Snapd Race Condition Vulnerability in snap-confine’s must_mkdir_and_open_with_perms() (CVE-2022-3328)
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
HIGH
Privileges Required
LOW
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H
6.9 Medium
CVSS2
Access Vector
LOCAL
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:L/AC:M/Au:N/C:C/I:C/A:C
The Qualys Threat Research Unit (TRU) has discovered a new vulnerability in snap-confine function on Linux operating systems, a SUID-root program installed by default on Ubuntu. Qualys recommends that security teams apply the patch for this vulnerability as soon as possible.
In February 2022, Qualys Threat Research Unit (TRU) published CVE-2021-44731 in our "Lemmings" advisory. The vulnerability (CVE-2022-3328) was introduced in February 2022 by the patch for CVE-2021-44731)
The Qualys Threat Research Unit (TRU) exploited this bug in Ubuntu Server by combining it with two vulnerabilities in multipathd called Leeloo Multipath (an authorization bypass and a symlink attack, CVE-2022-41974 and CVE-2022-41973), to obtain full root privileges.
What is snap-confine?
The snap-confine program is used internally by snapd to construct the execution environment for snap applications, an internal tool for confining snappy applications.
Potential Impact
Successful exploitation of the three vulnerabilities lets any unprivileged user gain root privileges on the vulnerable device. Qualys security researchers have verified the vulnerability, developed an exploit and obtained full root privileges on default installations of Ubuntu.
As soon as the Qualys Threat Research Unit confirmed the vulnerability, we engaged in responsible vulnerability disclosure and coordinated with vendors and open-source distributions to announce this newly discovered vulnerability.
The technical details of snap-confine vulnerability can be found at:
Disclosure Timeline
- 2022-08-23: Contacted security@ubuntu
- 2022-11-28: Contacted linux-distros@openwall
- 2022-11-30: Coordinated Release Date (17:00 UTC)
Qualys QID Coverage
Qualys has released one (1) QID 377800 at this time, starting with IP scanning versionVULNSIGS-2.5.642-3and Linux Cloud Agent manifest versionlx_manifest-2.5.642.3-2. Should additional QIDs be released, they will be added to the table below as they become available,
| QID | Title | Qualys Release Versions |
|---|---|---|
| 377800 | Snapd Race Condition Vulnerability | VULNSIGS-2.5.642-3 |
| lx_manifest-2.5.642.3-2 |
Discover Vulnerable Linux Servers Using Qualys Cloud Platform
The following instructs current Qualys customers on how to detect snap-confine in their environment.
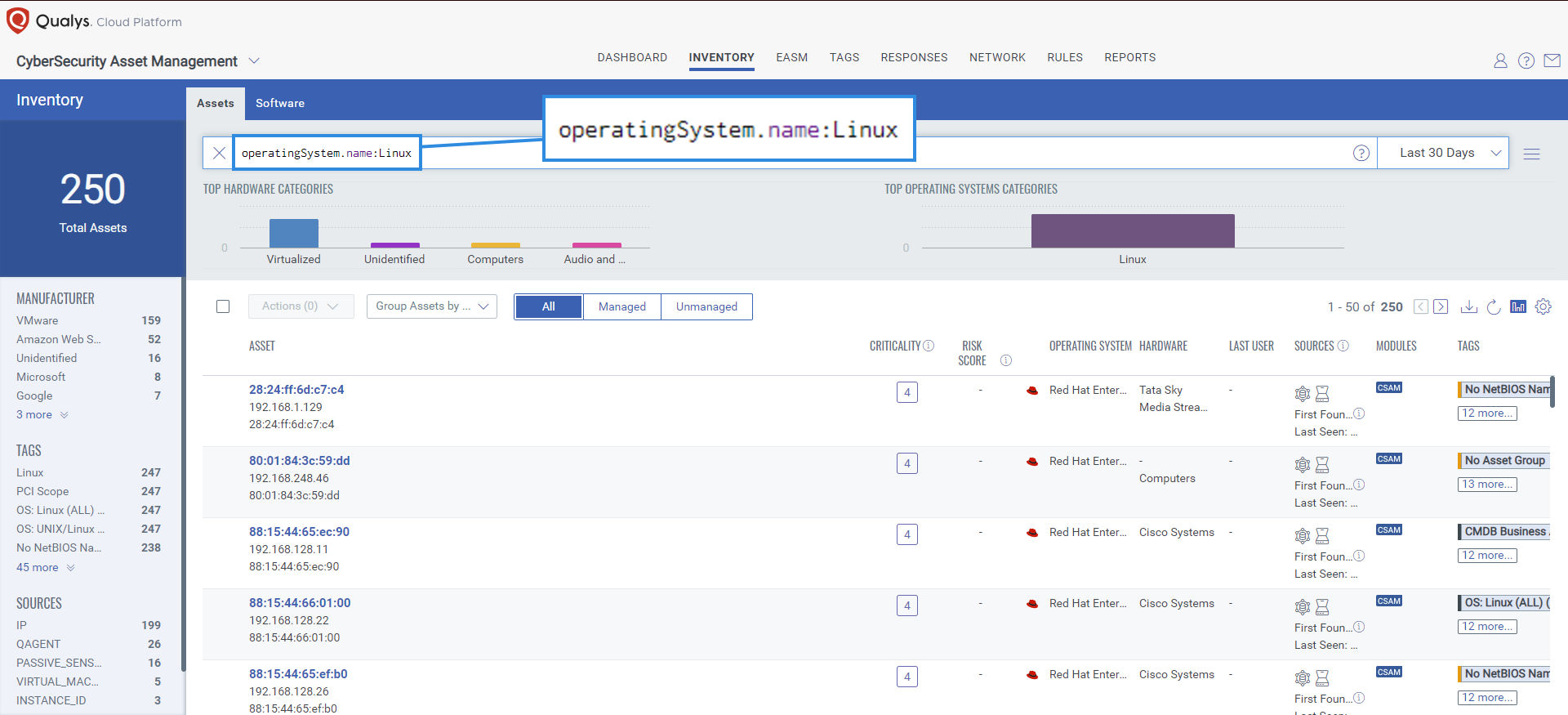
Identify Assets Running Linux OS with Qualys CyberSecurity Asset Management (CSAM)
The first step in managing this critical vulnerability and reducing risk is the identification of all assets running Linux OS. Qualys CyberSecurity Asset Management makes it easy to identify such assets.
operatingSystem.name:”Linux”
Once the hosts are identified, they can be grouped together with a dynamic tag, let’s say: “Linux Servers”. This helps by automatically grouping existing hosts with the above vulnerabilities and any new Linux assets that spin up in your environment. Tagging makes these grouped assets available for querying, reporting, and management throughout the Qualys Cloud Platform.
Prioritize with Qualys Vulnerability Management Detection and Response (VM/VMDR) Based on Risk Threat Indicators (RTIs)
Using Qualys VMDR, the Snap-confine vulnerability can be prioritized using the following real-time threat indicators (RTIs):
-
Predicted_High_Risk
-
Privilege_Escalation
-
Easy_Exploit
-
High_Lateral_Movement
vulnerabilities.vulnerability.cveIds:
CVE-2022-3328
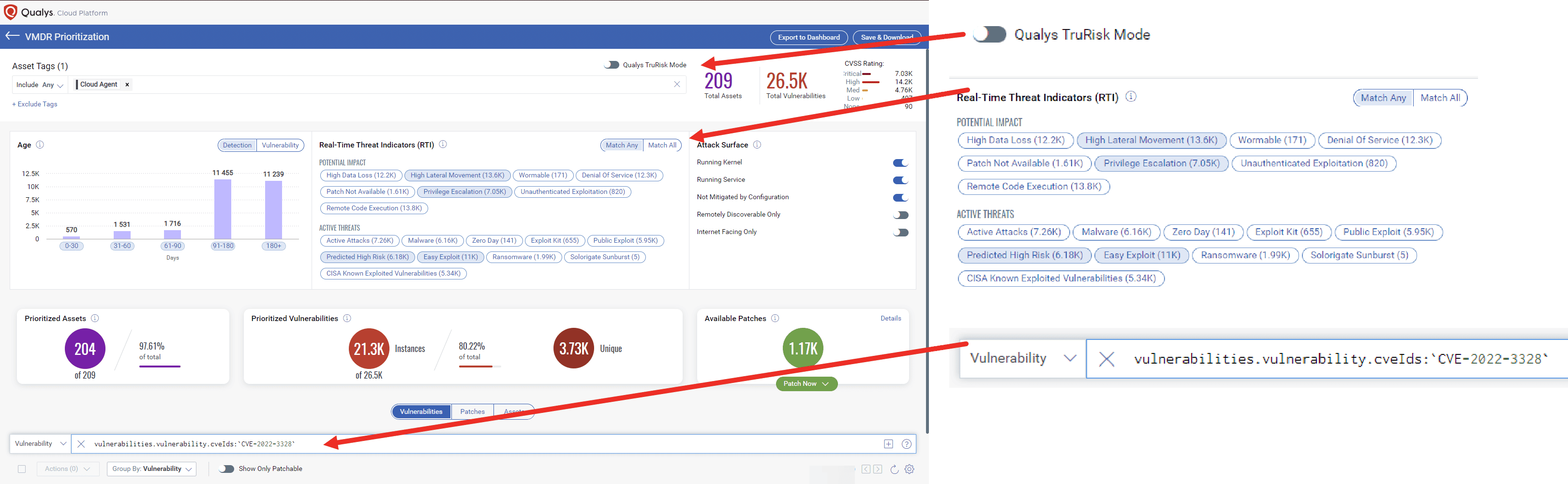 VM/VMDR Prioritization by Risk Threat Indicators (RTIs) and Affected CVE
VM/VMDR Prioritization by Risk Threat Indicators (RTIs) and Affected CVE
Prioritize with Qualys Vulnerability Management Detection and Response (VM/VMDR) LeveragingQualys TruRisk Mode
vulnerabilities.vulnerability.cveIds:`CVE-2022-3328`
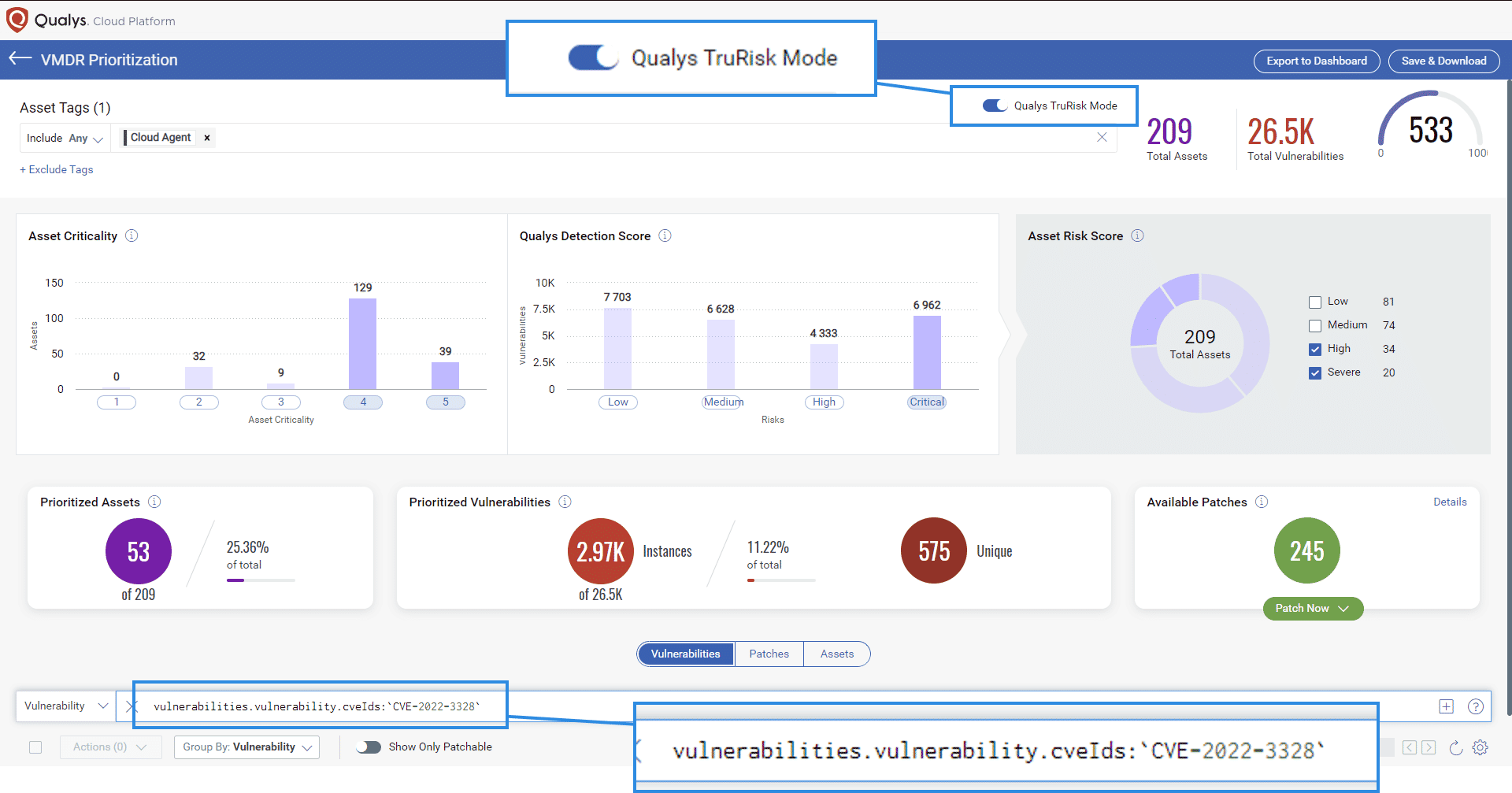 VM/VMDR Prioritization using Qualys Tru Risk and Affected CVE
VM/VMDR Prioritization using Qualys Tru Risk and Affected CVE
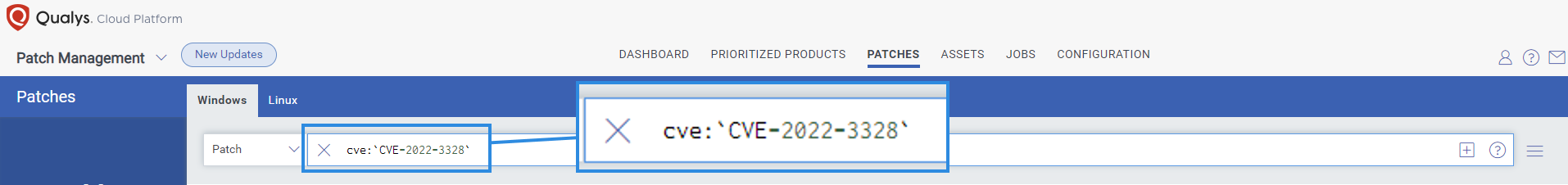
Deploy Patches with Qualys Patch Management (PM)
We expect vendors to release patches for this vulnerability in the short term. Qualys Patch Management can be used to deploy those patches to vulnerable assets when available.
Using the same prioritization based on the RTI method as described above, customers can use the “patch now” button found to the right of the vulnerability to add Snap-confine to a patch job. Once patches are released, Qualys will find the relevant patches for this vulnerability and automatically add those patches to a patch job. This will allow customers to deploy those patches to vulnerable devices, all from the Qualys Cloud Platform.
cve:`CVE-2022-3328`
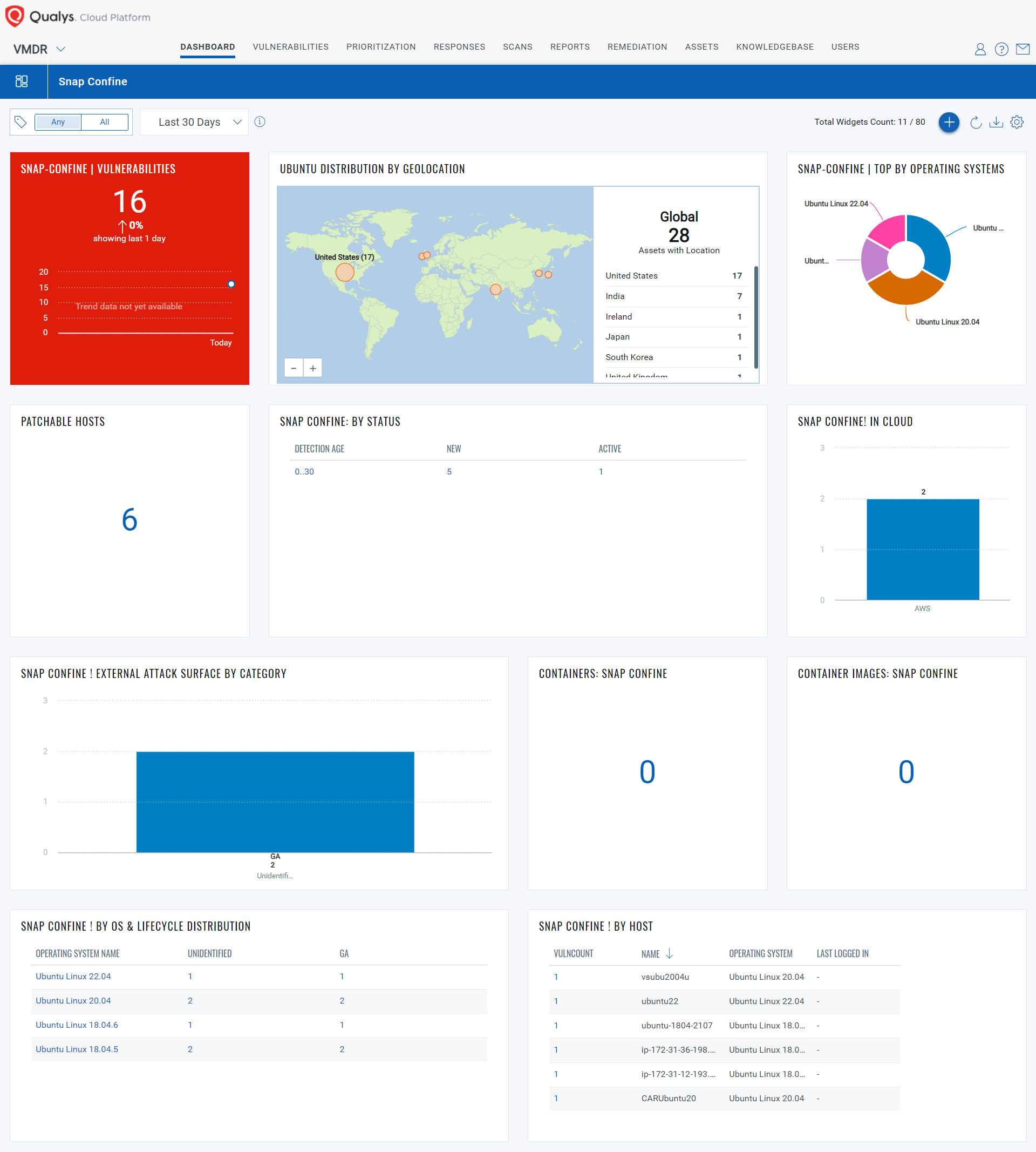
Visualize Exposure and Track Remediation Progress with Qualys Unified Dashboard (UD)
With the Qualys Unified Dashboard, you can track the vulnerability exposure within your organization and view your impacted hosts, their status, distribution across environments, and overall management in real-time, allowing you to see your mean-to-time remediation (MTTR).
View and download the "Snapd Race Condition Vulnerability” dashboardDownload
Vendor References
Frequently Asked Questions (FAQs)
- Will the Qualys Research Team publish exploit code for this vulnerability?
- No., not at this time.
- Are there any mitigations for this vulnerability?
- No.
- Is this vulnerability remotely exploitable?
- No. However, if an attacker can log in as an unprivileged user, the vulnerability can be quickly exploited to gain root privileges.
7.8 High
CVSS3
Attack Vector
LOCAL
Attack Complexity
HIGH
Privileges Required
LOW
User Interaction
NONE
Scope
CHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H
6.9 Medium
CVSS2
Access Vector
LOCAL
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:L/AC:M/Au:N/C:C/I:C/A:C