OSINT. What can you find from a domain or company name
6.9 Medium
AI Score
Confidence
Low

We carry out lots of attack surface assessments, parts of which involve investigating information that has been unintentionally disclosed.
To help OPSEC people I thought it might be useful to go over some of the key things that can be found using domain and company names.
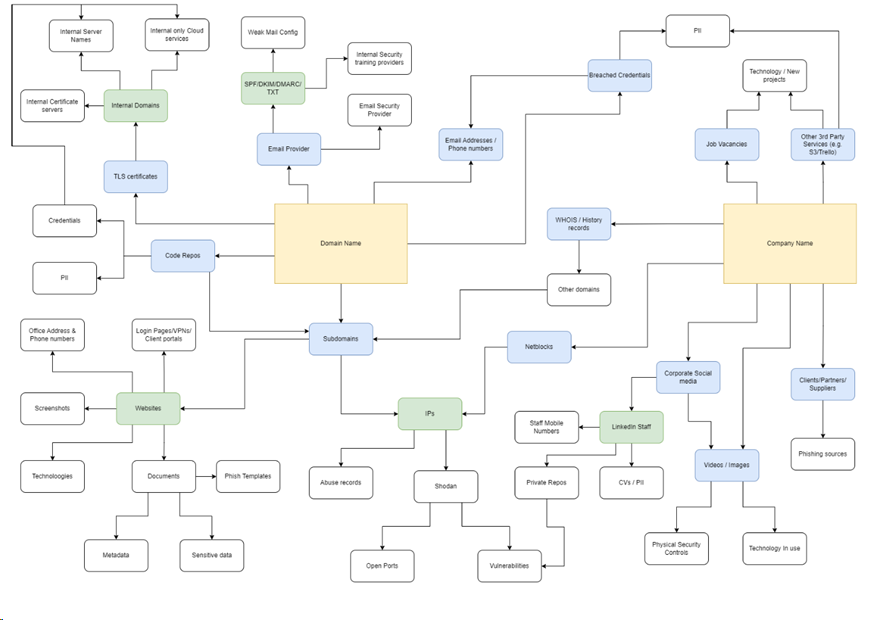
Domain name
So let’s dive in and look at the domain name. From this we can find:
- Subdomains
- IP addresses
- Web servers
- TLS certificates
- Email provider information
- Email addresses
- Staff contact information
- Breached credentials
- Code repos
- Documents
- Internal server or domain names
- Other domains
- …plus much more
This will provide you with further layers of information to examine and scrutinise.
Company name
From the company name there is plenty to find:
- Netblocks (which can be examined for much more)
- WHOIS records (which can be used in horizonal domain correlation)
- Corporate social media profiles
- Staff
- Videos/images
- Clients and suppliers or partners
- SaaS services
- Vacant jobs
- …plus much more
What can each element be used for?
If we look at the impact of these disclosures there are some key attacks that can be carried out, although this is not exhaustive, it does demonstrate how innocuous disclosures can have a bigger impact when combined.
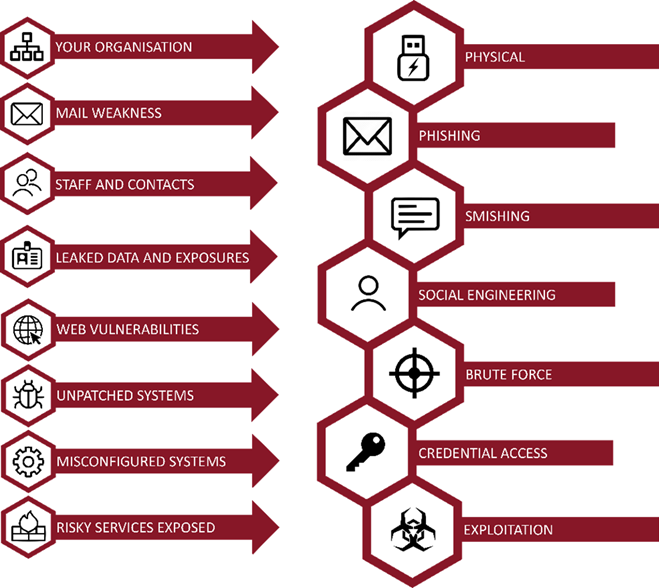
Whilst this overly simplifies the situation, we can expand on this with other examples:
- TLS certificates often disclose other domains, this can lead to more subdomains which may not be as well managed.
- Email configuration is routinely overlooked and can lead directly to spoofing attacks.
- Images posted on LinkedIn or YouTube by the organisation often include ID badges, we can create fake versions to add credent to physical attacks.
- Exposed code on code repos can lead directly to accessing corporate services.
- Supplier information disclosed in job adverts or testimonials can lead to suppliers being spoofed in email communications or they themselves being hacked to be used in supply chain attacks.
- …and much more!
Visualised
This diagram shows what can be obtained from just two starting points: The company and domain name.
Click image to enlarge. Opens in new tab.
This is just a start, but hopefully should get you on the right track to understanding what information can be found, and as importantly, where you can apply technical or procedural control to either limit the exposure or be aware of the impact of the exposure.
Recommendations
It is crucial to understand your entire attack surface and importantly recognise that this extends way beyond your technical attack surface. Tools alone won’t be able to provide you all of the information.
Some key suggested steps to take
- Use Google dorks with the parameter site:<yourdomain> to see what you are currently exposing, its advisable to use other operators, such as any protective markings e.g.site:<yourdomain> “classification: sensitive”. This may reveal information being published which may not be suitable for public consumption.
- Identify exposed technical assets from DNS, TLS certificates, IP netblocks and much more. This can identify assets not being managed by IT.
- Search for partners or suppliers who are exposing relationships with your organisation. This is a supply chain attack risk.
- Look at what your organisation is publishing to corporate social media, ensure to train marketing staff to be careful what publish to avoid things like ID badges being leaked.
Naturally there is much, much more that can be found. Its important to recognise that your threat actors only need start with one or two pieces of information and can deduce a huge amount of information. Isn’t it worth trying to emulate the reconnaissance phase of the Mitre ATT&CK matrix to see what your threat actors see?
The post OSINT. What can you find from a domain or company name first appeared on Pen Test Partners.
6.9 Medium
AI Score
Confidence
Low