
New vulnersBot for Telegram with advanced searches and subscriptions
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
0.973 High
EPSS
Percentile
99.8%
Vulners.com team have recently presented a new version of vulnerability intelligence bot for Telegram messenger. Now you can search for vulnerabilities and other security content by talking with bot.
Searches
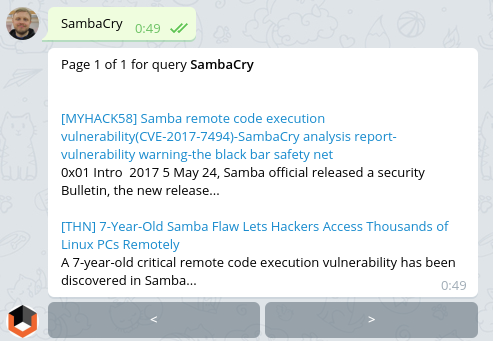
For example, I’ve heard about new critical vulnerability in Samba called SambaCry by analogy with famous WannaCry. Let’s see what Vulners knows about it.
Ok, I see it has id CVE-2017-7494. Do we have exploits related to this vulnerability?
_ cvelist:CVE-2017-7494 AND bulletinFamily:“exploit”_
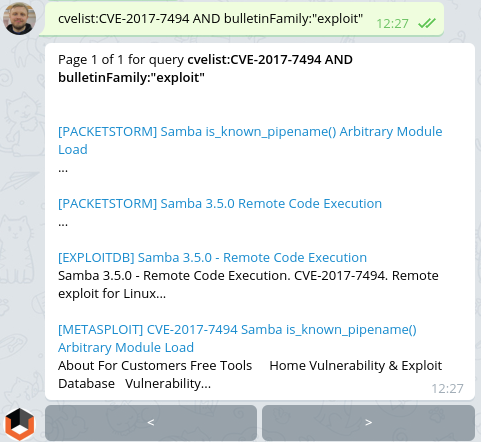
Even in Metasploit! Seems to be critical. Do we already have patches for CentOS 6 and 7?
cvelist:CVE-2017-7494 AND type:centos
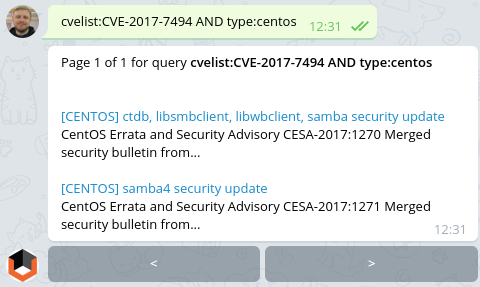
Yep, we can now make a task to IT department to update it.
NB: Did you know that critical patches for CentOS 5 were available till the March 31 2017? CentOS 5 is officially dead and if you still use it you should migrate to supported distribution ASAP.
Can we already detect this vulnerability using vulnerability scanners?
cvelist:CVE-2017-7494 AND bulletinFamily:“scanner” AND title:CentOS
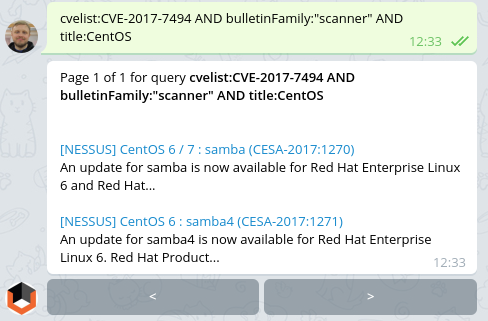
Two authenticated checks for Nessus. Not bad. If you have configured regular vulnerability scans of your infrastructure, you can get the list of vulnerable hosts from the existing scan results. Or you can perform a new scan task with only this two active plugins in the scan policy.
Subscriptions
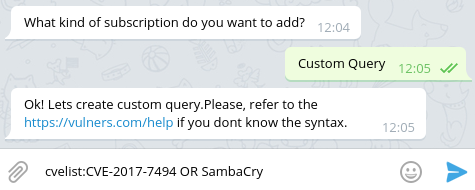
However, this vulnerability is interesting and I would like to get new information about it as soon as it will be available in Vulners. I want to subscribe to cvelist:CVE-2017-7494 OR SambaCry. Checking the request:
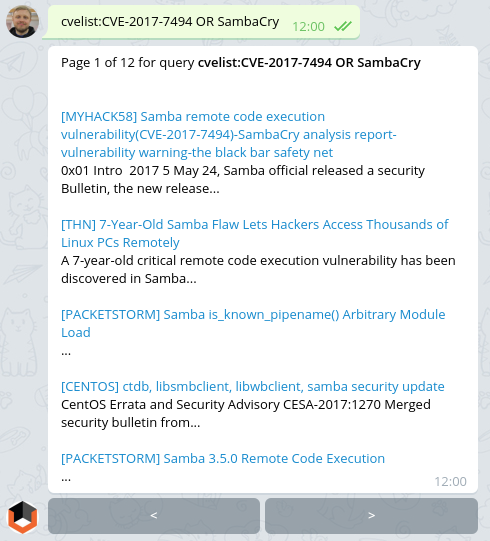
And making a new subscription. Available commands:
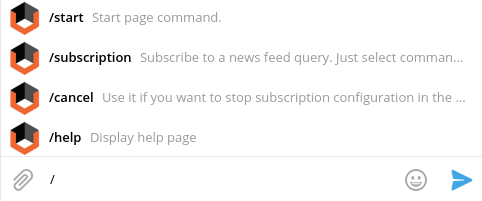
I choose /subscription
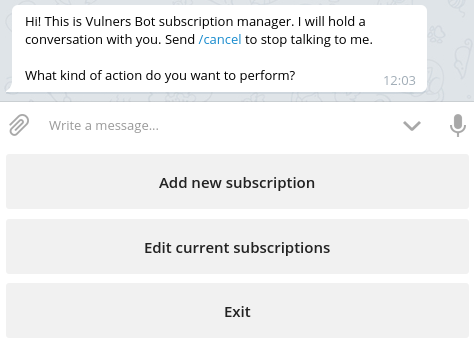
“Add new subscription”:
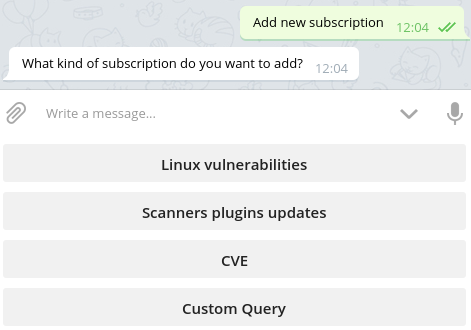
“Custom query”:
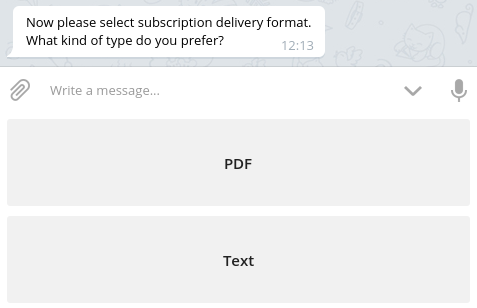
Subscription delivery format. I choose “Text”:
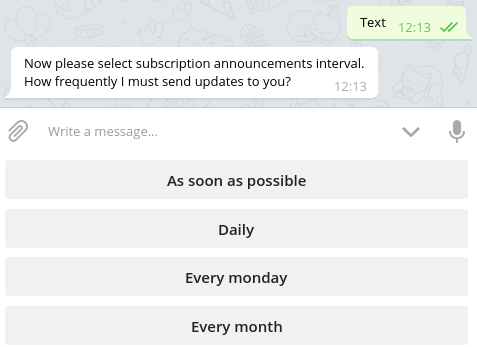
How often I would like to receive messages. “As soon as possible”:
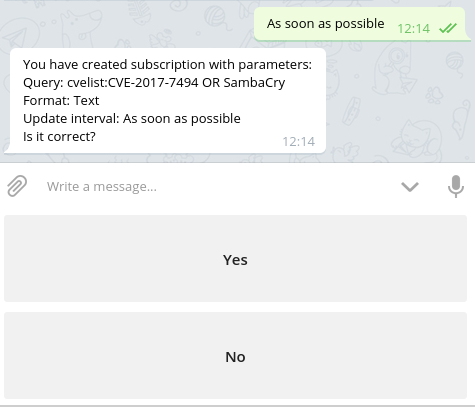
Approve the subscription:
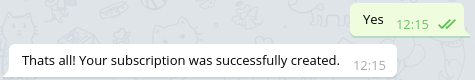
When Vulners will get a new object matched by this query, vulnersBot will send me a notification like this one:

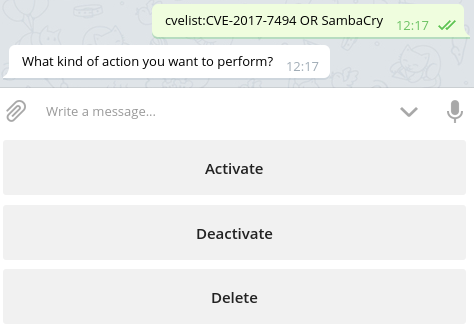
And if I would like to delete this subscription, I will write /subscription and choose “Edit current subscription”. Bot will show me my current subscriptions:
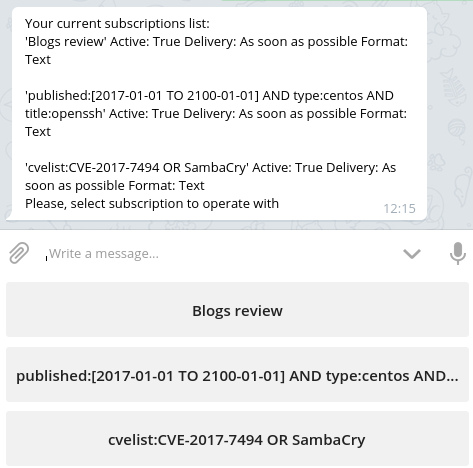
Each of them I can Activate, Deactivate or Delete:
As you can see, I have also a subscription “Blogs review”. It’s one of the standard templates that you can choose in vulnersBot. It is the same as bulletinFamily:blog
Vulners aggregates posts from 13 “blog” sources right now. This list includes top Vulnerability Management vendors Qualys and Rapid7, and WAF vendors Akamai, Imperva, Wallarm, well-known media and independent security bloggers. So if some really critical vulnerability will appear, I will easily get actual information from them.
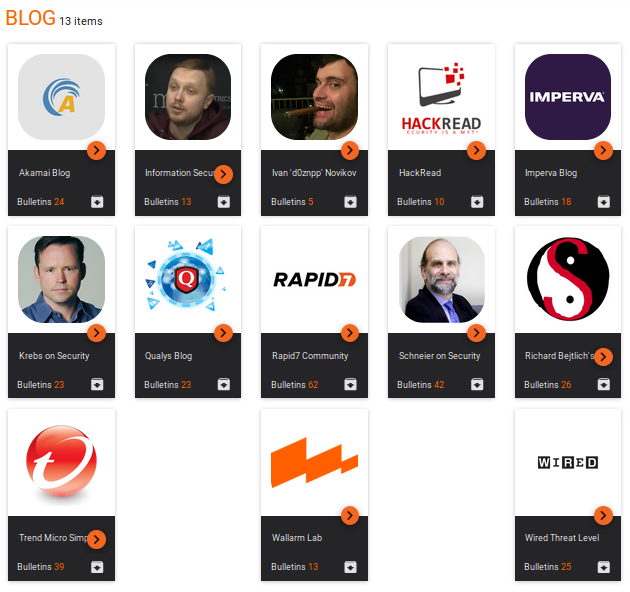
This templates are currently available in “subscription marketplace” :
- Security news
- Exploit updates
- Blogs review
- Bugbounty
- Linux vulnerabilities
- Scanners plugins updates
- CVE
Thanks for your attention! If you find a bug in vulnersBot please write an email to [email protected] or telegram user @isox_xx
9.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
NONE
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
10 High
CVSS2
Access Vector
NETWORK
Access Complexity
LOW
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:L/Au:N/C:C/I:C/A:C
0.973 High
EPSS
Percentile
99.8%