
VMware patches SSRF and arbitrary file read vulnerabilities in vCenter Server
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P
THREAT LEVEL: Amber.
For a detailed advisory, download the pdf file here.
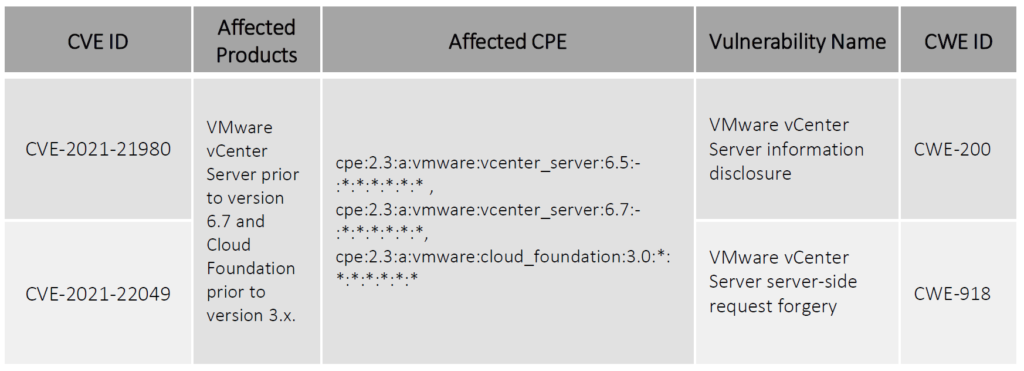
VMware has released fixes to address two security flaws in vCenter Server and Cloud Foundation tracked as CVE-2021-21980 and CVE-2021-22049. The vulnerability CVE-2021-21980 (arbitrary file read) is of major concern as an attacker with network access to port 443 on the vCenter Server can use this vulnerability to gain access to sensitive data.
Another vulnerability CVE-2021-22049 is an SSRF(Server-Side Request Forgery) vulnerability in the VSAN Web Client plug-in which a hostile actor with network access to port 443 on vCenter Server to exploit the flaw by visiting an internal service or a URL request outside of the server.
VMware has not released any official workarounds for the vulnerabilities, but organizations can patch their vulnerabilities for vCenter Server from the patch link provided down below. Patches for both the vulnerabilities are still pending for Cloud Foundation version 3x.
Vulnerability Details
Patch
<https://www.vmware.com/security/advisories/VMSA-2021-0027.html>
References
<https://thehackernews.com/2021/11/vmware-warns-of-newly-discovered.html>
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P