
Patch Tuesday - May 2022
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C

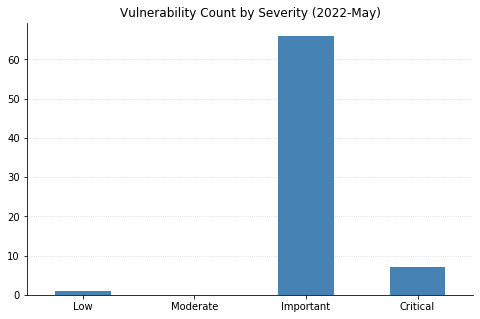
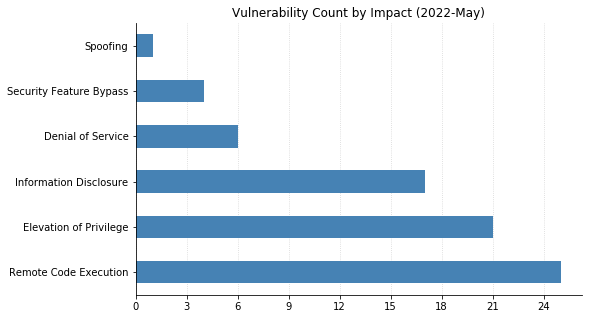
This month is par for the course in terms of both number and severity of vulnerabilities being patched by Microsoft. That means there’s plenty of work to be done by system and network administrators, as usual.
There is one 0-day this month: CVE-2022-26925, a Spoofing vulnerability in the Windows Local Security Authority (LSA) subsystem, which allows attackers able to perform a man-in-the-middle attack to force domain controllers to authenticate to the attacker using NTLM authentication. This is very bad news when used in conjunction with an NTLM relay attack, potentially leading to remote code execution (RCE). This bug affects all supported versions of Windows, but Domain Controllers should be patched on a priority basis before updating other servers.
Two other CVEs were also publicly disclosed before today’s releases, though they have not yet been seen exploited in the wild. CVE-2022-22713 is a denial-of-service vulnerability that affects Hyper-V servers running relatively recent versions of Windows (20H2 and later). CVE-2022-29972 is a Critical RCE that affects the Amazon Redshift ODBC driver used by Microsoft’s Self-hosted Integration Runtime (a client agent that enables on-premises data sources to exchange data with cloud services such as Azure Data Factory and Azure Synapse Pipelines). This vulnerability also prompted Microsoft to publish their first guidance-based advisory of the year, ADV220001, indicating their plans to strengthen tenant isolation in their cloud services without actually providing any specific details or actions to be taken by customers.
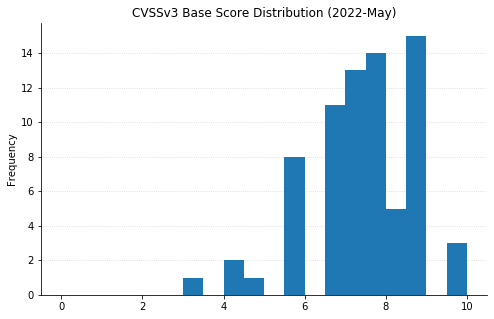
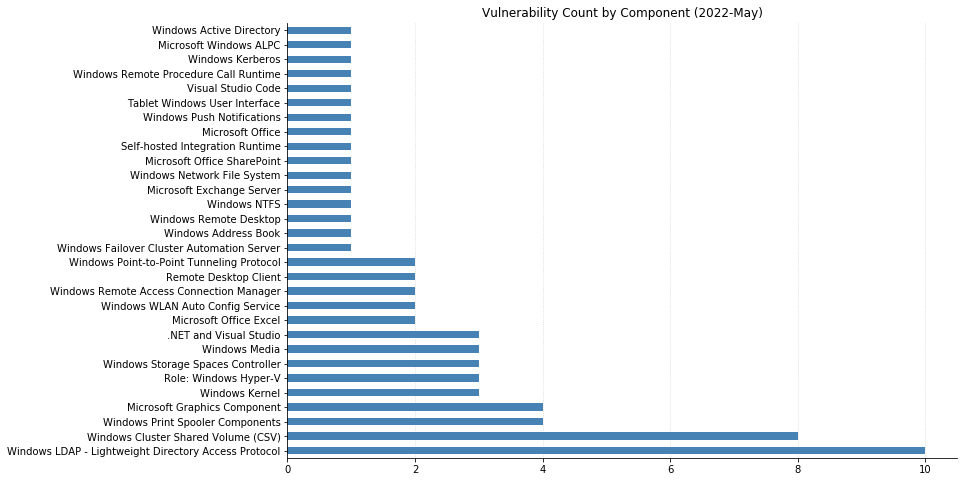
All told, 74 CVEs were fixed this month, the vast majority of which affect functionality within the Windows operating system. Other notable vulnerabilities include CVE-2022-21972 and CVE-2022-23270, critical RCEs in the Point-to-Point Tunneling Protocol. Exploitation requires attackers to win a race condition, which increases the complexity, but if you have any RAS servers in your environment, patch sooner rather than later.
CVE-2022-26937 carries a CVSSv3 score of 9.8 and affects services using the Windows Network File System (NFS). This can be mitigated by disabling NFSV2 and NFSV3 on the server; however, this may cause compatibility issues, and upgrading is highly recommended.
CVE-2022-22017 is yet another client-side Remote Desktop Protocol (RDP) vulnerability. While not as worrisome as when an RCE affects RDP servers, if a user can be enticed to connect to a malicious RDP server via social engineering tactics, an attacker will gain RCE on their system.
Sharepoint Server administrators should be aware of CVE-2022-29108, a post-authentication RCE fixed today. Exchange admins have CVE-2022-21978 to worry about, which could allow an attacker with elevated privileges on an Exchange server to gain the rights of a Domain Administrator.
A host of Lightweight Directory Access Protocol (LDAP) vulnerabilities were also addressed this month, including CVE-2022-22012 and CVE-2022-29130 – both RCEs that, thankfully, are only exploitable if the MaxReceiveBuffer LDAP policy is set to a value higher than the default value.
Although there are no browser vulnerabilities this month, two RCEs affecting Excel (CVE-2022-29109 and CVE-2022-29110) and one Security Feature Bypass affecting Office (CVE-2022-29107) mean there is still some endpoint application patching to do.
Summary charts
Summary tables
Azure vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-29972 | Insight Software: CVE-2022-29972 Magnitude Simba Amazon Redshift ODBC Driver | No | Yes | N/A | Yes |
Developer Tools vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-29148 | Visual Studio Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-30129 | Visual Studio Code Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-23267 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-29117 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-29145 | .NET and Visual Studio Denial of Service Vulnerability | No | No | 7.5 | No |
| CVE-2022-30130 | .NET Framework Denial of Service Vulnerability | No | No | 3.3 | No |
ESU Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-26935 | Windows WLAN AutoConfig Service Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29121 | Windows WLAN AutoConfig Service Denial of Service Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-26936 | Windows Server Service Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-22015 | Windows Remote Desktop Protocol (RDP) Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29103 | Windows Remote Access Connection Manager Elevation of Privilege Vulnerability | No | No | 7.8 | No |
| CVE-2022-29132 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.8 | No |
| CVE-2022-26937 | Windows Network File System Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-26925 | Windows LSA Spoofing Vulnerability | Yes | Yes | 8.1 | Yes |
| CVE-2022-22012 | Windows LDAP Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-29130 | Windows LDAP Remote Code Execution Vulnerability | No | No | 9.8 | Yes |
| CVE-2022-22013 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | No |
| CVE-2022-22014 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | No |
| CVE-2022-29128 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29129 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29137 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | No |
| CVE-2022-29139 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29141 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | No |
| CVE-2022-26931 | Windows Kerberos Elevation of Privilege Vulnerability | No | No | 7.5 | Yes |
| CVE-2022-26934 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29112 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-22011 | Windows Graphics Component Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29115 | Windows Fax Service Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-26926 | Windows Address Book Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-22019 | Remote Procedure Call Runtime Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-21972 | Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-23270 | Point-to-Point Tunneling Protocol Remote Code Execution Vulnerability | No | No | 8.1 | Yes |
| CVE-2022-29105 | Microsoft Windows Media Foundation Remote Code Execution Vulnerability | No | No | 7.8 | No |
| CVE-2022-29127 | BitLocker Security Feature Bypass Vulnerability | No | No | 4.2 | Yes |
Exchange Server vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-21978 | Microsoft Exchange Server Elevation of Privilege Vulnerability | No | No | 8.2 | Yes |
Microsoft Office vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-29108 | Microsoft SharePoint Server Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29107 | Microsoft Office Security Feature Bypass Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29109 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-29110 | Microsoft Excel Remote Code Execution Vulnerability | No | No | 7.8 | Yes |
Windows vulnerabilities
| CVE | Title | Exploited? | Publicly disclosed? | CVSSv3 base score | Has FAQ? |
|---|---|---|---|---|---|
| CVE-2022-26930 | Windows Remote Access Connection Manager Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29125 | Windows Push Notifications Apps Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29114 | Windows Print Spooler Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29140 | Windows Print Spooler Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29104 | Windows Print Spooler Elevation of Privilege Vulnerability | No | No | 7.8 | No |
| CVE-2022-22016 | Windows PlayToManager Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-26933 | Windows NTFS Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29131 | Windows LDAP Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29116 | Windows Kernel Information Disclosure Vulnerability | No | No | 4.7 | Yes |
| CVE-2022-29133 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29142 | Windows Kernel Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29106 | Windows Hyper-V Shared Virtual Disk Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-24466 | Windows Hyper-V Security Feature Bypass Vulnerability | No | No | 4.1 | Yes |
| CVE-2022-22713 | Windows Hyper-V Denial of Service Vulnerability | No | Yes | 5.6 | Yes |
| CVE-2022-26927 | Windows Graphics Component Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-29102 | Windows Failover Cluster Information Disclosure Vulnerability | No | No | 5.5 | Yes |
| CVE-2022-29113 | Windows Digital Media Receiver Elevation of Privilege Vulnerability | No | No | 7.8 | Yes |
| CVE-2022-29134 | Windows Clustered Shared Volume Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29120 | Windows Clustered Shared Volume Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29122 | Windows Clustered Shared Volume Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29123 | Windows Clustered Shared Volume Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-29138 | Windows Clustered Shared Volume Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29135 | Windows Cluster Shared Volume (CSV) Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29150 | Windows Cluster Shared Volume (CSV) Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29151 | Windows Cluster Shared Volume (CSV) Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-26913 | Windows Authentication Security Feature Bypass Vulnerability | No | No | 7.4 | Yes |
| CVE-2022-23279 | Windows ALPC Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-29126 | Tablet Windows User Interface Application Core Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-26932 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 8.2 | Yes |
| CVE-2022-26938 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-26939 | Storage Spaces Direct Elevation of Privilege Vulnerability | No | No | 7 | Yes |
| CVE-2022-26940 | Remote Desktop Protocol Client Information Disclosure Vulnerability | No | No | 6.5 | Yes |
| CVE-2022-22017 | Remote Desktop Client Remote Code Execution Vulnerability | No | No | 8.8 | Yes |
| CVE-2022-26923 | Active Directory Domain Services Elevation of Privilege Vulnerability | No | No | 8.8 | Yes |
NEVER MISS A BLOG
Get the latest stories, expertise, and news about security today.
Subscribe
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C