crypto Pro Boot Loader Bypass | No | No | N/A | Yes |
| CVE-2022-34302 | CERT/CC: CVE-2022-34302 New Horizon Data Systems Inc Boot Loader Bypass | No | No | N/A | Yes |
| CVE-2022-34301 | CERT/CC: CVE-2022-34301 Eurosoft Boot Loader Bypass | No | No | N/A | Yes |
NEVER MISS A BLOG
Get the latest stories, expertise, and news about security today.
Subscribe
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C