Monthly red digest with red vulnerabilities and incidents
Microsoft is the headliner of the outgoing month. Too many too critical vulnerabilities in the last month. Also, other vendors with zero-day and 1-click vulnerabilities are worth noting. In addition to vulnerabilities, there were several high-profile hacks and news about ransomware + some APT for our monthly digest.
Vulnerabilities: Microsoft, IOT, Nvidia, Atlassian, Western Digital and others;
Tools: MacHound, Gdir, Gorsair, Typodetect;
News: Ransomware, APT, data leaks and GitHub project;
Research: Usefull staff.
Feedback and Vulners docs
Vulnerabilities
PrintNightmare
Sangfor has published a PoC exploit that implements the PrintNightmare vulnerability in the Windows Print Spooler. PoC was originally supposed to implement the CVE-2021-1675 vulnerability closed by Microsoft in June. But it turned out that this is a completely new vulnerability CVE-2021-34527, allowing an attacker to take full control of the attacked system. To avoid attack, we recommend that you disable the Windows Print Spooler service (spoolsv.exe) on domain controllers and non-printing hosts.
PrintNightmare meme
You can find a bunch of videos of the vulnerability exploitation and relevant news in the Vulners database.
Millions of Internet-connected CCTV cameras are vulnerable to video interception
CISA has issued an advisory warning IoT manufacturers of a critical vulnerability - CVE-2021-32934 / CVSS score: 9.1 - in ThroughTek's P2P SDK that could be exploited by attackers to eavesdrop on connected cameras.
The problem affects the ThroughTek component from a third-party manufacturer used in the software of some CCTV cameras. The same component is also used by a number of IoT device manufacturers: baby monitor, pet devices, etc. The ThroughTek component is a peer-to-peer (P2P) software development kit (SDK) that provides access to video and audio streams over the Internet.
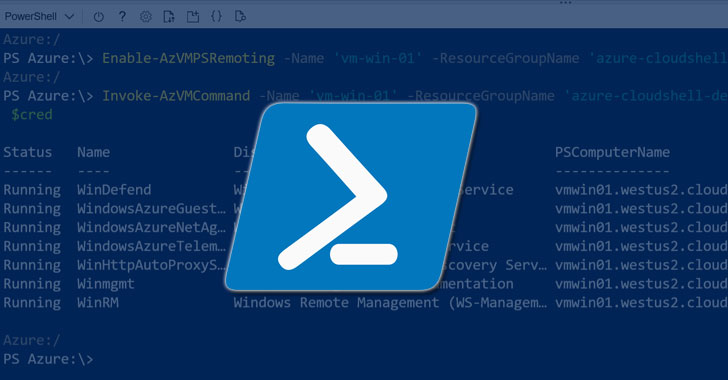
Microsoft has warned of a critical vulnerability in PowerShell 7 that allows RCE (remote code execution). The problem exists due to incorrect text encoding in .NET 5 and .NET Core. There are currently no effective measures to stop the exploitation of this gap. To protect systems from cyberattacks, customers are encouraged to install PowerShell versions 7.0.6 and 7.1.3 as soon as possible.
Any application using vulnerable versions of System.Text.Encodings.Web is open to cyber attacks. These versions, according to the published information, are from 4.0.0 to 4.5.0, from 4.6.0 to 4.7.1, and 5.0.0.

Check Point discovered vulnerabilities in Atlassian, a software development and project management platform used by 180,000 customers worldwide. The vulnerabilities could hijack Atlassian accounts as well as access source code hosted on Bitbucket.
Researchers demonstrated 1-click exploit for Atlassian's project and software development platform that could potentially be exploited to take over an account and control apps connected via SSO functionality.

NVIDIA releases update 3.23 for GeForce Experience
The update fixed CVE-2021-1073 with a CVSS severity rating of 8.3. An attacker using a malicious link could intercept the session token, thereby gaining access to user information. The severity of the vulnerability has been reduced as the victim must follow the malicious link on his own, which complicates the intended attack.
GeForce Experience is installed by default with all NVIDIA cards.
Microsoft Edge vulnerability CVE-2021-34506
CVE-2021-34506 is a Universal Cross-Site Scripting (UXSS) vulnerability related to automatic translation of web pages using a built-in browser feature via Microsoft Translator.
CyberXplore provided PoC exploit
UXSS differs from XSS attacks in that in the case of universal cross-site scripting, vulnerabilities in the browser (or in browser extensions) are exploited on the client side. The main goal of an attacker in this case is to execute malicious code.
Microsoft has fixed the vulnerability in browser version 91.0.864.59.

WD My Book Live Devices Wipe Through Zero-Day Vulnerability
Western Digital NAS has been attacked, which has wiped all files from the devices and made it impossible for users to log in through a browser or application, receiving an "Invalid Password" error.
Western Digital reported that the devices could have been compromised using some kind of vulnerability because they were connected to the Internet directly. At the same time, the last firmware update for WD My Book Live was released in 2015, and after that a critical bug CVE-2018-18472 was discovered for which an exploit immediately appeared.
Western Digital representatives have already announced that the company will provide data recovery services to all victims.
Tools

Typodetect tool gives blue teams, SOC’s, researchers and companies the ability to detect the active mutations of their domains, thus preventing the use of these domains in fraudulent activities, such as phishing and smishing.
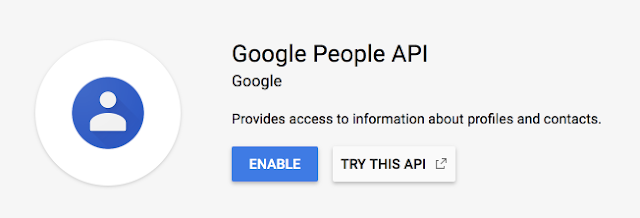
GDir-Thief is a tool for exfiltrating the target organization’s Google People Directory that you have access to, via Google’s People API.

Gorsair is a penetration testing tool for discovering and remotely accessing Docker APIs from vulnerable Docker containers. Once it has access to the docker daemon, you can use Gorsair to directly execute commands on remote containers.

MacHound is an extension to the Bloodhound audting tool allowing collecting and ingesting of Active Directory relationships on MacOS hosts.
News

Electronic Arts knew about critical vulnerabilities before the attack, but did nothing
The data leak revealed by the American video game publisher Electronic Arts this month could be much more serious than previously thought. This is not about the scale of the incident, but about the fact that a company can easily ignore the security threats that it knows about and not prevent cyberattacks.
A few weeks ago, reports began to appear on hacker forums about the theft from Electronic Arts of about 780 GB of source code, proprietary frameworks, development tools (SDK) and engines. All stolen data, including access to FIFA 21 servers, FIFA 22 API keys and some SDKs for Microsoft Xbox and Sony, have been put up for sale.

Microsoft mistakenly signed malicious Netfilter drivers
Microsoft admitted that it mistakenly signed and approved a series of Netfilter drivers, which turned out to be a Windows rootkit. The Netfilter drivers contained malicious functionality that would configure a proxy configuration on an infected host and then wait for commands from the C&C infrastructure located in China.
Microsoft said it had already blocked the vendor account through which the driver was sent for signing to the WHCP program, and also checked other drivers for that account for malware.
Security researcher Kevin Beaumont discovered that someone had downloaded Babuk Locker ransomware on VirusTotal. After the constructor got into the network, an intruder started using it in attacks on ordinary users. The hacker uses Tutanota's email address and demands a $ 210 ransom. We would like to note that the creators of Babuk Locker announced the termination of operations with ransomware after a high-profile attack on the Washington police department.

GitHub Copilot
GitHub introduced the GitHub Copilot project, which develops an intelligent assistant capable of generating generic constructs when writing code. The system was developed in cooperation with the OpenAI project and uses the OpenAI Codex machine learning platform, trained on a large array of source codes hosted in public GitHub repositories.

Hacking Kaseya software by the REvil ransomware
Researchers from the Dutch University of Vulnerability Disclosure (DIVD) reported that Kaseya was in the process of fixing the 0-day vulnerability CVE-2021-30116, which the researchers found several weeks before the incident. No technical details were provided by DIVD, but there was information on the network that exploiting the hole leads to bypassing authentication in the VSA web interface. How information about CVE-2021-30116 got into the hands of the ransomware - no one reports.
REvil has confirmed that it is they, claims that more than 1 million computers are encrypted, and is demanding a ransom of $ 70 million in bitcoins, promising to publish a decryptor.

APT IndigoZebra
Check Point has detected an ongoing phishing campaign targeting the Afghan government. Further investigation revealed that the attackers also targeted Kyrgyzstan and Uzbekistan. The suspect in the cyber espionage operation is APT IndigoZebra, which the researchers associate with China. The infection was carried out using phishing emails, the attachment of which contained a dropper that installed the BoxCaon backdoor. In addition, it is known that in the attack on the Afghan government, Dropbox was used as the command server, which made it difficult to detect the attackers.
Research
https://m0chan.github.io/2019/07/30/Windows-Notes-and-Cheatsheet.html
Demystifying the full attack chain of MineBridge RAT: https://www.zscaler.com/blogs/security-research/demystifying-full-attack-chain-minebridge-rat
REvil’s new Linux version: https://cybersecurity.att.com/blogs/labs-research/revils-new-linux-version
Complete Arsenal of Memory injection and other techniques for red-teaming in Windows: https://github.com/0xDivyanshu/Injector
Understanding & Detecting C2 Frameworks — DarkFinger-C2: https://nasbench.medium.com/understanding-detecting-c2-frameworks-darkfinger-c2-539c79282a1c
Feedback
-detecting-c2-frameworks-darkfinger-c2-539c79282a1c](https://nasbench.medium.com/understanding-detecting-c2-frameworks-darkfinger-c2-539c79282a1c)
