
Microsoft Windows Remote Desktop Gateway allows for unauthenticated remote code execution
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
0.422 Medium
EPSS
Percentile
97.3%
Overview
Microsoft Windows Remote Desktop Gateway contains vulnerabilities that may allow a remote, unauthenticated attacker to execute arbitrary code with SYSTEM privileges on a vulnerable system.
Description
Microsoft Windows Remote Desktop Gateway (RD Gateway) is a Windows Server component that provides access to Remote Desktop services without requiring the client system to be present on the same network as the target system. Originally launched as Terminal Services Gateway (TS Gateway) with Windows Server 2008, RD Gateway is a recommended way to provide Remote Desktop connectivity to cloud-based systems. For example, guidance has been provided for using RD Gateway with AWS, and also with Azure. The use of RD Gateway is recommended to reduce the attack surface of Windows-based hosts.
Microsoft RD Gateway in Windows Server 2012 and later contain two vulnerabilities that can allow an unauthenticated remote attacker to execute arbitrary code with SYSTEM privileges. It is reported by Kryptos Logic that the flaws lie in handling of fragmentation. This vulnerability is exploitable by connecting to the RD Gateway service listening on UDP/3391.
Impact
By sending a specially-crafted request to a Remote Desktop Gateway server, an unauthenticated remote attacker to execute arbitrary code with SYSTEM privileges.
Solution
Apply an update
This issue is addressed in the Microsoft updates for CVE-2020-0609 and CVE-2020-0610. If this update cannot be installed, consider the following workarounds:
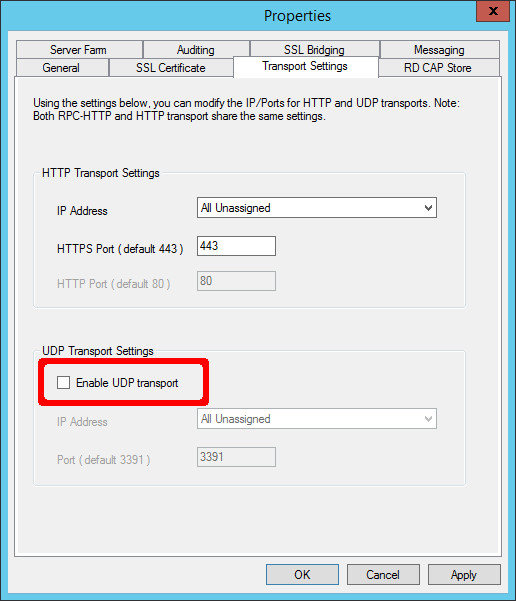
Disable Remote Desktop Gateway UDP transport
This vulnerability can be mitigated by disabling the UDP transport for Remote Desktop Gateway.
Block access to UDP/3391 at the network level
This vulnerability can be mitigated by blocking access to the Remote Desktop Gateway UDP port, which is UDP/3391 by default.
Vendor Information
491944
Filter by status: All Affected Not Affected Unknown
Filter by content: __ Additional information available
__ Sort by: Status Alphabetical
Expand all
Javascript is disabled. Click here to view vendors.
Microsoft Affected
Updated: January 14, 2020
Status
Affected
Vendor Statement
We have not received a statement from the vendor.
Vendor Information
We are not aware of further vendor information regarding this vulnerability.
Vendor References
- <https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0609>
- <https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0610>
CVSS Metrics
| Group | Score | Vector |
|---|---|---|
| Base | 10 | AV:N/AC:L/Au:N/C:C/I:C/A:C |
| Temporal | 7.8 | E:POC/RL:OF/RC:C |
| Environmental | 5.9 | CDP:ND/TD:M/CR:ND/IR:ND/AR:ND |
References
- <https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0609>
- <https://portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0610>
- <https://docs.microsoft.com/en-us/windows-server/remote/remote-desktop-services/rds-roles#remote-desktop-gateway>
- <https://aws.amazon.com/quickstart/architecture/rd-gateway/>
- <https://docs.microsoft.com/en-us/azure/active-directory/manage-apps/application-proxy-integrate-with-remote-desktop-services>
- <https://docs.microsoft.com/en-us/openspecs/windows_protocols/ms-tsgu/0007d661-a86d-4e8f-89f7-7f77f8824188>
- <https://techcommunity.microsoft.com/t5/ask-the-performance-team/ws2008-terminal-services-gateway-overview/ba-p/372882>
- <https://www.kryptoslogic.com/blog/2020/01/rdp-to-rce-when-fragmentation-goes-wrong/>
Acknowledgements
This document was written by Will Dormann.
Other Information
| CVE IDs: | CVE-2020-0609, CVE-2020-0610 |
|---|---|
| Date Public: | 2020-01-14 Date First Published: |
References
aws.amazon.com/quickstart/architecture/rd-gateway/
docs.microsoft.com/en-us/azure/active-directory/manage-apps/application-proxy-integrate-with-remote-desktop-services
docs.microsoft.com/en-us/openspecs/windows_protocols/ms-tsgu/0007d661-a86d-4e8f-89f7-7f77f8824188
docs.microsoft.com/en-us/windows-server/remote/remote-desktop-services/rds-roles#remote-desktop-gateway
portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0609
portal.msrc.microsoft.com/en-us/security-guidance/advisory/CVE-2020-0610
techcommunity.microsoft.com/t5/ask-the-performance-team/ws2008-terminal-services-gateway-overview/ba-p/372882
www.kryptoslogic.com/blog/2020/01/rdp-to-rce-when-fragmentation-goes-wrong/
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
0.422 Medium
EPSS
Percentile
97.3%