
EFB ePIL. Pinching passenger PII from pilots

TL;DR
- The Passenger Information List (PIL) is often now available on EFBs and crew devices. It stores information such as passenger names, seat numbers, and customer services information. Digital versions of the PIL enable crew to offer more bespoke customer service
- Information on a PIL is different to most other EFB applications as it contains sensitive information relating to passengers. The devices used to access the PIL often connect to unsecure networks. There are heavy GDPR fines for failure to secure this data.
Targets and potential data access / tampering consequences
Target: Passenger Information List / Manifest
Background:
The Passenger Information List (PIL) or Passenger Manifest is a document which is provided to the crew prior to each flight. In its most basic form it will include passenger names and their seat numbers.
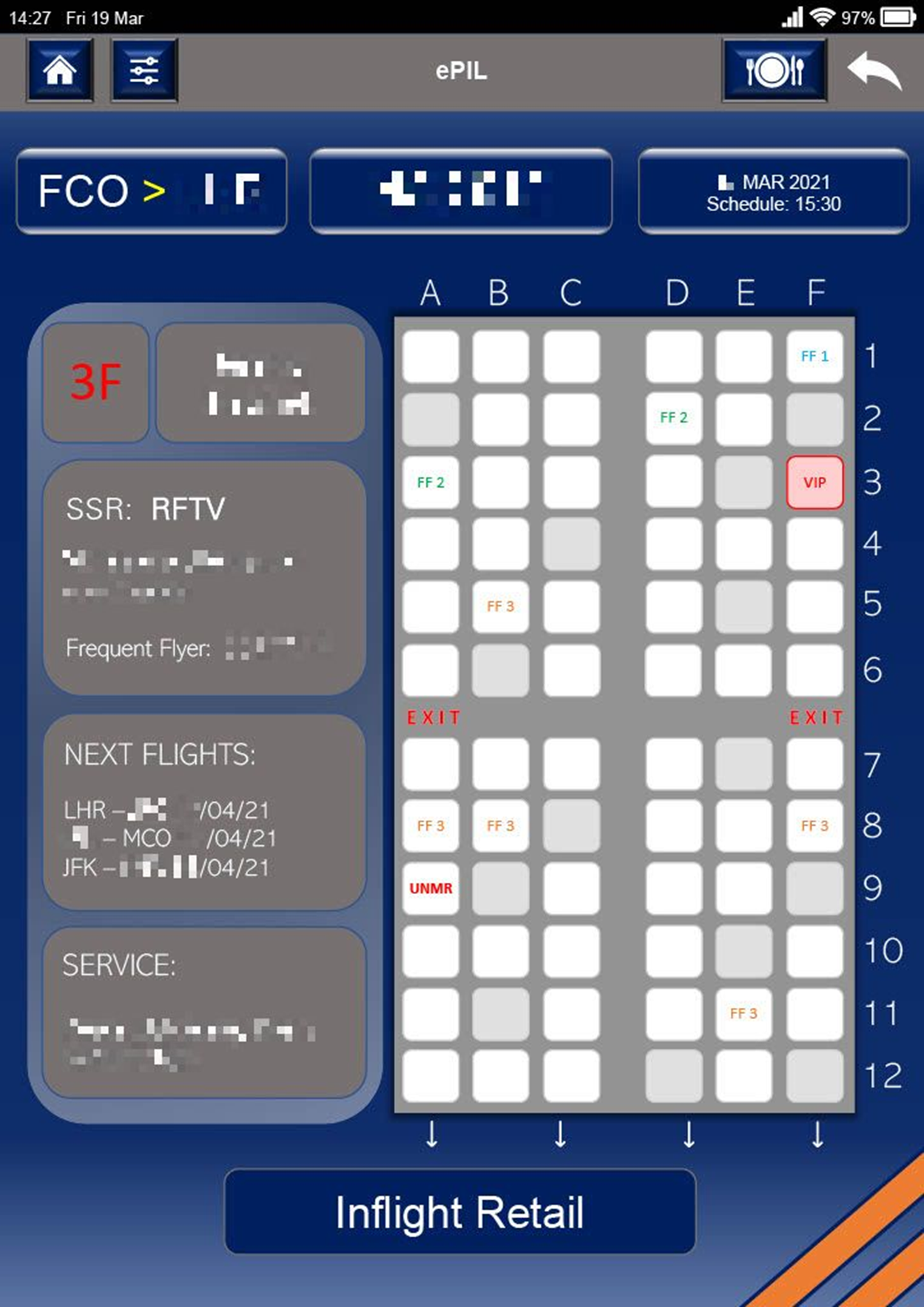
Various applications have now been developed which digitalise the PIL, hence it is often called the Electronic Passenger Information List (ePIL). These applications remove the need for a printed PIL, can be updated frequently and provide several functions to the crew which were unavailable using a paper PIL. Whilst an ePIL is more frequently used by the cabin crew than the pilots, it is common for them to be installed on EFB’s for pilots to use.
Where the ePIL is unique compared to other EFB applications is that it contains highly sensitive passenger information whereas others don’t. Failing to properly secure this information makes airlines susceptible to GDPR fines and it also makes passengers vulnerable to fraud and extortion. Fines for GDPR breaches are becoming more common and larger in size. In July 2019, Marriot International were informed of the ICO intention to impose a fine of £99m for failing to keep customers’ personal data secure. When it comes to fraud, it was estimated that in 2016 alone up to $16 billion of losses were caused by fraud and identity theft.
Common ePIL functions on an EFB include:
- Viewing pre-orders
- Processing purchases from the on-board shop (BuyOnBoard/BOB)
- Viewing real-time passenger information and their preferences
- Enable crew to advise passengers that the airline has changed their booking to ensure they make their connecting flight
- View details of previous purchases on-board
- View previous travel history
- Instructions for cabin crew to deliver personal messages to certain passengers (particularly VIPs), for example birthday wishes, anniversary congratulations, or previous complaint information
Common data that is included in the ePIL:
- Passenger name
- Seat number
- VIP Details
- Executive/Frequent Flyer Program Number
- Special service requests/requirements
- Previous on-board purchase information
- Connecting flight details
Connectivity:
As most airlines are aware of the risks around the disclosure of personal information, passenger data is often not available to crew until 24-48 hours prior to a flight. Senior crew need to be able to access the data prior to reporting for duty – it enables them to plan services and crew positions. The data is often downloaded by the crew member at their home address using their home Wi-fi, or using hotel Wi-fi on a layover prior to reporting. It is common for crew to then update the ePIL several times prior to departure, often using airport Wi-fi hotspots or 3G/4G.
As an ePIL application will be sending and receiving sensitive data it isn’t just the device in question that needs to be secure, networks the device connects to also need to be considered. This is no easy task as the devices in question are highly mobile and potentially connect to hundreds of different Wi-fi networks yearly. In less developed countries where cybersecurity is still a relatively new concept, it isn’t all that uncommon to find consumer Wi-fi routers in smaller hotels, sometimes with a default PSK and router admin credential. Additionally, open Wi-fi networks without client isolation are not rate.
Threat Areas:
ePIL applications can be located on both an installed as well as a portable EFB. It is almost certain that it will also be installed on cabin crew devices, these can be either tablets or company issued mobile phones. Therefore, we need to consider both the remote and local access threats - cybersecurity awareness training for crew applies in both cases:
ePIL remote threat:
Network-based. Unencrypted data on hotel/airport Wi-fi
Mitigation: Ensure only secure cryptographic protocols are used, prohibit/restrict crew from connecting to public Wi-fi networks, enforce unique passwords
Web-based: links to malicious websites sent via email or messaging applications
Mitigation: Restrict use of EFBs or crew devices to business use only and prohibit personal messaging applications that are unnecessary
**Application-based:**Malware or malicious applications installed on device
Mitigation: Code reviews (e.g. ensure secure cryptographic protocols are used) and penetration testing if application is internally developed. Mobile Device Management configured to push secure policies, prohibit installation of unnecessary applications and ensure sharing permissions are restricted
ePIL local threat:
Access: Theft of or access to device, ports (USB etc.)
Mitigation: Two factor authentication and use of strong complex passwords, screen lock with short timer, disabling of any ports that are not required, reduce exposure by restricting devices to business use only (prevents them being taken on holiday etc.), remote wiping, where possible store data to the cloud rather than locally
Australian PM Tony Abbott Boarding Card Story:
As hackers often try to obtain information which helps them to enumerate (gather details on) their target, just one piece of information from the ePIL could provide a hacker with enough detail to access other systems or other sensitive information. A famous example of this was when former Australian Prime Minister Tony Abbott posted a photo of his boarding pass on Instagram. Ethical hacker Alex Hope used the information on the barcode of the boarding card to access the booking management system on the Qantas website – for Tony Abbotts account…!
Having accessed the Manage Booking System, Hope was able to obtain some fairly innocuous information including Abbott’s frequent flyer number. Having done a little more digging (purely with Inspect Element…!), Hope could now see Abbott’s passport number, his registered phone number, and his Special Service Request (SSR – discussed next).
Hope disclosed the information to Abbott who thanked him. Read his original blog post at <https://mango.pdf.zone/finding-former-australian-prime-minister-tony-abbotts-passport-number-on-instagram>.
Special Service Request (SSR):
SSR’s are codes sent to communicate traveller preferences, special services needed by a traveller, or of a procedural requirement necessary of the carrier. It is common for SSR’s to be displayed on the ePIL. On most flights these will relate to passenger disabilities or customer service concerns, for example BLND (passenger is blind or has reduced vision) or PETC (passenger is travelling with a pet in the cabin).
Some perceivably more sensitive SSR’s:
- WEAP – Weapon
- DEPA – Accompanied deportee
- UMNR – Unaccompanied minor
- RFTV – Reason for travel
Clearly, this information is highly sensitive. The location of any armed personnel onboard a flight or the VIP they are protecting is extremely delicate as is the location of any minors travelling alone. We won’t go into detail about when these details would or would not be present on an ePIL, for obvious reasons. However, it does raise the question of whether it really is appropriate to be accessing information of this nature on an insecure hotel Wi-fi, public Wi-fi hotspots, or from home routers.
Electronic Passenger Information List
Motives and consequences:
There are a wide variety of reasons that could motivate a malicious hacker to access ePIL data as well as a wide variety of potential consequences – too many to name in this blog. The following are just some examples - GDPR fines would be applicable in most scenarios.
- Passenger ransom/threat/theft. Previous and future journey details are available on some ePIL software. VIP travel patterns could be obtained which would enable a malicious hacker to anticipate when/where the next flight will occur. Obtaining data which discloses future travel bookings would be useful to a terrorist organisation (targeting VIPs) and thieves (targeting properties of VIPs – establishing when the properties will be empty).
A tale from when an unnamed airline first introduced the ePIL:
VIP Passenger Mr Jacobs takes his wife for a weekend away to Paris. On boarding the aircraft they are shown to their seats by a stewardess who then says: “Mr Jacobs, how was your visit to Paris last weekend?”.
Mr Jacobs wife replies “what trip to Paris last weekend?”…
- Competitor access to data. Competitors could target customers/advertising based on travel history and personal information.
- Disclosure of sensitive passenger information. This information could be misused in a variety of ways including:
- Extortion/blackmail of a victim
- Compromising bank or other accounts
- Creating counterfeit credit cards
- Creating forged documents
- Applications for loans/credit cards under the victim’s name
- Resale of information to marketing firms
Malicious hackers with access could obtain confidential information which could be used in a variety of ways including building a profile of a passenger which could subsequently be sold on or used in identity theft / for fraudulent purposes.
Summary:
The improvements to service made available by use of an ePIL are significant. In order to ensure passenger data is secure, consideration should be given to what networks are used when downloading passenger information. Device security needs to be effective with strong passwords and two factor authentication where possible. Many threats are potentially removed by prohibiting the use of public Wi-fi (including hotels), and also by restricting applications installed on devices to only those which are required for work purposes.
Target: Airports charts
Potential consequence: Hull loss
Introduction:
Pilots use charts to obtain various information. All charts discussed below contain both a graphical overview of the relevant area as well as text containing important information. Airport charts can be broken up into 4 areas:
- Ground charts including airport runways/taxiways and aprons or parking areas
- Standard Instrument Departure (SID) charts
- Standard Terminal Arrival (STAR) charts
- Approach charts
Ground charts:
These are used by pilots to help them plan expected taxi routings both from the parking stand to the departure runway as well as after landing from vacating the runway to arrival at the parking stand. During taxi, pilots consult ground charts frequently to help them navigate around airports – many of them unfamiliar and large in scale. Whilst airports have taxiway signs to help pilots, in poor visibility these can be hard to see. The deadliest non-terrorist accident in aviation history occurred in Tenerife when a KLM 747 taking-off collided with a Pan Am 747 that was taxiing on the runway.
When directing aircraft on the ground controllers generally look out of the window from the control tower. Ground radar, also known as surface movement radar, where installed is used when visibility is poor - many airports do not have ground radar. Controller workload can be high (as can pilot workload) and equipment unserviceability’s do occur. A well-known example of this was the Milan Linate Airport accident that occurred in October 2001 when a Scandinavian Airlines MD-87 taking-off collided with a business jet that had inadvertently taxied onto the runway during poor weather.
Full report: <https://reports.aviation-safety.net/2001/20011008-0_MD87_SE-DMA_C25A_D-IEVX.pdf>
Video (dramatization): <https://www.youtube.com/watch?v=IZ8zhJ_7sHI>
Standard Instrument Departure (SID) charts:
SID charts are used to provide pilots with information to enable them to comply with standard departure routings from the take-off phase to the en-route phase. When an aircraft takes-off on a commercial flight from a busy airfield, the pilots can’t simply point the aircraft at the destination. Instead, they follow a pre-assigned routing that Air Traffic Control (ATC) have assigned them for departure. This is known as the SID.
Standard Terminal Arrival (STAR) charts:
STAR charts are similar to SID charts except they contain the information required to follow arrival routings from the en-route phase to the final approach phase. Roughly speaking, this is from the cruising altitude to anywhere between 3000 and 5000 feet.
Approach charts:
There are a whole variety of different types of approaches that are available to commercial aircraft. In order to fly a specific approach, certain information will be required. More common approach methods include:
Visual approach: charts used to identify pre-brief threats e.g. location of terrain. No navigational aids required, just look out of the window to find the airport.
ILS approach: favoured at most large commercial airports, used frequently. Ground aids including a localiser and a glidepath antenna are required. These approaches are used in poor visibility, known as CAT II or CAT III approaches.
VOR approach: non-precision approach used more frequently in less developed countries but many still exist in Europe and the USA. Gradually being replaced by RNP approaches (GPS based)
NDB approach: Similar to VOR approaches (ground based beacon) but even less common as these days they are being replaced. Can be very inaccurate particularly when navigating in the vicinity of thunderstorms or around mountainous terrain.
RNP/GPS based approach: Various forms exist but in principle they’re similar - navigation is based on GPS signals. Can be combined with VOR/NDB approaches (known as “overlaying”) to fly a VOR/NDB approach using GPS equipment instead of navigation beacons.
- Ground radar explanation
- Ground collision at Milan Linate
- Runway incursion
- Departure from incorrect runway
- Recording of aircraft on youtube near miss
- Live taxiway routing is new on ND, some EFBs do it too. Spoofed GPS…!
- Change missed approach into something incorrect
- Change frequencies
- Change radials
- Change ILS courses
- Change DME
- Change minimums
- Low vis issue of ground charts being wrong
- Change taxiway routing in low vis (automatic taxiway instructions and depictions)
EMER TURN: add to “other” applications? It’s often a function in the TO Perf tool, but could be a separate application. Modify emergency turn by 10 degrees to direct at a hill…! EGPWS won’t help as pull up manouevre means you fly straight and level, so if the terrain is in front of you and big, you won’t necessarily outclimb it.
CHARTING:
Prevent update of LIDO charts – creates an out of date situation and possibly charts will not include critical updates.
Modification of TOR/LDA? Taxiway width? Actually move taxiway positions on the chart?
Removal of no fly zones? Malaysian crash shot down?
VOR approach Korean that flew in to hill, mod of VOR radial.
Mod of danger areas on charts, 747 that the Russians shot down, more recently Malaysian 777.
Frequencies, radials, distances, depictions, layout, procedures, critical data (TORA/LDA).
Pilots often brief interactively – could be done on one EFB. Alternatively, EFB can be inop for a period of time.
Automatic taxi routing (follow LVO taxi route “A”, change the path to make the aircraft go a different way, either through interactive mode or on the paper chart instructions.
<https://www.youtube.com/watch?v=TmCFRnG56zA>
Above link, 1:00 in. Modify positions of lights etc, makes it difficult for pilots to know where they are. Add a taxiway prior to a runway, would make pilots think the upcoming runway is a taxiway (hopefully see the signage).
The post EFB ePIL. Pinching passenger PII from pilots first appeared on Pen Test Partners.