
Cryptic Rumblings Ahead of First 2020 Patch Tuesday
8.1 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
NONE
CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:N
5.8 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
NONE
AV:N/AC:M/Au:N/C:P/I:P/A:N
Sources tell KrebsOnSecurity that Microsoft Corp. is slated to release a software update on Tuesday to fix an extraordinarily serious security vulnerability in a core cryptographic component present in all versions ofWindows. Those sources say Microsoft has quietly shipped a patch for the bug to branches of the U.S. military and to other high-value customers/targets that manage key Internet infrastructure, and that those organizations have been asked to sign agreements preventing them from disclosing details of the flaw prior to Jan. 14, the first Patch Tuesday of 2020.
According to sources, the vulnerability in question resides in a Windows component known as crypt32.dll, a Windows module that Microsoft says handles “certificate and cryptographic messaging functions in the CryptoAPI.” The Microsoft CryptoAPI provides services that enable developers to secure Windows-based applications using cryptography, and includes functionality for encrypting and decrypting data using digital certificates.
A critical vulnerability in this Windows component could have wide-ranging security implications for a number of important Windows functions, including authentication on Windows desktops and servers, the protection of sensitive data handled by Microsoft’s Internet Explorer/Edge browsers, as well as a number of third-party applications and tools.
Equally concerning, a flaw in crypt32.dll might also be abused to spoof the digital signature tied to a specific piece of software. Such a weakness could be exploited by attackers to make malware appear to be a benign program that was produced and signed by a legitimate software company.
This component was introduced into Windows more than 20 years ago – back in Windows NT 4.0. Consequently, all versions of Windows are likely affected (including Windows XP, which is no longer being supported with patches from Microsoft).
Microsoft has not yet responded to requests for comment. However, KrebsOnSecurity has heard rumblings from several sources over the past 48 hours that this Patch Tuesday (tomorrow) will include a doozy of an update that will need to be addressed immediately by all organizations running Windows.
Update 7:49 p.m. ET: Microsoft responded, saying that it does not discuss the details of reported vulnerabilities before an update is available. The company also said it does "not release production-ready updates ahead of regular Update Tuesday schedule. “Through our Security Update Validation Program (SUVP), we release advance versions of our updates for the purpose of validation and interoperability testing in lab environments,” Microsoft said in a written statement. “Participants in this program are contractually disallowed from applying the fix to any system outside of this purpose and may not apply it to production infrastructure.”
Original story:
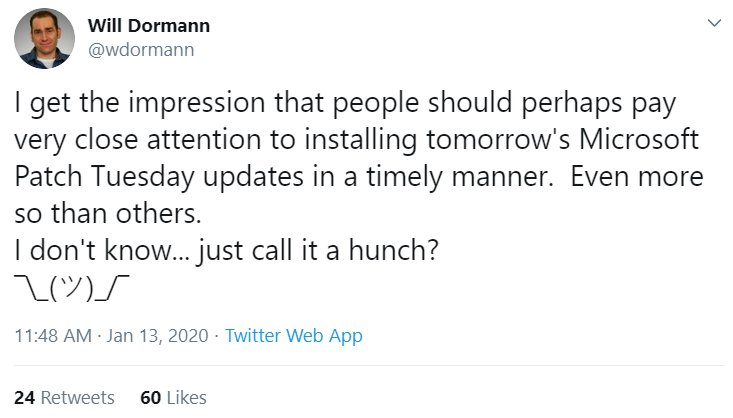
Will Dormann, a security researcher who authors many of the vulnerability reports for the CERT Coordination Center (CERT-CC), tweeted today that “people should perhaps pay very close attention to installing tomorrow’s Microsoft Patch Tuesday updates in a timely manner. Even more so than others. I don’t know…just call it a hunch?” Dormann declined to elaborate on that teaser.
It could be that the timing and topic here (cryptography) is nothing more than a coincidence, but KrebsOnSecurity today received a heads up from the U.S. National Security Agency (NSA) stating that NSA’s Director of CybersecurityAnne Neuberger is slated to host a call on Jan. 14 with the news media that “will provide advanced notification of a current NSA cybersecurity issue.”
The NSA’s public affairs folks did not respond to requests for more information on the nature or purpose of the discussion. The invitation from the agency said only that the call “reflects NSA’s efforts to enhance dialogue with industry partners regarding its work in the cybersecurity domain.”
Stay tuned for tomorrow’s coverage of Patch Tuesday and possibly more information on this particular vulnerability.
Update, Jan. 14, 9:20 a.m. ET: The NSA’s Neuberger said in a media call this morning that the agency did indeed report this vulnerability to Microsoft, and that this was the first time Microsoft will have credited NSA for reporting a security flaw. Neuberger said NSA researchers discovered the bug in their own research, and that Microsoft’s advisory later today will state that Microsoft has seen no active exploitation of it yet.
According to the NSA, the problem exists in Windows 10 and Windows Server 2016. Asked why the NSA was focusing on this particular vulnerability, Neuberger said the concern was that it “makes trust vulnerable.” The agency declined to say when it discovered the flaw, and that it would wait until Microsoft releases a patch for it later today before discussing further details of the vulnerability.
Update, 1:47 p.m. ET: Microsoft has released updates for this flaw (CVE-2020-0601). Their advisory is here. The NSA’s writeup (PDF) includes quite a bit more detail, as does the advisory from CERT.
8.1 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
NONE
CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:N
5.8 Medium
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
NONE
AV:N/AC:M/Au:N/C:P/I:P/A:N