
Emergency patches have been released by Microsoft for PrintNightmare
8.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C
THREAT LEVEL: Red.
For a detailed advisory, download the pdf file here.
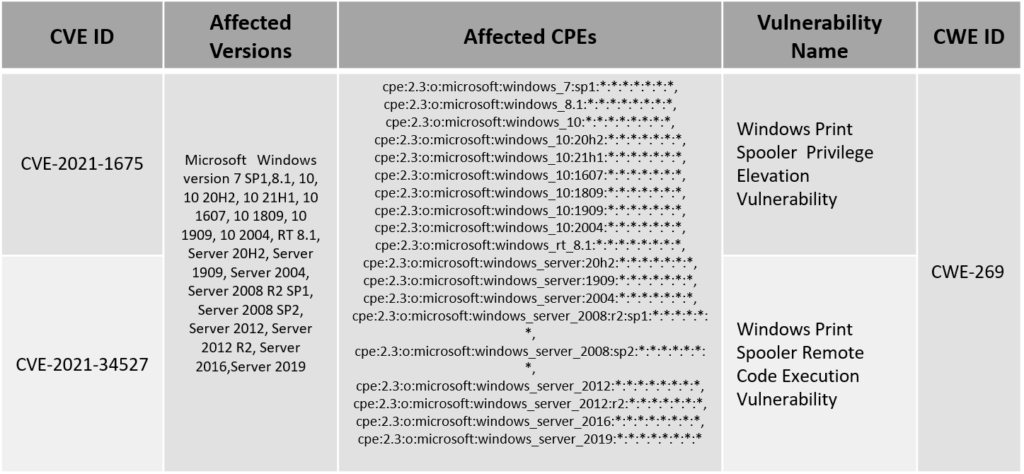
Attackers have been targeting Windows Print Spooler services for almost 2 months now. It started with the vulnerability(CVE-2021-1675) being exploited in the wild. Soon a patch was released for the same. It was after 2 days that Microsoft found out that there exist another vulnerability which gives the attacker an access to execute a code in the victim’s system. This new vulnerability(CVE-2021-34527) has been named as PrintNightmare. An emergency patch has been released by Microsoft for some of the versions and a workflow as been made available for other versions.
Vulnerability Details
Patch Links
<https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-1675>
<https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-34527>
References
<https://securelist.com/quick-look-at-cve-2021-1675-cve-2021-34527-aka-printnightmare/103123/>
<https://www.kaspersky.com/blog/printnightmare-vulnerability/40520/>
8.8 High
CVSS3
Attack Vector
NETWORK
Attack Complexity
LOW
Privileges Required
NONE
User Interaction
REQUIRED
Scope
UNCHANGED
Confidentiality Impact
HIGH
Integrity Impact
HIGH
Availability Impact
HIGH
CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
9.3 High
CVSS2
Access Vector
NETWORK
Access Complexity
MEDIUM
Authentication
NONE
Confidentiality Impact
COMPLETE
Integrity Impact
COMPLETE
Availability Impact
COMPLETE
AV:N/AC:M/Au:N/C:C/I:C/A:C