Vulners weekly digest #7

+1 integration for Vulners: 
Old and fresh vulnerabilities
Tools
Various news
This week Vullners integrated with data about Apple vulnerabilities!
Already available at Vulners DB: https://vulners.com/search?query=type:apple
Vulnerabilities
Update news on vulnerabilities from our latest digest and sth new!
Gitlab exploit
Automation to exploit one of the latest vulnerabilities in gitlab. Of course, it's possible to exploit it without it, but it's always nice when automation for such exploitation appears.
Latest news about Saltstack
Continuation of the story that f-secure started. The first affected mobile operating system is LineageOS. Then a large blogging platform Ghost, with more than 750 thousand users. Then Digicert, Xen Orchestra and a number of small companies followed.
The exploit, which uses the vulnerabilities identified By f-Secure in Salt, was published on GitHub by several users at once and the metasploit module is also on the way:
Full detailed timeline and other info about saltstack vulnerabilities: https://saltexploit.com
https://vulners.com/threatpost/THREATPOST:A1F6C89E2D2F2205B93C6727C24B908C
Trixbox CVE-2020-7351
Trixbox is open-source system for deployment VoIP (asterisk inside). Vulnerability in Trixbox version 1.2.0 to 2.8.0.4 inclusive in the “network” POST parameter of the “/maint/modules/endpointcfg/endpoint_devicemap.php” page. Successful exploitation allows for arbitrary command execution on the main operating system as the “asterisk” user.
SharePoint CVE-2020-0932 RCE
Microsoft in their last "The second Tuesday patch" announced fix for six vulnerabilities in SharePoint. There is no indication from the vendor why some of these vulnerabilities are rated as important, while others are rated as critical.
The most detailed write-up with great PoC: https://www.thezdi.com/blog/2020/4/28/cve-2020-0932-remote-code-execution-on-microsoft-sharepoint-using-typeconverters
SharePoint is used by many companies and accordingly attackers in their work, so you should not postpone updating your SharePoint servers.
Tools
Socks Over RDP: https://github.com/nccgroup/SocksOverRDP
"As penetration testers we frequently find ourselves in a situation where the only access that we are provided to a server or network is a Remote Desktop account. These servers are commonly called Jump boxes. It means that we need to perform our testing via this server. This usually introduces a few extra steps that takes time from us and our clients to setup and configure."
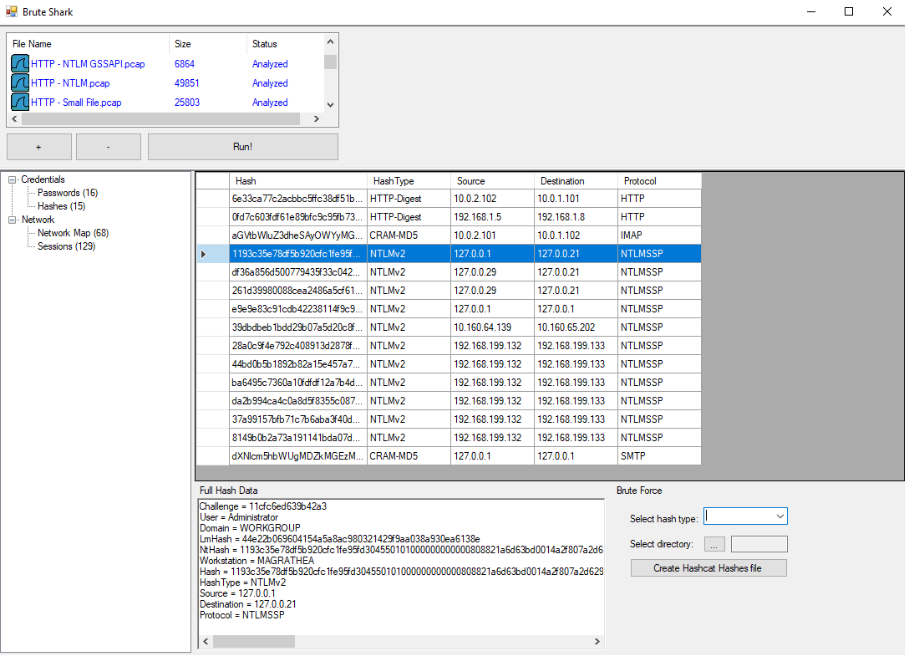
Brute Shark: https://github.com/odedshimon/BruteShark**
**Network Forensic Analysis Tool with usefull GUI and interesting functions. It includes: password extracting, building a network map, reconstruct TCP sessions, extract hashes of encrypted passwords and even convert them to a Hashcat format in order to perform an offline Brute Force attack.
Two BruteShark versions are available, A GUI based application (Windows) and a Command Line Interface tool (Windows and Linux).
Shellerator
This project is inspired by Print-My-Shel, which we cpecified in our previous weekly digest.
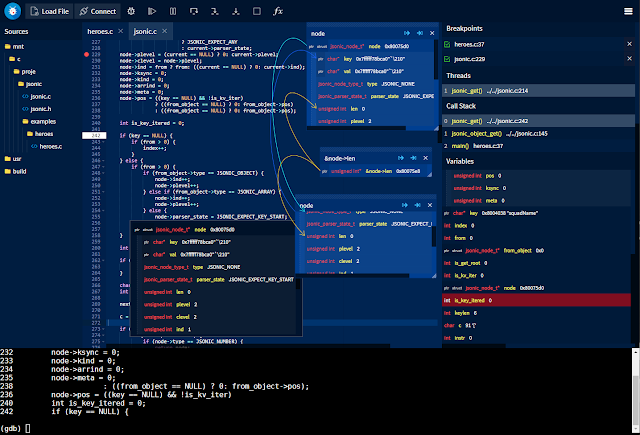
GDBFrontend
GDBFrontend is an easy, flexible and extensionable gui debugger.
Article: https://oguzhaneroglu.com/projects/gdb-frontend/
News
Conferences :(
Microsoft :)
APT :|
Major Cybersecurity Conferences
Black Hat USA and DEFCON 28 Cyber Security Conferences will not be held in person this year due to the coronavirus pandemic. Instead, both conferences will be transformed into fully virtualized events. Black Hat USA on Aug. 1 to 6, 2020, and DEF CON 28 on Aug. 7 to 9, 2020.
DEF CON remote events will include a new on-line Mystery Challenge, a DEF CON is Canceled music album, remote CTFs (including Hack-a-Sat, Villages like the Packet Hacking Village, contests like the TeleChallenge, and Ham Exams) and a remote movie night and drink-up, he said.
Black Hat USA will be adapted into a virtual format that will be available for the entire global infosec community. More details on how the virtual conferences:
https://vulners.com/threatpost/THREATPOST:4F7DA5B616227FD485369DAAEBE84656
Microsoft damn…

The hacker group Shiny Hunters reported to the editorial Board that they hacked Microsoft's GitHub account and got full access to the software company's private repository.
Shiny Hunter downloaded 500Gb of closed projects that they initially wanted to sell, but now decided to place on the network for free download. The hack itself appears to have occurred on March 28.
As a teaser, hackers posted 1Gb of stolen data on a closed forum, but not all forum users considered the posted information real. Microsoft employees also say that the leak is fake, but the company does not officially comment.
https://vulners.com/threatpost/THREATPOST:810608E8FBF789E16FA78CF73EDD7EB2
APT Naikon

Check Point has released a report, which reported on the recent disclosure of a long-running and large-scale cyber operation involving the use of the new Aria-body backdoor and directed at public authorities in the Asia-Pacific region, including Australia, Indonesia, the Philippines, Vietnam, Thailand, Myanmar and Brunei. The company has been running since at least 2018, and most likely since 2017.
Based on the analysis of the Aria-body functionality, Check Point concludes that the main purpose of cyber operations is to gather intelligence. This includes not only hunting for documents that hackers are interested in, but also extracting data from removable media, recording screenshots, and keylogging.
Analysis of the Aria-body code revealed sufficient similarity with the XsFunction backdoor code, which, along with a partial intersection of the infrastructure of control centers, allowed us to talk about the involvement of the Chinese APT Naikon aka APT 30 and Override Panda in the new cyber operation. There has been no news about APT Naikon since 2015. The group has previously worked actively against countries bordering the South China sea.
Overview of the research: https://vulners.com/threatpost/THREATPOST:96934F347B55F85990962035EF6F658D
Technical details with IOCs: https://vulners.com/securelist/SECURELIST:C96E2BC7AC745F58E5C3916C0AD13B0B
