
Microsoft & Adobe Patch Tuesday (June 2021) – Microsoft 50 Vulnerabilities with 5 Critical, Adobe 21 Critical Vulnerabilities
Microsoft Patch Tuesday – June 2021
Microsoft patched 50 CVEs in their June 2021 Patch Tuesday release, and five of them are rated as critical severity. Six have applicable exploits.
Critical Microsoft Vulnerabilities Patched
CVE-2021-31985 – Microsoft Defender Remote Code Execution Vulnerability
Microsoft released patches addressing a critical RCE vulnerability in its Defender product (CVE-2021-31985). This CVE has a high likelihood of exploitability and is assigned a CVSSv3 base score of 7.8 by the vendor.
CVE-2021-31959 – Scripting Engine Memory Corruption Vulnerability
Microsoft released patches addressing a critical memory corruption vulnerability in the Chakra JScript scripting engine. This vulnerability impacts Windows RT, Windows 7, Windows 8, Windows 10, Windows Server 2008 R2, Windows Server 2012 (R2) and Windows Server 2016. An adversary can exploit this vulnerability when the target user opens a specially crafted file.
CVE-2021-31963 – Microsoft SharePoint Server Remote Code Execution Vulnerability
Microsoft released patches addressing a critical RCE in SharePoint Server. This CVE is assigned a CVSSv3 base score of 7.1 by the vendor.
Six 0-Day Vulnerabilities with Exploits in the Wild Patched
The following vulnerabilities need immediate attention for patching since they have active exploits in the wild:
CVE-2021-33742 – Windows MSHTML Platform Remote Code Execution Vulnerability
CVE-2021-33739 – Microsoft DWM Core Library Elevation of Privilege Vulnerability
CVE-2021-31956 – Windows NTFS Elevation of Privilege Vulnerability
CVE-2021-31955 – Windows Kernel Information Disclosure Vulnerability
CVE-2021-31201 – Microsoft Enhanced Cryptographic Provider Elevation of Privilege Vulnerability
CVE-2021-31199 – Microsoft Enhanced Cryptographic Provider Elevation of Privilege Vulnerability
Qualys QIDs Providing Coverage
| QID | Title | Severity | CVE ID |
|---|---|---|---|
| 91768 | Microsoft .NET Core Security Update June 2021 | Medium | CVE-2021-31957 |
| 91769 | Microsoft Visual Studio Security Update for June 2021 | Medium | CVE-2021-31957 |
| 375614 | Visual Studio Code Kubernetes Tools Extension Elevation of Privilege Vulnerability | Medium | CVE-2021-31938 |
| 110383 | Microsoft SharePoint Enterprise Server Multiple Vulnerabilities June 2021 | High | CVE-2021-31966,CVE-2021-31965,CVE-2021-31964,CVE-2021-31963,CVE-2021-31950,CVE-2021-31948,CVE-2021-26420 |
| 110384 | Microsoft Office and Microsoft Office Services and Web Apps Security Update June 2021 | High | CVE-2021-31939,CVE-2021-31941,CVE-2021-31940,CVE-2021-31949 |
| 110385 | Mcrosoft Outlook Remote Code Execution Vulnerability Security Update June 2021 | High | CVE-2021-31949,CVE-2021-31941 |
| 91771 | Microsoft Defender Multiple Vulnerabilities - June 2021 | Critical | CVE-2021-31978,CVE-2021-31985 |
| 91772 | Microsoft Windows Security Update for June 2021 | Critical | CVE-2021-1675,CVE-2021-26414,CVE-2021-31199,CVE-2021-31201,CVE-2021-31951,CVE-2021-31952,CVE-2021-31953,CVE-2021-31954,CVE-2021-31955,CVE-2021-31956,CVE-2021-31958,CVE-2021-31959,CVE-2021-31960,CVE-2021-31962,CVE-2021-31968,CVE-2021-31969,CVE-2021-31970,CVE-2021-31971,CVE-2021-31972,CVE-2021-31973,CVE-2021-31974,CVE-2021-31975,CVE-2021-31976,CVE-2021-31977,CVE-2021-33742 |
| 91773 | Microsoft 3D Viewer Multiple Vulnerabilities - June 2021 | High | CVE-2021-31944,CVE-2021-31943,CVE-2021-31942 |
| 91774 | Microsoft Paint 3D Remote Code Execution Vulnerability | High | CVE-2021-31983,CVE-2021-31946,CVE-2021-31945 |
| 91775 | Microsoft Windows VP9 Video Extension Remote Code Execution Vulnerability | Medium | CVE-2021-31967 |
| 91777 | Microsoft Windows DWM Core Library Elevation of Privilege Vulnerability - June 2021 | High | CVE-2021-33739 |
Adobe Patch Tuesday – June 2021
Adobe addressed 41 CVEs this Patch Tuesday, and 21 of them are rated as critical severity impacting Acrobat and Reader, Adobe Photoshop, Creative Cloud Desktop Application, RoboHelp Server, Adobe After Effects, and Adobe Animate products.
| Adobe Security Bulletin | QID | Severity | CVE ID |
|---|---|---|---|
| Adobe Animate Multiple Security Vulnerabilities (APSB21-50) | 91770 | Medium | CVE-2021-28630,CVE-2021-28619,CVE-2021-28617,CVE-2021-28618,CVE-2021-28621,CVE-2021-28620,CVE-2021-28629,CVE-2021-28622 |
| Adobe Security Update for Adobe Acrobat and Reader( APSB21-37) | 375611 | High | CVE-2021-28551,CVE-2021-28554,CVE-2021-28552,CVE-2021-28631,CVE-2021-28632 |
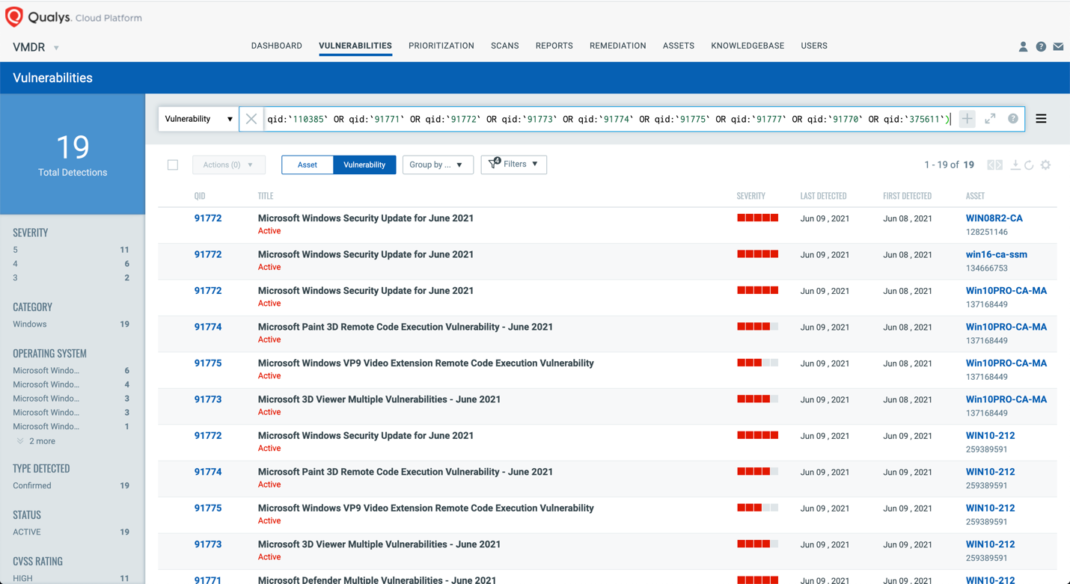
Discover Patch Tuesday Vulnerabilities in VMDR
Qualys VMDR automatically detects new Patch Tuesday vulnerabilities using continuous updates to its Knowledge Base (KB).
You can see all your impacted hosts by these vulnerabilities using the following QQL query:
vulnerabilities.vulnerability:(qid:91768 OR qid:91769 OR qid:91770 OR qid:91771 OR qid:91772 OR qid:91773 OR qid:91774 OR qid:91775 OR qid:91777 OR qid:110383 OR qid:110384 OR qid:110385 OR qid:375611 OR qid:375614)
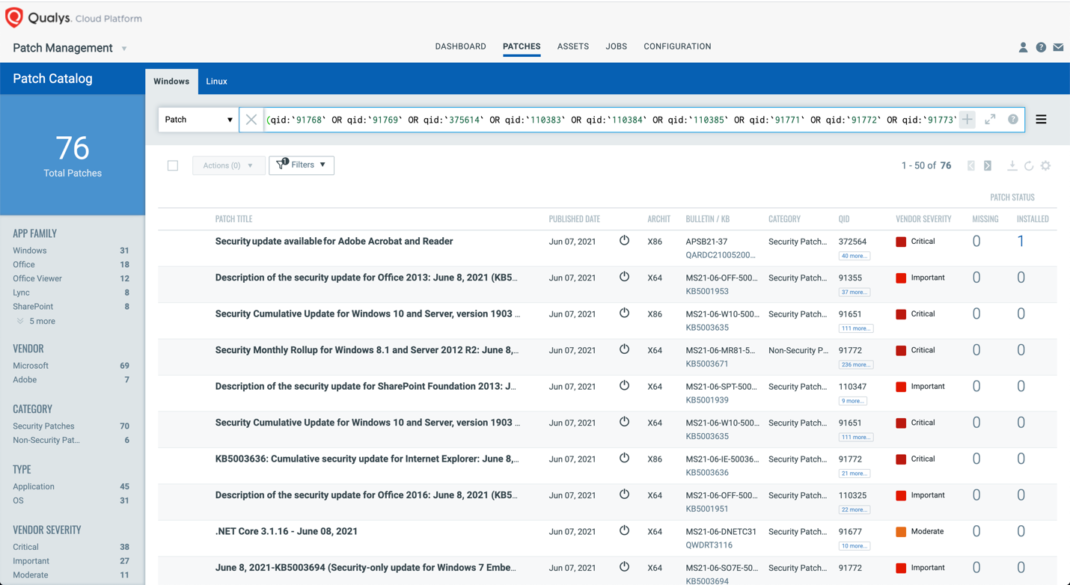
Respond by Patching
VMDR rapidly remediates Windows hosts by deploying the most relevant and applicable per-technology version patches. You can simply select respective QIDs in the Patch Catalog and filter on the “Missing” patches to identify and deploy the applicable, available patches in one go.
The following QQL will return the missing patches pertaining to this Patch Tuesday.
(qid:91768 OR qid:91769 OR qid:91770 OR qid:91771 OR qid:91772 OR qid:91773 OR qid:91774 OR qid:91775 OR qid:91777 OR qid:110383 OR qid:110384 OR qid:110385 OR qid:375611 OR qid:375614)
Patch Tuesday Dashboard
The current updated Patch Tuesday dashboards are available in Dashboard Toolbox: 2021 Patch Tuesday Dashboard.
Webinar Series: This Month in Patches
To help customers leverage the seamless integration between Qualys VMDR and Patch Management and reduce the median time to remediate critical vulnerabilities, the Qualys Research team is hosting a monthly webinar series This Month in Patches.
We discuss some of the key vulnerabilities disclosed in the past month and how to patch them:
- VMware vCenter Server Multiple Vulnerabilities
- Ubuntu XStream Vulnerabilities
- Microsoft Patch Tuesday, June 2021
Join us live or watch on demand!
About Patch Tuesday
Patch Tuesday QIDs are published at Security Alerts, typically late in the evening of Patch Tuesday, followed shortly after by PT dashboards.