
VMware patches 2 Critical Vulnerabilities in Carbon Black App Control, VMWare Tools and VMWare Remote Console
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P
THREAT LEVEL: Amber.
For a detailed advisory, download the pdf file here.
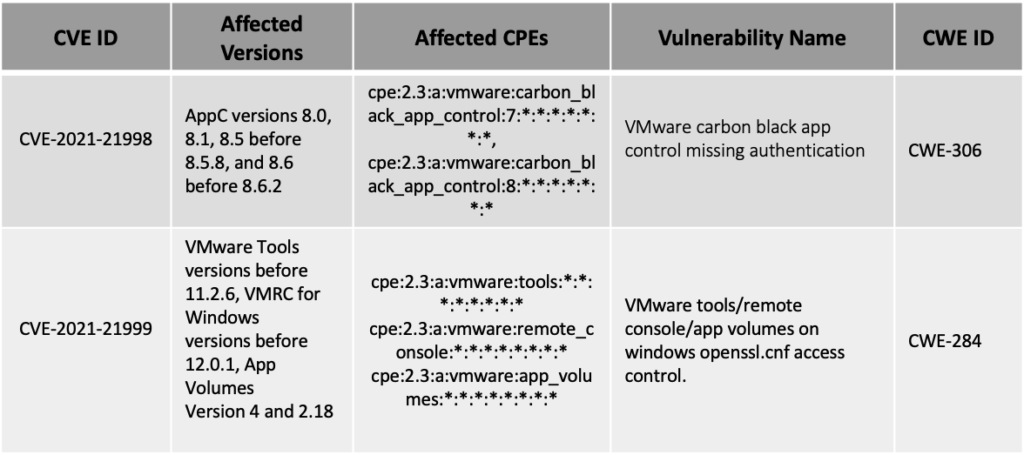
VMware has patched an authentication bypass vulnerability(CVE-2021-21998) in the carbon black app control management server. Apart from this vulnerability VMware also patched a privilege escalation vulnerability(CVE-2021-21999) which was affected the VMware Tools for Windows, VMware Remote Console for Windows.
Vulnerability Details
Patch Links
<https://www.vmware.com/security/advisories/VMSA-2021-0012.html>
<https://www.vmware.com/security/advisories/VMSA-2021-0013.html>
References
<https://us-cert.cisa.gov/ncas/current-activity/2021/06/23/vmware-releases-security-updates>
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
7.5 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
PARTIAL
Integrity Impact
PARTIAL
Availability Impact
PARTIAL
AV:N/AC:L/Au:N/C:P/I:P/A:P