
FBI issues advisory over Play ransomware
7.7 High
AI Score
Confidence
Low
The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and the Australian Signals Directorate’s Australian Cyber Security Centre (ACSC) have released a joint Cybersecurity Advisory (CSA) about Play ransomware.
According to the FBI, Play made around 300 victims between June 2022 and October 2023 among a wide range of businesses and critical infrastructure in North America, South America, and Europe.
The joint advisory provides a list of legitimate tools that the Play ransomware group uses for their operations, but more importantly, it includes a list of frequently used attack vectors and vulnerabilities. These include the abuse of valid accounts and exploitation of public-facing applications, specifically through known vulnerabilities like ProxyNotShell.
Once inside a network, Play uses specialized tools to try and disable anti-virus software and remove log files. Then the hunt for valuable data and the preparation for the encryption process begins. Typically, that behavior that requires a dedicated security team or an external managed detection and response (MDR) service to discover.
In our most recent monthly ransomware review you'll see Play climbing from 6th place to 3rd in the list of groups with the highest number of known attacks.
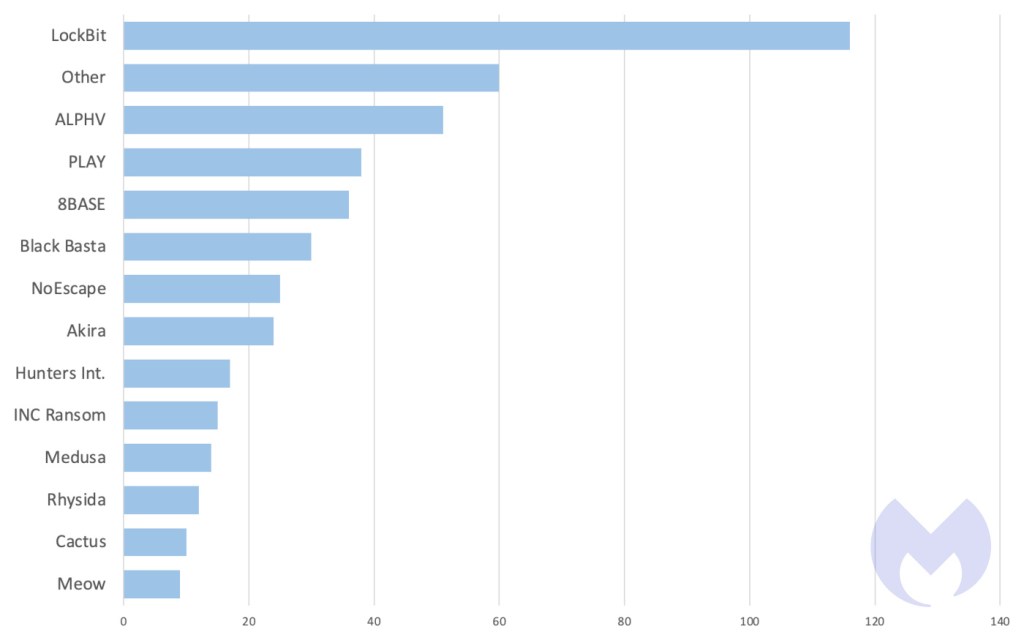 Known ransomware attacks by gang, November 2023
Known ransomware attacks by gang, November 2023
The Play ransomware group has been making a name for itself since August 2022 and is a typical double extortion group. This means they steal data as well as encrypting systems and then threaten to publish the stolen data on their Dark Web leak site.
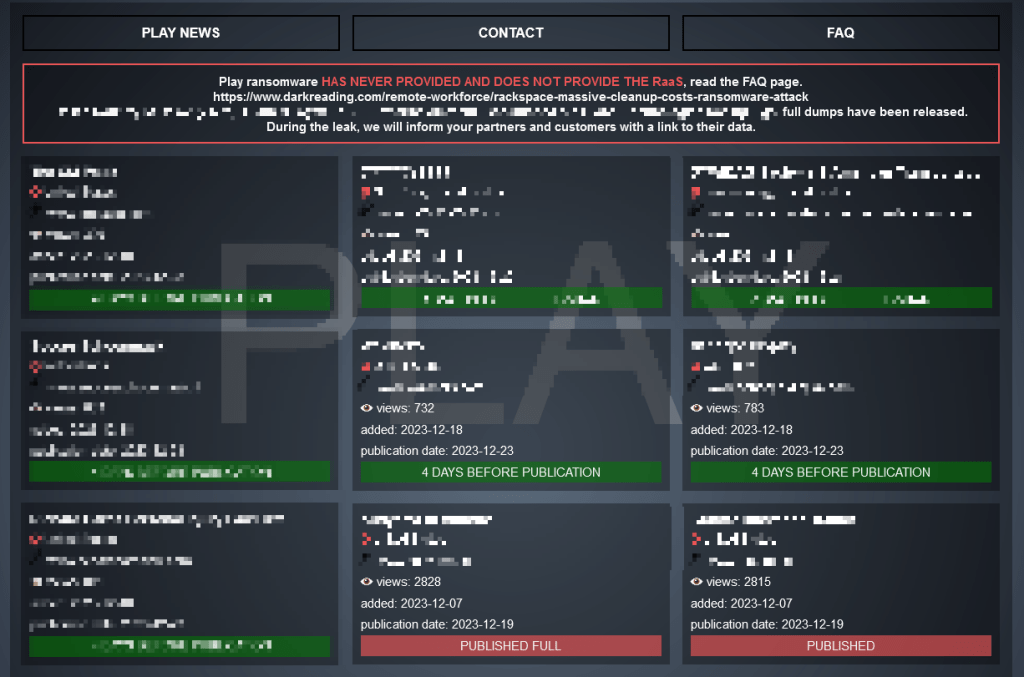
Screenshot of the PLAY leak site
The joint CSA emphasizes the importance of having an actionable recovery plan, using multi-factor authentication (MFA), and keeping all operating systems, software, and firmware up to date.
The FBI lets readers know it is seeking any information that can be shared, to include boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with Play ransomware actors, Bitcoin wallet information, decryptor files, and/or a benign sample of an encrypted file.
How to avoid ransomware
- Block common forms of entry. Create a plan for patching vulnerabilities in internet-facing systems quickly; and disable or harden remote access like RDP and VPNs.
- Prevent intrusions. Stop threats early before they can even infiltrate or infect your endpoints. Use endpoint security software that can prevent exploits and malware used to deliver ransomware.
- Detect intrusions. Make it harder for intruders to operate inside your organization by segmenting networks and assigning access rights prudently. Use EDR or MDR to detect unusual activity before an attack occurs.
- Stop malicious encryption. Deploy Endpoint Detection and Response software like ThreatDown EDR that uses multiple different detection techniques to identify ransomware, and ransomware rollback to restore damaged system files.
- Create offsite, offline backups. Keep backups offsite and offline, beyond the reach of attackers. Test them regularly to make sure you can restore essential business functions swiftly.
- Don’t get attacked twice. Once you’ve isolated the outbreak and stopped the first attack, you must remove every trace of the attackers, their malware, their tools, and their methods of entry, to avoid being attacked again.
Our business solutions remove all remnants of ransomware and prevent you from getting reinfected. Want to learn more about how we can help protect your business? Get a free trial below.
7.7 High
AI Score
Confidence
Low