CVSS: Common Vulnerability Scoring System Overview
Fast-developing network technologies and their wide adoption by users around the globe have brought a high demand for well-developed security infrastructures. Thus, to measure the protection level of internet-connected systems, a special numeric method was developed by the Forum of Incident Response and Security Teams (FIRST). This framework is known as the Common Vulnerability Scoring System (CVSS).
In this article, we will define what the CVSS framework is, how it works, as well as the major score metrics that are used. Moreover, we will outline how the score metrics can be calculated and how most organizations adopt this efficient system.
- What is CVSS?
- Different versions of CVSS
- CVSS score metrics
- How is the scoring done?
- What is the difference between CVSS and CVE?
- How do organizations adopt and use the cvss?
- Limitations of CVSS
- How vulners can help with vulnerability database
- Conclusion
- FAQ
What is CVSS?
The CVSS system is one of the most popular metric frameworks that are used to define the vulnerabilities in software security. It is a computing method that helps users to analyze the threat level of a system’s weaknesses. Moreover, it supports various organizations to guarantee confidentiality integrity, and at the same time ensure companies’ data protection.
This framework was first introduced by the US National Infrastructure Advisory Council (NIAC) in 2005, and later the management passed to FIRST. The key role of CVSS scores is to assist information security (infosec) teams in order to define the security requirements of an enterprise. Moreover, CVSS is used as a milestone to perform effective vulnerability management and prioritize which threat issue should be solved first.
Essentially, the CVSS is an open standard scoring framework used by organizations as a system to define the impact of vulnerabilities and present it on a scale from 0 to 10. That way, infosec experts can define which is a more serious threat and try to find the proper solution to prevent a serious data breach. To form a clearer picture of what CVSS is, you can watch the brief video below.
Different versions of CVSS
The first version of CVSS was introduced in 2005, but since then, many updates took place, providing more accurate results when evaluating software vulnerabilities and reducing security risks. The different versions of CVSS are CVSS V1, V2, and the most recent, V3.
CVSS V1
This is the primary version of CVSS, which was introduced in 2005 by the NIAC. It was aiming to develop a rating standard in order to highlight the major vulnerabilities that were detected in a system and prioritize the threats that were the most crucial to be dealt with first.
CVSS V2
In 2007, after two years of using the CVSS framework, FIRST introduced a significant update. CVSS V2 was a great improvement since it solved major unreliability as well as various granularity. Moreover, it helped to present the true attributes of the IT vulnerabilities regardless of the vulnerability’s nature.
CVSS V3
However, the second version of CVSS also had its drawbacks and still could benefit from more improvements. Thus, in June 2015, another important update was released, implementing various revisions in CVSS and leading to the development of the framework’s third version. The key element that V3 introduced was a more effective scoring system, presenting the true image of a system’s vulnerabilities.
Moreover, CVSS V3 offers advanced characteristics such as defining the privileges that are needed to take advantage of a vulnerability. It also helps to highlight the various opportunities that an attacker may have if he succeeds in utilizing those drawbacks. In 2019, this version had its own upgrade, moving forward to version 3.1.
CVSS score metrics
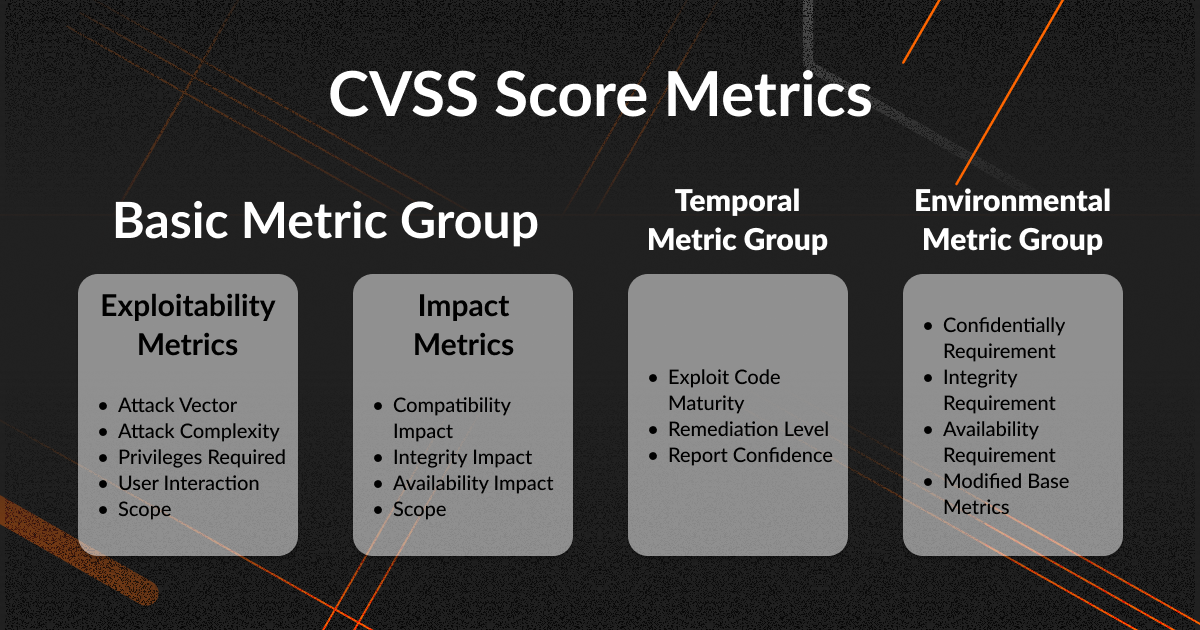
In order to implement the CVSS mechanism efficiently, the user should know how and from where the scores are derived. The score metrics depend on the characteristics, impact, and environmental persistence of the vulnerability. There are three major categories: base, temporal and environmental metrics. Moreover, a less technical CVSS score category refers to the qualitative ratings.
CVSS Base Metrics
This metrics category includes the inherent attributes of the vulnerability. These are elements that stay constant through time and are independent of any alterations to the user’s environment. Such characteristics can be the level that a vulnerability can expose the confidentiality, availability, or integrity of a system. The CVSS base metrics are divided into three sub-categories: exploitability, scope, and impact.
- Exploitability
This category refers to the metrics that are relevant to the means that can be used to reveal and take advantage of a vulnerability. This sub-category is further divided into subcomponents such as the attack vector and complexity, the user interaction, as well as the required privileges.
- Scope
This type of metric is correlated with the ability of the vulnerability to be propagated to different components. Thus, if propagation is possible then the scope scores are higher. An example of this metric can be a possible cyberattack on a backend database as a result of revealing and taking advantage of the vulnerabilities on a web server.
- Impact
This category is connected with the consequences that a cyberattack may have as a result of exploiting any type of vulnerability in the system. The impact metrics are divided into three subcategories: confidentiality, integrity, and availability.
CVSS Temporal Metrics
Another category of score metrics is temporal ones. These are types of metrics that change over time and define the level of the vulnerability’s exploitability, as well as the remediating controls. The temporal metrics are divided into three subcomponents: the exploit code maturity, the remediation level, and the report confidence.
CVSS Environmental Metrics
When running a vulnerability management program, the most serious characteristics that a user should take into consideration are the elements connected with his environment. These are known as environmental metrics and help an organization extract its Base CVSS, taking into consideration not only the Security Requirements, but also any alterations done to the Basic Metrics.
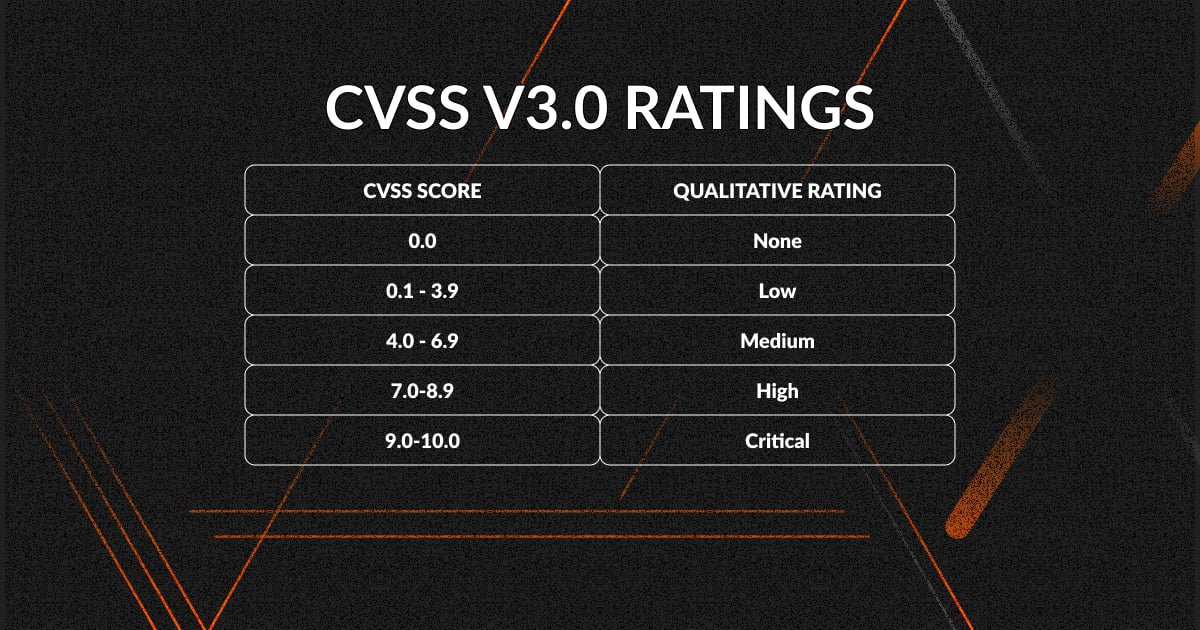
CVSS Qualitative Ratings
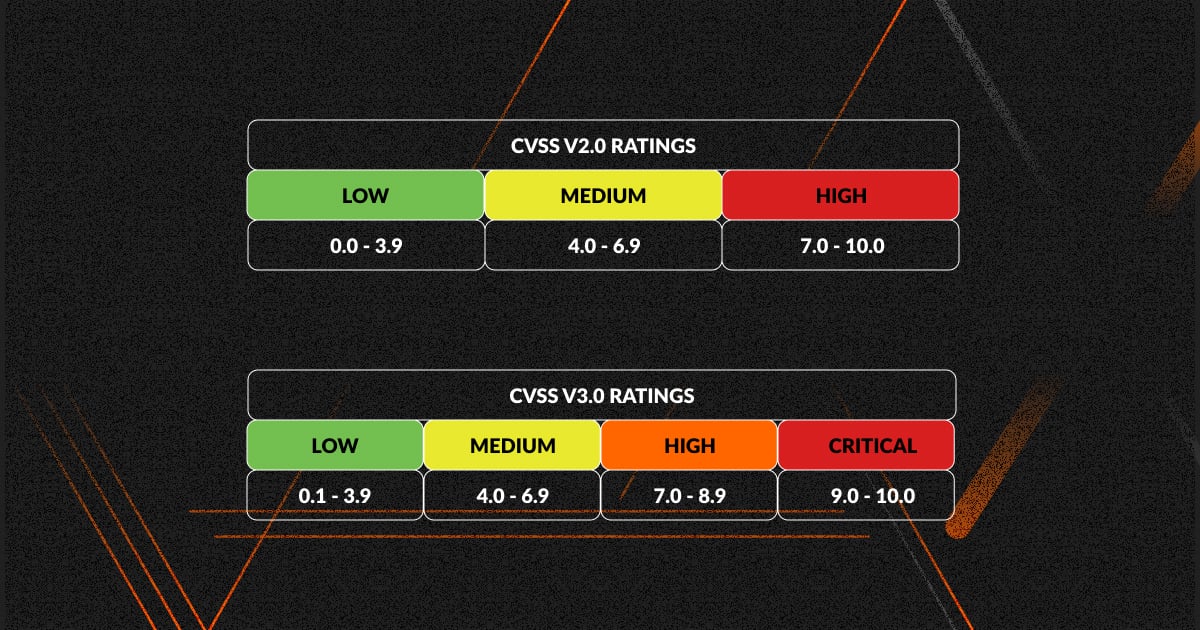
The qualitative ratings are considered to be an efficient tool that specifies the level of vulnerability severity when speaking in less technical terms. Thus, FIRST developed a scoring system that maps the CVSS scores with their corresponding qualitative ratings, as shown in the table below:
How is the scoring done?
In order to define the degree of harm that a vulnerability can cause to a system, we need to define the level to which a resource is unprotected, and how easily those vulnerabilities can be taken advantage of by an attacker. CVSS scoring is considered to be the framework that serves users as a measurement system to categorize the severity of the threat. A fast and easy way to do the scoring is by utilizing the NVD CVSS Calculator, which provides a personalized score, taking into consideration both impact and exploitability.
CVSS Score Rating
After calculating the score from the company’s infosec group or VTM, the most important thing is to match it with the level of the threat’s importance. Thus, if it is high or basic, organizations can understand the degree of impact that these weaknesses may have on their functionality. As an example, if a company uses a server that stores non-confidential information, and the infosec team spots various exploits or vulnerabilities, this can lead to a high CVSS score. However, since the information is not sensitive, those weaknesses do not have a high risk for the company.
The tables below present the rating systems of two different editions of CVSS:
What is the difference between CVSS and CVE?
In the digital world, CVE stands for Common Vulnerabilities and Exposures. This represents a special identifier that helps organizations classify each vulnerability in a unique way. The CVE helps infosec teams to quickly estimate the severity of the vulnerability, by advising the NIST National Vulnerability Database. If you want to learn some more details about CVE, check out the video below.
There is a great difference between CVE and CVSS since the latter does not represent a classification system. Moreover, the CVE has a special format that consists of the letters CVE, a four-digit year, and a sequential identifier. The final form looks like this:
CVE-[4-Digit Year]-[Sequential Identifier]
However, despite the fact that CVSS and CVE are not the same things, they are connected to each other. The latter utilizes the former in order to highlight the severity of vulnerabilities. Moreover, the qualitative metrics that were set by FIRST and are used as a CVSS score correspond to a different CVE vulnerability.
How do organizations adopt and use the CVSS?
The fast-growing development of network technology has led many organizations to enter this sector in order to take advantage of its various benefits. However, step by step, specialists started to understand the security problems that were appearing and the need for the organizations to categorize those issues in order to prioritize which they should tackle first.
In the beginning, each organization developed its own way to estimate the level of threat, but each method was deficient and could not define specific details about how the scores were calculated. Thus, the NIAC developed the CVSS in order to categorize and prioritize each vulnerability.
The CVSS is commonly used by organizations to measure the level of impact that a vulnerability may have on a specific IT environment. The main thing that makes the CVSS very useful and easy to understand is its open-source nature, which helps companies to use the same scoring tactics in order to develop their ratings. This way they can share and understand the differences of the vulnerabilities among each other.
Organizations that use the CVSS can develop numerous safety measures, so they will be able to confront the impact of the exploitation of vulnerabilities, as well as to meet the requirements in order to conform with several security standards. These are some of the reasons why most organizations use the CVSS.
Limitations of CVSS
Despite the various benefits that the CVSS has to offer, there are also some drawbacks that need to be mentioned. The CVSS is a measuring system that represents how serious a vulnerability in an organization's system is. However, it does not show the true risk of this weakness and how it may influence the company’s environment.
The growing number of vulnerabilities, in combination with the fact that only the Basic metrics of the CVSS are available to the public, raises serious issues when facing cybersecurity threats. Thus, the need for the temporal and environmental factors to also be made accessible to the public is now more crucial than ever. However, FIRST only provided the CVSS framework in order to define the severity of the weakness, and cannot assist organizations in connecting those metrics with each of the previous factors. This is a procedure done by an organization's security team, which needs to be highly qualified and have a deep understanding of the criticality of the various business assets, as well as the exploitability of the vulnerability in reality.
How vulners can help with vulnerability database

Vulners is a company specializing in information security in various sectors, including IT, payments systems, and more. Its main goal is to provide access to a rich database of software vulnerabilities, this way making the process of working with security data more efficient.
Apart from a robust database, Vulners comes with some other valuable tools, such as
- Linux security scanner
- API integration
- Subscriptions
- Manual audit
- Plugins
By implementing this intuitively designed, user-friendly platform, you can:
- Get access to up-to-date security intelligence feeds;
- Check your Linux system for vulnerabilities;
- Develop a secure product customized to your needs using Vulners SDK.
All you need to do is sign up, choose your pricing plan, and enjoy the benefits of this easy-to-use vulnerability database. Note that Vulners offers a 30-day trial period, so you can get accustomed to its features and capabilities.
Conclusion
CVSS has become one of the most critical tools that are widely used by organizations in order to protect their assets and systems. Its main purpose is to detect and specify the severity of a system’s weaknesses and help security teams to prioritize the threats depending on their significance. Despite the fact that the CVSS does not take into consideration all the real-world challenges and factors, it helps companies to have a starting point in their efforts to strengthen their security. Thus, combining an effective CVSS score with an efficient and robust security plan helps companies focus on the threats that are most severe, and find quick ways to boost their remediation efforts.
FAQ
What is the purpose of the CVSS?
There are various ways that an organization can measure the impact that vulnerabilities may have. One of these tools is the Common Vulnerability Scoring System (CVSS), whose main purpose is to evaluate a vulnerability and categorize it depending on its level of severity. The score that results is known as the CVE score.
What is the difference between CVSS V2 and V3?
Due to the constant effort of the FIRST development team to upgrade the functionality and effectiveness of the CVSS scoring system, they have proceeded to various upgrades, namely, V2 and V3. The key difference between the two versions is that the metrics of availability, confidentiality, and integrity were changed by adding the Low, High, and None levels. Moreover, a new metric was added to the physical value known as the Attack vector, and User Interaction was also implemented.
What is a CVSS Score of 10?
For an organization to define the level of the threat that its systems may face, they assign their infosec team to measure the CVSS score. The range can be from 0 to 10, depending on the severity of the threat. The lower the score, the less risky the vulnerability is for the company. Thus, a score of 10 shows that the detected weakness can pose a critical threat to the organization.
What do CVSS Scores mean?
A CVSS score is based on a three-metric system that consists of the base, metrical and environmental characteristics. It is an open and free standard framework that helps organizations to define the level of threat that a vulnerability can pose for the security of a computer system. This way, companies can prioritize their responses according to the severity of the threat.
