
June 2022 Patch Tuesday | Microsoft Releases 55 Vulnerabilities with 3 Critical; Adobe Releases 6 Advisories, 46 Vulnerabilities with 40 Critical.
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
Microsoft Patch Tuesday Summary
Microsoft has fixed 55 vulnerabilities (aka flaws) in the June 2022 update, including three (3) vulnerabilities classified as Critical as they allow Remote Code Execution (RCE). This month's Patch Tuesday cumulative Windows update includes the fix for one (1) zero-day vulnerability (CVE-2022-30190). Microsoft also released an advisory for Intel Processor MMIO Stale Data Vulnerabilitie to address four (4) Intel vulnerabilities (Microsoft Advisory 220002, Intel-SA-00615).
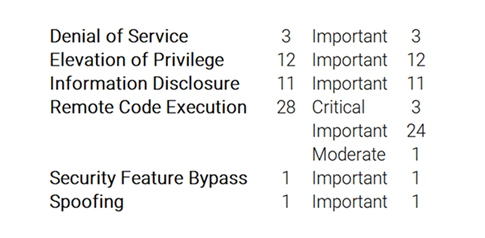
Microsoft has fixed several flaws in its software, including Denial of Service (DoS), Elevation of Privilege, Information Disclosure, Remote Code Execution (RCE), Security Feature Bypass, and Spoofing vulnerabilities.
Many of the vulnerabilities patched this month relate to remote code execution, but there are no reports of active exploitation in the wild with the exception of an update to CVE-2022-30190, a Microsoft Windows Support Diagnostic Tool (MSDT) vulnerability made public in May.
The June 2022 Microsoft vulnerabilities are classified as follows:
 Related Threat Protection Post
Related Threat Protection Post
Notable Microsoft Vulnerabilities Patched
CVE-2022-30190 | Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.8/10.
Microsoft has fixed the widely-exploited Windows Follina MSDT zero-day vulnerability tracked as CVE-2022-30190 in the June 2022 Updates.
The update for this vulnerability is in the June 2022 cumulative Windows Updates. Microsoft strongly recommends that customers install the updates to be fully protected from the vulnerability. Customers whose systems are configured to receive automatic updates do not need to take any further action.
Exploitability Assessment: Exploitation Detected.
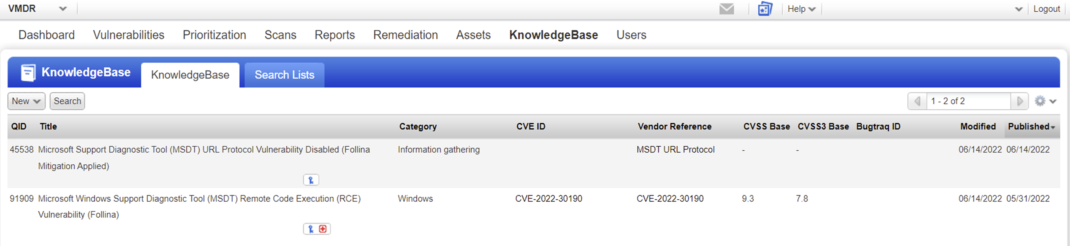
On May 31st Qualys released QID 91909 Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution (RCE) Vulnerability (Follina) (Zero Day).
On June 14th, Microsoft released the patch for this vulnerability in the June 2022 cumulative Windows Updates.
Qualys will modify our existing detection signature to check for the PATCH ONLY and apply a minor title revision to remove the zero-day reference:** QID 91909 Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution (RCE) Vulnerability (Follina).**
Qualys will also release a NEW Information Gathered (IG) detection that will test for the MITIGATION ONLY: QID 45538 Microsoft Support Diagnostic Tool (MSDT) URL Protocol Vulnerability Disabled (Follina Mitigation Enabled).
These updates will be included in the June 14th evening’s Patch Tuesday release cycle.
(VULNSIGS-2.5.504-4, QAGENT-SIGNATURE-SET-2.5.504.4-3, LX_MANIFEST-2.5.504.4-4)
 Examine a potential attack vector as well as technical details of Follina, and chart the ability to detect this new vulnerability using both Qualys Multi-Vector EDR and Qualys Context XDR. Detect the Follina MSDT Vulnerability (CVE-2022-30190) with Qualys Multi-Vector EDR & Context XDR
Examine a potential attack vector as well as technical details of Follina, and chart the ability to detect this new vulnerability using both Qualys Multi-Vector EDR and Qualys Context XDR. Detect the Follina MSDT Vulnerability (CVE-2022-30190) with Qualys Multi-Vector EDR & Context XDR
 Related Threat Protection Post
Related Threat Protection Post
Microsoft Guidance on Intel Processor MMIO Stale Data Vulnerabilities
Microsoft Advisory 220002, Intel-SA-00615
On June 14, 2022, Intel published information about a class of memory-mapped I/O vulnerabilities known as Processor MMIO Stale Data Vulnerabilities.
An attacker who successfully exploited these vulnerabilities might be able to read privileged data across trust boundaries. In shared resource environments (such as exists in some cloud services configurations), these vulnerabilities could allow one virtual machine to improperly access information from another. In non-browsing scenarios on standalone systems, an attacker would need prior access to the system or an ability to run a specially crafted application on the target system to leverage these vulnerabilities.
These vulnerabilities are known as:
- CVE-2022-21123 | Shared Buffer Data Read (SBDR)
- CVE-2022-21125 | Shared Buffer Data Sampling (SBDS)
- CVE-2022-21127 | Special Register Buffer Data Sampling Update (SRBDS Update)
- CVE-2022-21166 | Device Register Partial Write (DRPW)
Important: These vulnerabilities might affect other operating systems and service providers. We advise customers to seek guidance from their respective vendors.
 Related Threat Protection Post
Related Threat Protection Post
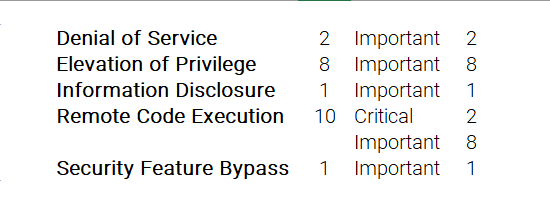
Windows Server 2022 Azure Edition Core Hotpatch (KB5014677) OS Build 20348.770
Windows Server 2022 Azure Edition Core Hotpatch (KB5014677) addresses 22 unique vulnerabilities, ranging in severity from a CVSSv3.1 score of 5.3/10 to 8.8/10, as summarized below.
Microsoft Critical and Important Vulnerability Highlights
This month’s advisory covers multiple Microsoft product families, including Azure, Developer Tools, Edge-Chromium Browser, Microsoft Office, SQL Server, System Center, and Windows.
A total of 25 unique Microsoft products/versions are affected.
Downloads include Azure Hotpatch, Cumulative Updates, Monthly Rollup, Security Only, and Security Updates.
CVE-2022-30136 | Windows Network File System Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 9.8/10.
This vulnerability could be exploited over the network by making an unauthenticated, specially crafted call to a Network File System (NFS) service to trigger a Remote Code Execution (RCE).
Exploitability Assessment: Exploitation More Likely.
CVE-2022-30157 | Microsoft SharePoint Server Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 8.8/10.
In a network-based attack, an attacker would need to have the privileges to create a page on a vulnerable SharePoint server. By creating a site using specific code, the attacker could execute code remotely on the target server.
The attacker must be authenticated and possess the permissions for page creation to be able to exploit this vulnerability.
Exploitability Assessment: Exploitation Less Likely.
CVE-2022-30158 | Microsoft SharePoint Server Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 8.8/10.
An authenticated attacker with access to a server that has Sandboxed Code Service enabled could execute code in the context of the web service account.
The attacker must be authenticated and possess the permissions for page creation to be able to exploit this vulnerability.
Exploitability Assessment: Exploitation Unlikely.
CVE-2022-30165 | Windows Kerberos Elevation of Privilege Vulnerability
This vulnerability has a CVSSv3.1 score of 8.8/10.
Systems configured to activate both of the following features in Windows Server: CredSSP (Credential Security Service Provider) and RCG (Remote Credential Guard) might be vulnerable to this exploit.
An authenticated attacker could exploit this vulnerability to elevate privileges and then spoof the Kerberos login process when a remote credential guard connection is made via CredSSP over the network.
Exploitability Assessment: Exploitation Less Likely.
CVE-2022-30163 | Windows Hyper-V Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 8.5/10.
To exploit this vulnerability, an attacker could run a specially crafted application on a Hyper-V guest that could cause the Hyper-V host operating system to execute arbitrary code.
Successful exploitation of this vulnerability requires an attacker to win a race condition.
In this case, a successful attack could be performed from a low privilege Hyper-V guest. The attacker could traverse the guest's security boundary to execute code on the Hyper-V host execution environment.
Exploitability Assessment: Exploitation Less Likely.
CVE-2022-30164 | Windows Kerberos AppContainer Security Feature Bypass Vulnerability
This vulnerability has a CVSSv3.1 score of 8.4/10.
A low privilege attacker could execute a script within an App Container to request a service ticket and thereby gain elevation to the service privilege.
An attacker could bypass the Kerberos service ticketing feature which performs user access control checks
In this case, a successful attack could be performed from a low privilege AppContainer. The attacker could elevate their privileges and execute code or access resources at a higher integrity level than that of the AppContainer execution environment.
Exploitability Assessment: Exploitation Less Likely.
CVE-2022-30139 | Windows Lightweight Directory Access Protocol (LDAP) Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.5/10.
This vulnerability is only exploitable if the MaxReceiveBuffer LDAP policy is set to a value higher than the default value. Systems with the default value of this policy would not be vulnerable.
For more information, please see LDAP policies.
Successful exploitation of this vulnerability requires an attacker to prepare the target environment to improve exploit reliability.
Exploitability Assessment: Exploitation Less Likely.
CVE-2022-30145 | Windows Encrypting File System (EFS) Remote Code Execution (RCE) Vulnerability
This vulnerability has a CVSSv3.1 score of 7.5/10.
Successful exploitation of this vulnerability requires an attacker to prepare the target environment to improve exploit reliability.
Exploitability Assessment: Exploitation Less Likely.
Microsoft Last But Not Least
Earlier in June, Microsoft released Microsoft Edge (Chromium-based) vulnerabilities on June 9 Microsoft Edge (Chromium-based) Remote Code Execution (RCE) Vulnerability (CVE-2022-22021) and an additional four (4) vulnerabilities on June 13 (CVE-2022-2011, CVE-2022-2010, CVE-2022-2008, CVE-2022-2007).
Adobe Security Bulletins and Advisories
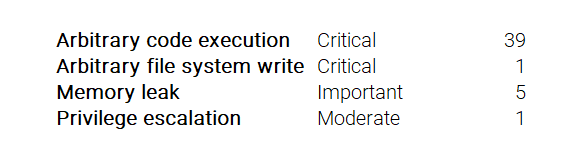
Adobe released six (6) advisories with updates to fix 46 vulnerabilities affecting Adobe Animate, Bridge, Illustrator, InCopy, InDesign, and RoboHelp Server. Of these 46 vulnerabilities, 40 are rated as Critical; ranging in severity from a CVSSv3.1 score of 5.5/10 to 7.8/10, as summarized below.
APSB22-24 | Security updates available for Adobe Animate
This update resolves one (1) Critical vulnerability.
This update resolves a critical vulnerability. Successful exploitation could lead to arbitrary code execution in the context of the current user.
APSB22-25 | Security updates available for Adobe Bridge
This update resolves 11 Critical and one (1) _Important_vulnerability.
This update addresses critical and important vulnerabilities that could lead to arbitrary code execution, arbitrary file system write, and memory leak.
APSB22-26 | Security updates available for Adobe Illustrator
This update resolves 13 Critical, and four (4)**_Important _**vulnerabilities.
This update resolves critical and important vulnerabilities that could lead to arbitrary code execution and memory leak.
APSB22-29 | Security updates available for Adobe InCopy
This update resolves eight (8) Critical vulnerabilities.
This update addresses multiple critical vulnerabilities. Successful exploitation could lead to arbitrary code execution.
APSB22-30 | Security updates available for Adobe InDesign
This update resolves seven (7) Critical vulnerabilities.
This update addresses multiple critical vulnerabilities. Successful exploitation could lead to arbitrary code execution.
APSB22-31 | Security updates available for RoboHelp Server
This update resolves one (1) Moderate vulnerability.
Adobe has released a security hotfix for RoboHelp Server 11 (Update 3) and prior releases. This hotfix resolves a security vulnerability that allows end-users with non-administrative privileges to manipulate API requests and elevate their account privileges to that of a server administrator.
This update resolves a vulnerability rated moderate. Successful exploitation could lead to privilege escalation.
About Qualys Patch Tuesday
Qualys Patch Tuesday QIDs are published as Security Alerts typically late in the evening on the day of Patch Tuesday, followed later by the publication of the monthly queries for the Unified Dashboard: 2022 Patch Tuesday (QID Based) Dashboard by Noon on Wednesday.
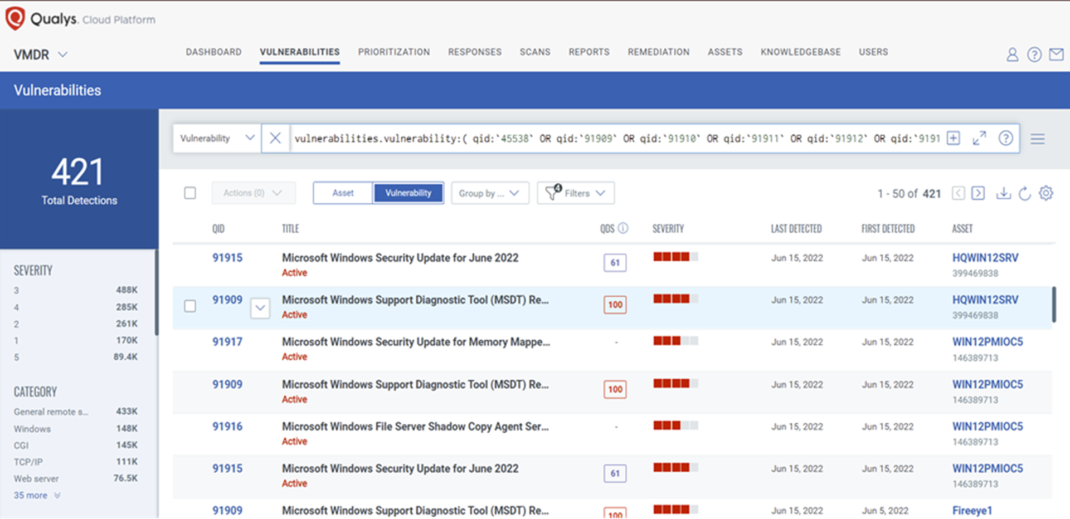
Discover and Prioritize Vulnerabilities in Vulnerability Management Detection Response (VMDR)
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its Knowledge Base (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability:( qid:`45538` OR qid:`91909` OR qid:`91910` OR qid:`91911` OR qid:`91912` OR qid:`91913` OR qid:`91914` OR qid:`91915` OR qid:`91916` OR qid:`91917` OR qid:`91918` OR qid:`91919` OR qid:`110409` OR qid:`110410` OR qid:`376665` OR qid:`376666` )
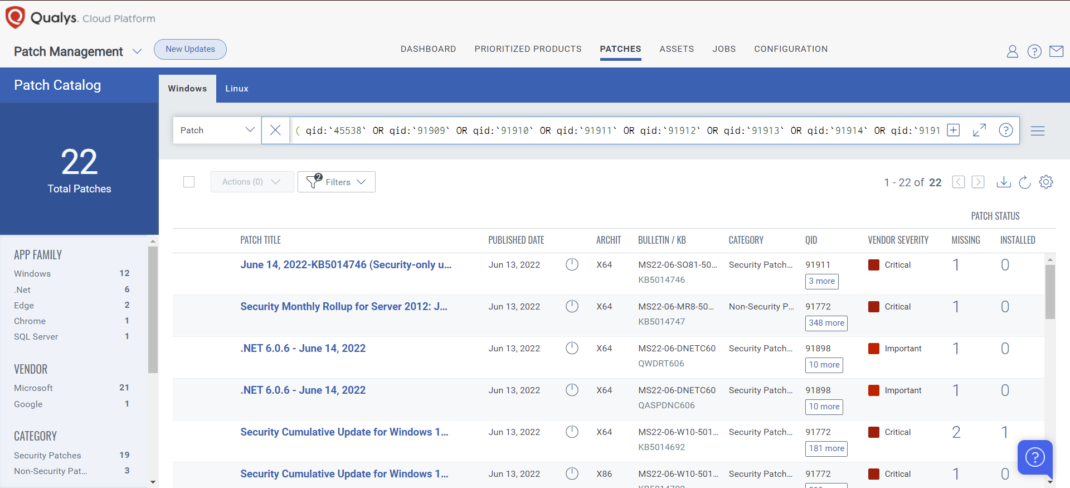
Rapid Response with Patch Management (PM)
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches in one go.
The following QQL will return the missing patches pertaining to this Patch Tuesday:
( qid:`45538` OR qid:`91909` OR qid:`91910` OR qid:`91911` OR qid:`91912` OR qid:`91913` OR qid:`91914` OR qid:`91915` OR qid:`91916` OR qid:`91917` OR qid:`91918` OR qid:`91919` OR qid:`110409` OR qid:`110410` OR qid:`376665` OR qid:`376666` )
Qualys Monthly Webinar Series

The Qualys Research team hosts a monthly webinar series to help our existing customers leverage the seamless integration between Qualys Vulnerability Management Detection Response (VMDR) and Qualys Patch Management. Combining these two solutions can reduce the median time to remediate critical vulnerabilities.
During the webcast, we will discuss this month’s high-impact vulnerabilities, including those that are part of this month's Patch Tuesday alert. We will walk you through the necessary steps to address the key vulnerabilities using Qualys VMDR and Qualys Patch Management.
Join the webinar
This Month in Vulnerabilities & Patches
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C